Spyrtacus and the fake WhatsApp client behind a hidden surveillance campaign
In late March 2026, around 200 people in Italy received an unusual warning from WhatsApp. Their devices, according to the company, had been compromised through a fake client that looked like the real app but behaved like spyware.
Meta publicly linked the campaign to Asigint, a subsidiary of SIO S.p.A., a company active in lawful interception technologies for law enforcement and intelligence customers. Researchers identified the malware family name Spyrtacus in sample code, and public reporting indicates activity dating back to at least 2018.
This post focuses on what is currently documented and useful in practice, including capabilities, delivery mechanics, forensic traces, ATT&CK mapping, and investigative caveats.
If you work in incident response or mobile forensics, the key point up front is simple. Spyrtacus is less about technical novelty and more about operational effectiveness. The campaign appears to combine believable pretexts, trusted brands, and enough mobile control to extract high-value data without obvious user-visible anomalies.
Quick facts
| Field | Current public picture |
|---|---|
| Malware family | Spyrtacus |
| Reported operator ecosystem | SIO / ASIGINT (public attribution reporting) |
| Main lure model | Fake WhatsApp and carrier-themed app distribution |
| Delivery channel | Targeted social engineering, including telecom-branded pretexts |
| Known platform coverage | Android and Windows documented, iOS activity publicly reported |
| Victim scope disclosed by WhatsApp | Around 200 users, mostly in Italy |
| Public IOC completeness | Partial, behavior-rich but not hash/domain complete |
| Best detection strategy right now | Behavioral triage plus timeline reconstruction |
Who is behind Spyrtacus
Attribution in this case is unusually explicit. The vendor was named by Meta, and multiple public investigations connected infrastructure and product branding to Asigint and SIO. Reporting by Corriere della Sera and TechCrunch also tied the operation to the broader Italian lawful interception market.
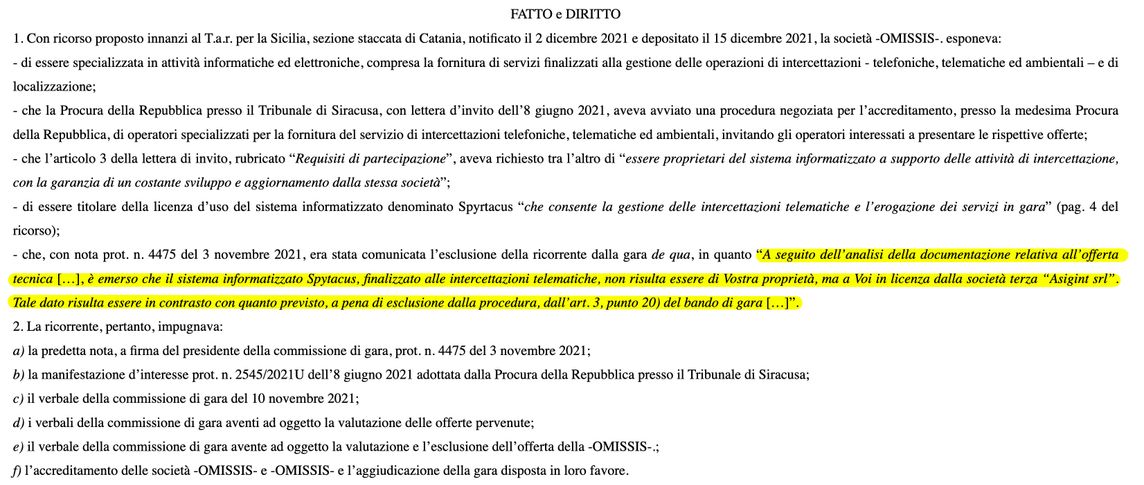
An additional element comes from DDay, which cites administrative procurement records connected to the Siracusa prosecutor office. In those records, the name “Spyrtacus” appears in relation to lawful interception tendering context, with references indicating software licensing through Asigint rather than direct ownership by the bidding company. This does not, by itself, prove specific operational deployments in each case, but it strengthens the picture of Spyrtacus as a product embedded in the Italian interception supply chain.
Italy is a special case in Europe because lawful trojans (captatori informatici) operate within a formal legal framework. That legal context does not remove technical risk for targets, nor does it remove the need for strong forensic standards when incidents are investigated.
How the spyware works
Public analyses describe Spyrtacus as a surveillance toolkit with multiple platform variants over time, including Android and Windows, and later campaign signals pointing to iOS targeting. The malware was also explicitly referenced in Kaspersky’s APT trends report Q1 2024, which noted historical distribution through fake provider-themed pages and signs of cross-platform expansion.
Documented and reported capabilities include the following.
