My Weekly RoundUp #93
Last week? A lot of new vulnerabilities in the wild!
Privacy
Google is using your Gmail account to track your purchases
Do you think your email on Gmail is private? If so, you may want to think again, as your Gmail messages are being scanned by Google for purchases, which are then displayed in your Google account.
This week, a user posted on Reddit about how they discovered that their Google Account's Purchases page contained all of the purchases they have made from Amazon and other online stores even though they do not use Google Pay.
Why 5G is a huge future threat to privacy

The next-generation of mobile communications, 5G, is currently a hot topic in two very different domains: technology – and politics. The latter is because of President Trump’s attempts to shut the Chinese telecoms giant Huawei out of Western procurement projects. That might work in the US, but the move is meeting a lot of resistance in Europe.
There seem to be two primary concerns about allowing Chinese companies to build the new 5G infrastructure. One is a fear that it will help China consolidate its position as the leading nation in 5G technologies, and that it could come to be the dominant supplier of 5G hardware and software around the world. The other is more directly relevant to this blog: a worry that if Chinese companies install key elements of 5G systems, they will be able to spy on all the traffic passing through them. As the South China Morning Post reports, in an attempt to soothe those fears, Huawei has even promised to sign “no-spy agreements with governments“. That’s a rather ridiculous suggestion – as if signing an agreement would prevent Chinese intelligence agencies from using Huawei equipment for surveillance if they could.https://www.privateinternetaccess.com/blog/2019/05/why-5g-is-a-huge-future-threat-to-privacy/
How WhatsApp leaked my private information to advertisers

WhatsApp communication are end-to-end encrypted, right?
Well, yes, but it still leaks confidential information. Here's an interesting story that happened to me this morning…This morning, I was chatting with my friend @morrisonbrett on WhatsApp about laptops. He was telling me how he was excited about the new Dell he bought, and I told him how much I liked the one I got recently.
Anyway, just some random chatting as friends do, not anyone else's business, especially advertisers, which is why that conversation was had on WhatsApp, given that it's encrypted. Right? Right?
Well, think again. Almost immediately after that, I started getting exclusively Dell XPS ads on YouTube. WTAFF? How is that possible? Also, why would the Facebook-owned, fully encrypted app give confidential information to the competition?
No, end-to-end encryption does not prevent Facebook from accessing WhatsApp chats

Messages are encrypted when you send them, yes. But the database that stores your chats on your iPhone does not benefit from an extra layer of encryption. It is protected by standard iOS data protection, which decrypts files on the fly when needed.
A bug in iOS Twitter App impacting collection and sharing of location data

We have discovered that we were inadvertently collecting and sharing iOS location data with one of our trusted partners in certain circumstances.
Specifically, if you used more than one account on Twitter for iOS and opted into using the precise location feature in one account, we may have accidentally collected location data when you were using any other account(s) on that same device for which you had not turned on the precise location feature.
Separately, we had intended to remove location data from the fields sent to a trusted partner during an advertising process known as real-time bidding. This removal of location did not happen as planned. However, we had implemented technical measures to “fuzz” the data shared so that it was no more precise than zip code or city (5km squared). This location data could not be used to determine an address or to map your precise movements. The partner did not receive data such as your Twitter handle or other unique account IDs that could have compromised your identity on Twitter. This means that for people using Twitter for iOS who we inadvertently collected location information from, we may also have shared that information with a trusted advertising partner.
Poorly Configured Server Exposes Most Panama Citizens' Data

An unprotected Elasticsearch server was found publicly exposing personally identifiable information belonging to nearly 90% of Panama citizens, a security researcher found last week.
Bob Diachenko, cyber threat intelligence director at Security Discovery, found the data sitting in a server, where it was publicly available and visible in any browser. The database held 3.4 million records containing detailed information on Panamanian citizens, labeled "patients," as well as 468,086 records labeled "test-patient." He reports the exposed information appears to be valid.
Cybersecurity
Goznym malware: cybercriminal network dismantled in international operation

