My Weekly RoundUp #86 - What happened in the Article 13's Week?
Last week the European Union’s Copyright Directive was approved by the European Parliament in Strasbourg.
Here some interesting articles about this significant topic, but also more light news.
Technology
What is Article 13? The EU's copyright directive explained

Article 13 is the part of the new EU Copyright Directive that covers how "online content sharing services" should deal with copyright-protected content, such as television programmes and movies.
It refers to services that primarily exist to give the public access to "protected works or other protected subject-matter uploaded by its users", so it is likely to cover services such as YouTube, Dailymotion and Soundcloud.
However, there is also a long list of exemptions, including:
- non-profit online encyclopaedias
- open source software development platforms
- cloud storage services
- online marketplaces
- communication services
EU Parliament Approves Controversial Copyright Law

The European Parliament approved major new changes to EU-wide copyright laws which critics claim could lead to de facto mass censorship of online content.
Tech giants like Google and Amazon have been mobilizing their users for months to protest ahead of the vote, but in the end the Copyright in the Digital Single Market directive was voted in by 348 MEPs to 274.
Most controversial is Article 13, which requires sites and internet platforms to filter any user-generated content that is being uploaded without permission, or else be held liable for infringement. Although they already scan for unlicensed content, this will put a greater liability on such sites for doing so.https://www.infosecurity-magazine.com/news/eu-parliament-approves-1/
Today the European Union’s Copyright Directive was approved in a decisive vote by the European Parliament in Strasbourg.
Reacting to the vote in the European Parliament, Jim Killock, executive director of Open Rights Group said:
“This is a very bad day for free expression, for copyright and democracy. Millions of people have voiced their opposition and thousands have protested against it. If copyright filters go ahead, large numbers of mistaken takedowns will impact what we do and say online. The EU Parliament has made a serious error of judgement here. We will go on doing everything we can to stop this being the disaster it promises to be.”
https://www.youtube.com/watch?v=h8kQ3pu7lOs
Article 13 approved: What are the EU copyright law amendments?
A particular point of contention is Article 13, which, were it to come to fruition, would make platforms like YouTube liable for copyrighted material. As such, platforms would require agreements with content producers (or whoever owns the rights to the music, film or television being shared).
YouTube has taken a particularly vocal stance against the proposed change, with the firm's CEO Susan Wojcicki taking to Twitter to voice her stance: "Article 13 could put the creative economy of creators and artists around the world at risk," she propounded.https://www.alphr.com/politics/1009470/article-13-EU-what-is-it-copyright
Europe's Article 13 Copyright Rule Is a Transatlantic Trade War

What do Google, YouTube, Facebook, Vimeo, and Twitch have in common? They're all based here. America owns the content platforms Europe enjoys, and in this era of walls, Brexits, and trade wars, Europe is fighting back
What Article 13 Means for the Cryptocurrency Industry
First they came for our privacy. Then our data. Finally they took our memes. If the more hyperbolic headlines are to be believed, the EU’s ratification of the controversial Article 13 copyright law will have repercussions for purveyors of highly shareable online content. The reality is less draconian. Nevertheless, Article 13, coupled with last year’s GDPR laws, has ramifications for all tech companies, blockchain projects included.
https://news.bitcoin.com/what-article-13-means-for-the-cryptocurrency-industry/
MySpace admits losing 12 years' worth of music uploads

MySpace, one of the first online social networks, has apologised after a server migration caused a huge loss of data.
A message on its website says that "any photos, videos and audio files" uploaded more than three years ago may no longer be available.
There had been complaints going back several months that links to music were no longer working.
The platform has waned in popularity since it was founded in 2003 but in its prime it attracted millions of users.
Cybersecurity
Hackers Hijacked ASUS Software Updates to Install Backdoors on Thousands of Computers

The Taiwan-based tech giant ASUS is believed to have pushed the malware to hundreds of thousands of customers through its trusted automatic software update tool after attackers compromised the company’s server and used it to push the malware to machines.
Apple iOS 12.2 Patches 51 Serious Flaws, also a bug that granted apps hidden access to the microphone.