- Collection of messages and communication metadata
- Access to contacts and call history
- Audio capture through device microphones
- Image or video collection through device cameras
- Location tracking and periodic device beaconing
On Android, the most recurrent operational pattern is app impersonation plus broad permission requests, often including high-risk privileges such as accessibility abuse and overlay rights. Those choices are typical in spyware operations that need persistence, UI control, and stealthy data collection.
How infections were delivered
The delivery chain appears to have relied heavily on targeted social engineering. Victims reportedly received messages that looked like legitimate carrier communications (for example TIM, Vodafone, or WINDTRE), then followed links to cloned pages where they were prompted to install malicious apps.
The same reporting line, reiterated by DDay and originally sourced to TechCrunch and Lookout analysis, describes a shift from earlier Play Store exposure to dedicated Italian-language distribution sites after Google detection hardening in 2022.
This is important for responders because user testimony and telecom metadata can become key evidence. In many cases, the malicious SMS may look ordinary at first glance, while the embedded URL, install source, and timing correlation reveal the compromise.
The campaign is also a reminder that social engineering can be as effective as zero-click exploitation when it piggybacks on trusted brands and institutions.
IOCs and forensic traces
Below is a practical shortlist based on public reporting and standard mobile triage workflows.
Confirmed indicators from published sources
The sources already cited in this article provide a few concrete and reusable indicators:
- Malware family name used in reporting and samples: Spyrtacus
- At least 13 Android samples observed by Lookout, with collection timeline from 2019 to October 2024
- Impersonated app themes repeatedly observed: WhatsApp, TIM, Vodafone, WINDTRE
- Delivery shift documented by Kaspersky: from Google Play-era distribution (2018) to fake provider-themed web pages (from 2019)
- Infrastructure-level attribution clue reported by TechCrunch and Lookout: C2 servers linked by registration metadata to ASIGINT and, in at least one case, to DataForense
These are not atomic IOCs in the strict SOC sense (for example exact hashes or IP lists), but they are high-confidence investigative pivots.
What to check first
| Priority | Check | Why it matters |
|---|---|---|
| High | Verify whether the messaging app was installed from an official channel | This quickly separates normal installs from likely malicious sideloading paths. |
| High | Reconstruct the infection window with SMS history, browser history, and install timestamps | The delivery chain is social-engineering-driven, so timeline correlation is often decisive. |
| Medium | Prioritize accessibility and device-management anomalies over static signatures | Public data is incomplete on hashes and C2, so behavioral pivots are more reliable. |
| Medium | Preserve volatile artefacts early before routine device updates remove context | Mobile telemetry is ephemeral and can be lost after updates or cleanup actions. |
If your team uses a case management platform, store these pivots as campaign tags so they can be correlated across incidents:
| Tag type | Suggested value |
|---|---|
| Theme | fake WhatsApp client / fake carrier support app |
| Geo-lingual context | Italian-language lure infrastructure |
| Cluster attribution (OSINT) | Spyrtacus cluster linked to SIO-ASIGINT ecosystem |
Android artefacts
| Artefact area | What to look for | Practical check |
|---|---|---|
| Package identity | Unexpected package names impersonating WhatsApp or carrier support apps | Compare installed package names with official app identifiers for the device region. |
| Install provenance | Non-Play installation sources for apps that should come from official stores | Validate installer source and sideload permissions in device settings and logs. |
| Accessibility abuse | Suspicious accessibility services enabled for non-accessibility apps | Review enabled services and cross-check with app purpose and publisher trust level. |
| Runtime behavior | Evidence of injected modules or suspicious behavior in communication app processes | Correlate process anomalies with user activity windows and network bursts. |
| Local config storage | Obfuscated keys or unusual shared preferences entries | Inspect preference files for opaque keys and frequent configuration rewrites. |
| Infection chain traces | User journey artefacts matching known chain (SMS lure -> cloned page -> sideload install) | Build a unified timeline from SMS, browser, and package installation events. |
iOS artefacts
| Artefact area | What to look for | Practical check |
|---|---|---|
| Provisioning profiles | Untrusted, expired, or anomalous profiles | Enumerate profiles and validate issuer, install date, and intended distribution scope. |
| Device management entries | Unexpected items under Settings > General > VPN & Device Management | Compare with known corporate MDM baselines and user-approved management records. |
| App distribution path | Installation events outside expected App Store or approved enterprise channels | Review installation history and cross-check with enterprise signing policy. |
| Social-engineering overlap | Timeline overlap with user-reported update prompts referencing WhatsApp | Align user report timestamps with install and profile changes to confirm causality. |
Network clues
| Signal | What to look for | Investigation action |
|---|---|---|
| Beaconing cadence | Regular encrypted callback intervals from suspicious mobile processes | Baseline normal app behavior and flag periodic outliers by process and destination. |
| Exfiltration timing | Traffic bursts after messaging activity | Correlate network spikes with app foreground events and message handling windows. |
| Infrastructure overlap | Domain and registration overlaps with previously reported infrastructure | Run WHOIS and passive DNS pivots against known registrant patterns and naming reuse. |
| Attribution enrichment | Links to entities named in open reporting (ASIGINT and related registrations) | Preserve registrar snapshots and hosting history as evidentiary supporting material. |
What public sources still do not provide
At the time of writing, open reports do not provide a complete public feed of:
- Sample hashes (SHA256) for all known variants
- Exhaustive package name list
- Full C2 domain and IP list
- Signing certificate fingerprints
For operational deployments, treat this case as behavior-led detection first, then enrich with private TI, mobile EDR telemetry, and legal process to obtain telecom and registrar records.
