My Weekly RoundUp #80
A really bad week for application containers and secure email providers, and a sad news from Mars.
Cybersecurity
VFEmail suffers ‘catastrophic’ attack, as hacker wipes email service’s primary and backup data

Disaster. There’s no other word for it.
Customers of VFEmail, a Milwaukee-based email provider for businesses and end-users since 2001, has revealed that it has suffered a ‘catastrophic’ attack after a hacker breached its systems and wiped out all of the data it was storing on its US-based servers.
VFEmail Suffers Catastrophic Attack, All Data Lost
A major cyber-attack has hit email provider VFEmail in what the company is calling a "catastrophic attack," which has destroyed all data in the US, including backups.
The company issued an alert via its website and social media accounts on February 11, 2019, warning, “At this time I am unsure of the status of existing mail for US users. If you have your own email client, DO NOT TRY TO MAKE IT WORK. If you reconnect your client to your new mailbox, all your local mail will be lost.”
https://www.infosecurity-magazine.com/news/vfemail-suffers-catastrophic-attack/
RunC Flaw Lets Attackers Escape Linux Containers to Gain Root on Hosts

A serious security vulnerability has been discovered in the core runC container code that affects several open-source container management systems, potentially allowing attackers to escape Linux container and obtain unauthorized, root-level access to the host operating system.
The vulnerability, identified as CVE-2019-5736, was discovered by open source security researchers Adam Iwaniuk and Borys Popławski and publicly disclosed by Aleksa Sarai, a senior software engineer and runC maintainer at SUSE Linux GmbH on Monday.
The flaw resides in runC—a lightweight low-level command-line tool for spawning and running containers, an operating-system-level virtualization method for running multiple isolated systems on a host using a single kernel.
Container Escape Flaw Hits AWS, Google Cloud, Linux Distros
Introduced in 2015, runc is a lightweight, portable container runtime that includes all of the code used by Docker to interact with system features related to containers. The runtime is used in most containers out there, including cri-o, containerd, Kubernetes, Podman, and others.
Tracked as CVE-2019-5736 and featuring a CVSSv3 score of 7.2, the vulnerability can be exploited with minimal user interaction, senior software engineer at SUSE Linux and runc maintainer Aleksa Sarai says.
Discovered by Adam Iwaniuk and Borys Popławski, the vulnerability could allow a malicious container to overwrite the host runc binary and execute code on the host.
The bug can be triggered when creating a new container using an attacker-controlled image, or when attaching to a running container (using docker exec) that the attacker previously had write access to.
New Offensive USB Cable Allows Remote Attacks over WiFi
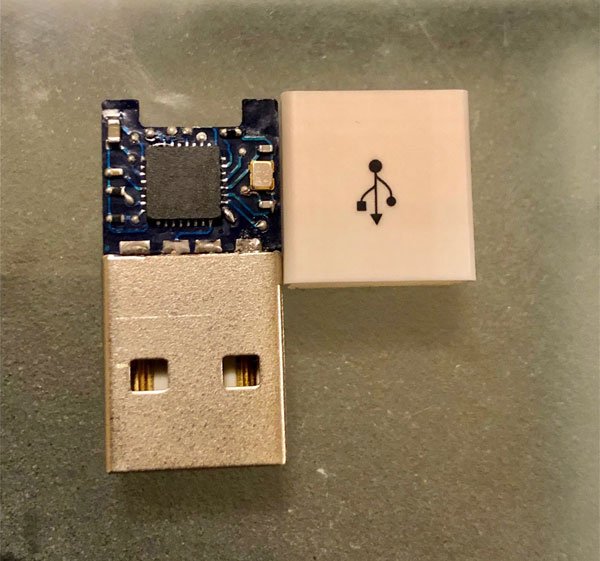
Like a scene from a James Bond or Mission Impossible movie, a new offensive USB cable plugged into a computer could allow attackers to execute commands over WiFi as if they were using the computer's keyboard.
When plugged into a Linux, Mac, or Windows computer, this cable is detected by the operating system as a HID or human interface device. As HID devices are considered input devices by an operating system, they can be used to input commands as if they are being typed on a keyboard.
Privacy
Man Uses GDPR to Find That Netflix Hoards All Your Bandersnatch Choices

Turns out Netflix has a big stash of all the choices everyone has ever made in Bandersnatch, including you (if you've watched it).
Tech policy researcher Michael Veale made a GDPR access request and found out exactly how much Netflix stores about your Bandersnatch choices and how the data is formatted, which is fascinating for us supernerds
Programming
Introduction to WebAssembly
Essentially, WebAssembly is a way to compile stuff to a browser-native binary format .wasm, which you can then load with JavaScript and interact with.
https://sensepost.com/blog/2018/introduction-to-webassembly/
Technology
Enough of the 5G Hype
Fifth Generation (5G) wireless represents a more efficient way to manage wireless services through “network slicing,” which prevents multiple wireless networks from interfering with each other. Under previous wireless specifications, operators generally competed for the same network resources, but “slices” can operate as their own independent networks without cannibalizing one another. This allows for tailored wireless services for the Internet of Things, autonomous vehicles, broadband Internet access, and other services that have different needs.
NASA is saying goodbye to its Opportunity rover on Mars after eight months of radio silence
Goodbye, little guy.

Opportunity has been radio silent since June 2018 when a massive dust storm overwhelmed the skies of Mars and blotted out the Sun. The storm, one of the thickest NASA has ever seen, made it impossible for Opportunity’s solar panels to stay powered. As a result, the rover’s internal battery drained, and Opportunity went into hibernation mode.
After the storm passed, the mission team for Opportunity was hopeful that they might be able to wake the rover up again. They figured that once light hit Opportunity’s solar panels again, it could get enough power to turn on and establish a radio link with Earth. But it’s been total silence since June 10th when the rover sent back its last message that indicated the environment on Mars was incredibly dark and that the bot’s battery was nearly depleted.
Entertainment
The 'Frozen 2' trailer is here!
Do you want to build a snowman? No? Well, then, how about a sequel to one of Disney Animation's most beloved recent hits?
It's been over five years since Anna, Elsa, Olaf, and Kristoff sang and danced their way into our hearts, but the gang are all back now for a second adventure.
We don't know whether we're more excited to see their faces again... or more scared of another "Let It Go"-level earworm. We just got that song out of our heads, guys
Music
Khatia Buniatishvili plays Piano Concerto No 2 by Sergej Rachmaninov
Mesmerizing...