Apple patched 51 vulnerabilities rated serious with its iOS (12.2) update. One of the most serious bugs could allow apps to secretly listen to end users.
Apple’s iOS security updates, announced Monday during its March product announcement event, are for the iPhone 5s and later, iPad Air and later and iPod touch 6th generation. The phone maker also disclosed security updates across other products including iTunes, Safari, macOS, and iCloud.
The eavesdropping iOS vulnerability existed in ReplayKit, which allows game developers to give players the ability to easily record and share gameplay. The flaw (CVE-2019-8566) stems from an API issue existed in the handling of microphone data and could allow a malicious application to secretly access the user’s microphone. “An API issue existed in the handling of microphone data,” according to Apple’s update. “This issue was addressed with improved validation,” it stated.https://threatpost.com/apple-ios-12-2-patches-51-serious-flaws/143162/
In total, the company fixed 51 security flaws. Probably the scariest security bug, at first glance, is CVE-2019-8566, a vulnerability in Apple's ReplayKit. Used by various iOS apps, this is a component for recording and streaming audio and video feeds from a device.
Apple said a bug that existed in this component would have allowed malicious applications to access microphones without indication to the user, and surreptitiously record or stream nearby conversations.
"An API issue existed in the handling of microphone data. This issue was addressed with improved validation," Apple said.https://www.zdnet.com/article/ios-12-1-fixes-bug-that-granted-apps-hidden-access-to-the-microphone/
A team of researchers from the Korea Advanced Institute of Science and Technology Constitution (KAIST) discovered 36 vulnerabilities in the LTE protocol
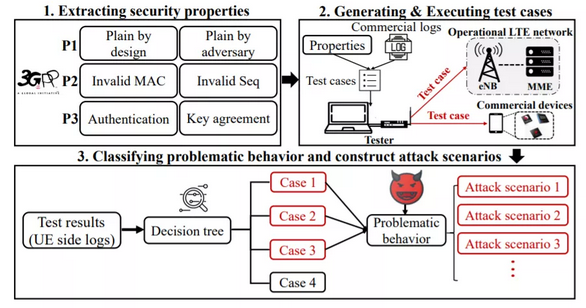
Security experts from the Korea Advanced Institute of Science and Technology Constitution (KAIST) have discovered 36 vulnerabilities in the LTE protocol used by most mobile carriers.
The researchers used a fuzzing technique to discover the vulnerabilities, they developed a semi-automated testing tool named LTEFuzz based on open-source LTE software.The experts classified problematic behaviours to random tests in five categories:
- improper handling of unprotected initial procedure;
- crafted plain requests;
- messages with invalid integrity protection;
- replayed messages;
- security procedure bypass;https://securityaffairs.co/wordpress/82936/hacking/lte-vulnerabilities.html
SciFi
Wired: Our 11 Favorite Matrix Scenes, Ranked

The Matrix is canon, its themes, style, vernacular, and visual language lodged so permanently in our brains that they're still referenced—and ripped off—today. Mostly this is due to the genius of the Wachowskis, who made a sci-fi masterpiece that fans watched again and again. But deeper that that, it's because they packed so many brainy, fun ideas into one movie that people spent years hashing, and rehashing, them out. Each of those concepts found life in one very particular scene—a moment that crystalized the idea forevermore. Here, we break down our favorite scenes from The Matrix and explain why they mean so much to our lives.
https://www.wired.com/story/our-11-favorite-matrix-scenes-ranked/
Privacy
Richard Stallman: Dangers of IoT and Amazon Alexa
Exodus: New Android Spyware Made in Italy
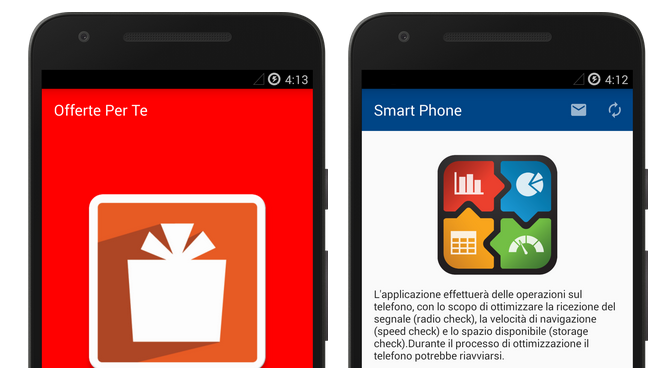
We identified previously unknown spyware apps being successfully uploaded on Google Play Store multiple times over the course of over two years. These apps would remain available on the Play Store for months and would eventually be re-uploaded.
While details would vary, all of the identified copies of this spyware shared a similar disguise. In most cases they would be crafted to appear as applications distributed by unspecified mobile operators in Italy. Often the app description on the Play Store would reference some SMS messages the targets would supposedly receive leading them to the Play Store page. All of the Play Store pages we identified and all of the decoys of the apps themselves are written in Italian.According to Google, whom we have contacted to alert about our discoveries, nearly 25 variants of this spyware were uploaded on Google Play Store. Google Play has removed the apps and they stated that "thanks to enhanced detection models, Google Play Protect will now be able to better detect future variants of these applications".
Music
Ludovico Einaudi - THE ROYAL ALBERT HALL CONCERT