Analysing Active Directory event logs to identify compromised accounts
During investigation in a security incident, event log analysis is a key element.
If the affected network is managed by Active Directory, identify compromised accounts is a critical step.
For such investigation, because is quite difficult to conduct detailed analysis in AD event viewer, it is rather common to export the logs to text format or import them into a SIEM.
However, since the amount of event logs can be massive depending on the environment, this can be a big challenge for analysts.
Luckily, JPCERT/CC has developed LogonTracer, a tool which supports such event log analysis, associating a hostname/IP and account name founds in logon-related events and displaying it as a graph, like this:
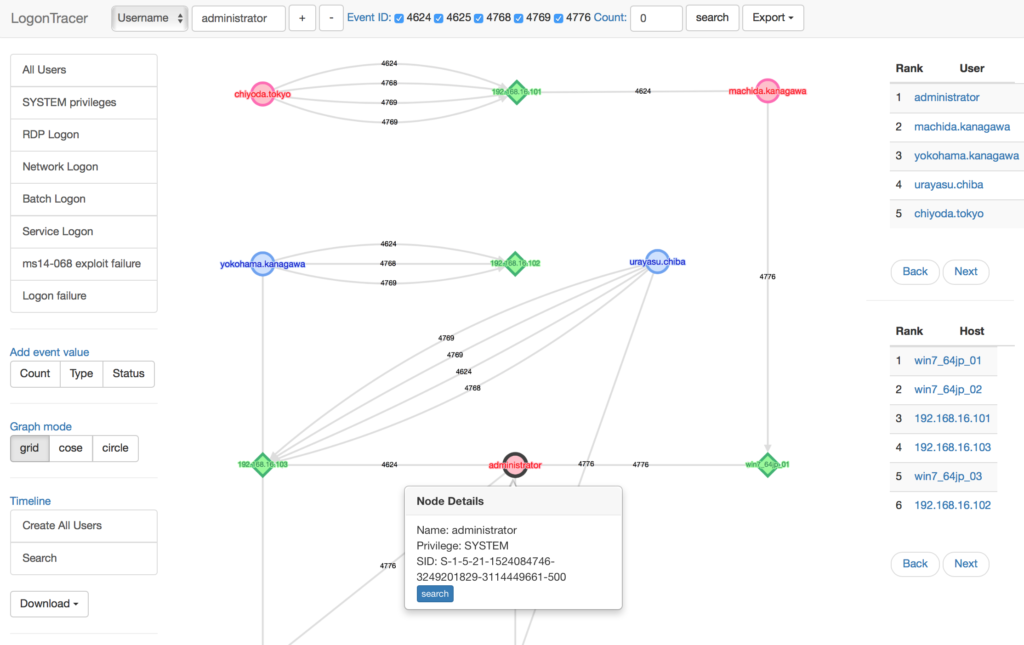
This graph allows the analyst to simply see in which account login attempt occurs and which host is used.
The tool can visualize the following event IDs related to Windows logon:
4624: Successful logon
4625: Logon failure
4768: Kerberos Authentication (TGT Request)
4769: Kerberos Service Ticket (ST Request)
4776: NTLM Authentication
4672: Assign special privileges
And is essentially based on this previous research by the same team: Detecting Lateral Movement through tracking Windows Events
LogonTracer also allows to display display event logs ordered by a chronological order or by a ranking, which is calculated performing network analysis on the event log graph, and creates a ranking based on the “centrality” of each node, an index which indicates each node’s proximity to the centre in a network.
Installation
The installation process is pretty simple.
Prior you need to satisfy some requirements, such as neo4j (needed for graph creation), then you can follow the procedure on the official documentation:
You can also use a preconfigured Docker image:
$ docker pull jpcertcc/docker-logontracer
$ docker run \
--detach \
--publish=7474:7474 --publish=7687:7687 --publish=8080:8080 \
-e LTHOSTNAME=[IP_Address] \
jpcertcc/docker-logontracer
And access to via Web browser.
References and further readings
- LogonTracer on GitHub
- Detecting Lateral Movement through tracking Windows Events