MITRE ATT&CK mapping
The table below maps the observed behavior to ATT&CK techniques.
| Technique ID | Technique | Why it fits this case | Investigation focus |
|---|---|---|---|
| T1444 | Masquerade as Legitimate Application | Fake clients impersonated WhatsApp and telecom-branded apps to gain trust. | Verify app identity, signing chain, and install provenance. |
| T1432 | Access Contact List | Public reporting describes collection of contacts and related metadata. | Compare app permissions with observed contact database access events. |
| T1412 | Capture SMS Messages | The spyware family is reported to collect SMS and messaging content. | Correlate suspicious process activity with message database access. |
| T1429 | Capture Audio | Reported capabilities include microphone-based ambient and call-adjacent recording. | Look for unauthorized microphone activation patterns and background recording artifacts. |
| T1512 | Capture Camera | Sources describe image and video capture through device cameras. | Inspect camera permission use, background camera sessions, and media staging paths. |
| T1430 | Location Tracking | Campaign reporting includes GPS/location collection for surveillance purposes. | Hunt for periodic geolocation requests tied to suspicious app components. |
| T1583.001 | Acquire Infrastructure: Domains | Infrastructure registration and domain ownership patterns were part of attribution. | Use WHOIS and passive DNS to pivot on linked registrant entities and hosting clusters. |
Why this case matters
The SIO and Spyrtacus case arrived shortly after the Paragon and Graphite controversy in Italy. The two models are different in both tradecraft and traceability.
- Paragon reporting focused on zero-click tradecraft
- Spyrtacus reporting highlights social engineering and fake app delivery
From a forensic perspective, this changes the evidence profile. Social engineering campaigns often leave richer, human-readable traces such as SMS content, browser history, sideload logs, and timeline anchors from user action.
From a policy perspective, the case sits at the intersection of lawful interception, platform defense, and accountability. Even where domestic legal authorization may exist, technical transparency, evidentiary rigor, and proportionality remain central questions.
For readers outside Italy, this case is still relevant. The same delivery pattern can be reused anywhere with local adaptations: different telecom branding, different legal wrappers, same human trust exploit.
Detection gaps to close
The current public picture is useful, but still incomplete. These are the five gaps that usually have the highest operational impact.
| Priority | Gap | Why it is a risk | Action to close it |
|---|---|---|---|
| 1 | Missing atomic IOCs (hashes, certs, full C2 list) | Signature-only detection remains weak and easy to bypass. | Build behavior-led detections and continuously enrich with private TI feeds. |
| 2 | Limited mobile install provenance telemetry | Sideloading and profile abuse may be discovered too late. | Expand EDR and MDM logging on installer source, profile changes, and app signing data. |
| 3 | Weak SMS and browser timeline correlation | The social-engineering chain can remain fragmented across tools. | Standardize timeline reconstruction playbooks that merge SMS, browser, and install events. |
| 4 | Incomplete registrar and passive-DNS enrichment | Attribution pivots may be missed in early triage. | Automate WHOIS and passive-DNS enrichment for suspicious mobile-related domains. |
| 5 | Legal and forensic workflow misalignment | Volatile evidence may be lost before authorization and preservation steps complete. | Pre-approve emergency preservation procedures and legal escalation paths for mobile cases. |
Final notes for investigators
Three points are worth keeping in mind while this campaign is still being clarified.
- Treat every claim as time-bounded. Public reporting can evolve quickly.
- Preserve first, interpret second. Mobile artefacts are volatile and easy to lose.
- Separate technical findings from legal conclusions in your reporting workflow.
Spyrtacus is not just another malware label. It is a concrete example of how surveillance tooling, social engineering, and institutional trust can collide in the same operation.
References and further reading