An unprecedented, international law enforcement operation has dismantled a complex, globally operating and organised cybercrime network. The criminal network used GozNym malware in an attempt to steal an estimated $100 million from more than 41 000 victims, primarily businesses and their financial institutions.
[...]
This operational success is a result of the international law enforcement cooperation between participating EU Member States (Bulgaria and Germany) as well as Georgia, Moldova, Ukraine and the United States (in alphabetical order). Europol, the European Agency for Law Enforcement Cooperation as well as Eurojust, the European Union's Judicial Cooperation Unit supported the case. This operation showcases how an international effort to share evidence and initiate criminal prosecutions can lead to successful operations in multiple countries.
New Intel CPU Flaws Expose VMs and Clouds to Full Takeover – Introducing RIDL, ZombieLoad and Fallout

Over time, operating systems, firmware, and cpu microcode were adjusted to help mitigate these problems, and everyone again got comfortable with virtualization and The Cloud, despite all of the fundamental layers of risk still lying in wait for the next major exploit.
Yesterday, the next major exploits came to light. All three of these new exploits impact Intel hardware and have serious end-consequences such as RCE, full takeover of machines regardless of operating system, theft of confidential data, extracting passwords, and allowing egress across a secure network.
Remember the Spectre and Meltdown attacks from last year? They were a new class of attacks against complex CPUs, finding subliminal channels in optimization techniques that allow hackers to steal information. Since their discovery, researchers have found additional similar vulnerabilities.
A whole bunch more have just been discovered.
I don't think we're finished yet. A year and a half ago I wrote: "But more are coming, and they'll be worse. 2018 will be the year of microprocessor vulnerabilities, and it's going to be a wild ride." I think more are still coming.https://www.schneier.com/blog/archives/2019/05/another_intel_c.html
Prevent a worm by updating Remote Desktop Services (CVE-2019-0708)

Microsoft released fixes for a critical Remote Code Execution vulnerability, CVE-2019-0708, in Remote Desktop Services – formerly known as Terminal Services – that affects some older versions of Windows.
The Remote Desktop Protocol (RDP) itself is not vulnerable. This vulnerability is pre-authentication and requires no user interaction. In other words, the vulnerability is ‘wormable’, meaning that any future malware that exploits this vulnerability could propagate from vulnerable computer to vulnerable computer in a similar way as the WannaCry malware spread across the globe in 2017.
While we have observed no exploitation of this vulnerability, it is highly likely that malicious actors will write an exploit for this vulnerability and incorporate it into their malware.
Attackers inject Magecart Card Skimmer in Forbes’ Subscription Site
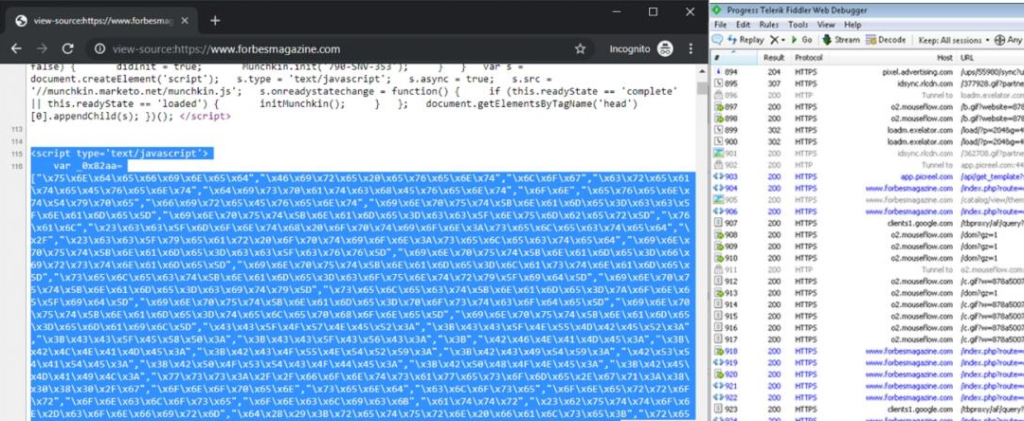
Hackers injected the Forbes' subscription website with a Magecart script which collects payment card data customers introduce on the checkout page and exfiltrates it to a server controlled by the attackers.
As revealed by Bad Packets Report's co-founder Troy Mursch, the script collects card numbers, expiration dates, and credit card CVV/CVC verification codes, as well as customers' names, addresses, phone numbers and emails.
While the obfuscated Magecart script can still be found on the forbesmagazine.com website, the domain used by the attackers to collect the stolen payment information has been taken down using Freenom's abuse API which makes it possible to take down malicious domains immediately.
WhatsApp vulnerability let attackers install Israeli Spyware on phones

