Fileless Malware for Dummies
Just some random thoughts about this kind of threat
Some days ago, a non-technical friend asked me some informations about ‘fileless malware’.
Has been pretty difficult to explain this concept to a person lacking a correct security knowledge, so i have make a recap of this talk in a brief article “4Dummies”.
What is fileless malware?
Fileless malware are malicious programs that don’t use any files in the process.
To understand their name, we need is a quick recap of how traditional antivirus work:
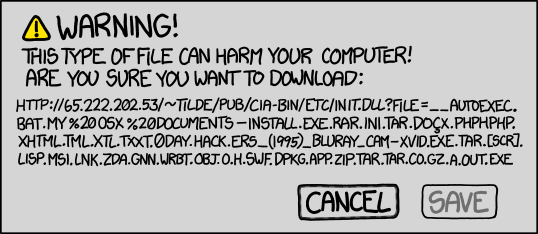
- The infection places files on the hard drive
- The antivirus analyzes the malicious files
- If identified, the antivirus removes the malicious files
In case of fileless infections no files are dropped onto the system, so traditional antivirus products can’t identify this infection.
Infections are defined as an Advanced Volatile Threat (AVT) that can persist in the infected machine’s memory, the registry, or combined with additional payloads for more targeted attacks in the future, such as inclusion as part of a group’s botnet, and can be grouped into this categories:
1.Memory-resident malwaree: this type of malware makes use of the memory space of a process or an authentic Windows file. It loads its malicious code into that memory space and stays there until it’s triggered.
-
Rootkits: this kind of malware reside in the kernel, thus persisting in spite of restarts and usual antivirus scans. Its ability to hide itself can make removal be really difficult.
-
Windows registry malware: The Windows Registry is a database that stores low-level settings for the operating system and certain apps. It’s a difficult place to navigate as a normal user. But malware authors have even exploited the OS’s thumbnail cache to gain persistence: the malware writes the complete payload file in an encrypted form in the Windows registry hive and set the system to delete it once the attack is executed
How to protect against infections?
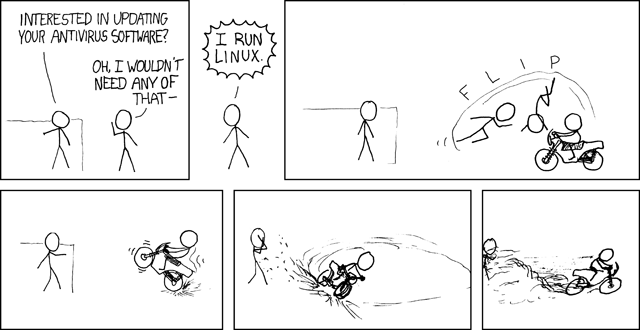
Due to the difficult detection of this kind of malicious programs, traditional antivirus can fail.
So, it’s important to strongly apply the standard security rules:
- Apply all the latest Windows Updates ( especially the security updates!).
- Make sure that all installed software is patched and updated to latest versions.
- Use a security product with the ability to scan memory and also block malicious web pages that may be hosting exploitkits.
- Be careful before downloading any email attachments.
- Use a firewall that lets you effectively control network traffic.
References
- Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software
- The History of Fileless Malware - Looking Beyond the Buzzword
- Fileless Malware Explained
- Understanding Fileless Malware Infections - The Full Guide