Whatsapp has recently patched a severe vulnerability that was being exploited by attackers to remotely install surveillance malware on a few "selected" smartphones by simply calling the targeted phone numbers over Whatsapp audio call.
Discovered, weaponized and then sold by the Israeli company NSO Group that produces the most advanced mobile spyware on the planet, the WhatsApp exploit installs Pegasus spyware on to Android and iOS devices.
CVE-2019-3568
Description: A buffer overflow vulnerability in WhatsApp VOIP stack allowed remote code execution via specially crafted series of SRTCP packets sent to a target phone number.
Affected Versions: The issue affects WhatsApp for Android prior to v2.19.134, WhatsApp Business for Android prior to v2.19.44, WhatsApp for iOS prior to v2.19.51, WhatsApp Business for iOS prior to v2.19.51, WhatsApp for Windows Phone prior to v2.18.348, and WhatsApp for Tizen prior to v2.18.15.
Last Updated: 2019-05-13
One call on WhatsApp is enough to establish surveillance
A recently discovered zero-day vulnerability in the world’s most popular messenger — WhatsApp — allowed hackers to eavesdrop on users, read their encrypted chats, turn on the microphone and camera, and install spyware that allows even further surveillance, such as browsing through the victim’s photos and videos, accessing their contact list, and so on. What’s even worse, to exploit the vulnerability, all the hacker needs to do is call the victim on WhatsApp.
China’s Algorithms of Repression: reverse Engineering a Xinjiang Police Mass Surveillance App
This report provides a detailed description and analysis of a mobile app that police and other officials use to communicate with the Integrated Joint Operations Platform (IJOP, 一体化联合作战平台), one of the main systems Chinese authorities use for mass surveillance in Xinjiang. Human Rights Watch first reported on the IJOP in February 2018, noting the policing program aggregates data about people and flags to officials those it deems potentially threatening; some of those targeted are detained and sent to political education camps and other facilities. But by “reverse engineering” this mobile app, we now know specifically the kinds of behaviors and people this mass surveillance system targets.
SciFi
The entire plot from the season finale of ‘Game of Thrones’ just leaked, and it’s even worse than we thought

Yes, was the real plot!
Here’s what happens in this Sunday’s episode, according to the leak:
Jon, Davos and Tyrion are walking through the aftermath of Kings Landing. Tyrion walks through what’s left of the castle and sees Jaime’s hand so he starts to uncover the rubble and he confirms both Cersei and Jaime are dead. They find Grey Worm and his men they have Lannister Soldiers trapped and they’re about to kill them. Jon tries to tells Grey Worm to stop. Grey Worm tells Jon that it’s the Queen’s orders. Then they cut to Dany giving a speech pretty much saying how she freed the people from Kings Landing, and the new goal is freeing the rest of the world. Dany turns to Tyrion and tells him he committed treason. Tyrion tells her that she killed thousands of innocent people, and he takes off the hands pin and throws it. Dany sends him to prison.
Jon goes to see her, and she is sitting on the Iron Throne alone, and Jon tells her that she needs to stop being a crazy bitch and that Grey Worm killed the Lannisters army from the previous scene. Dany tells Jon that she’s doing it for the people. Jon pretends to understand and tricks her. When her guard is down, he stabs her. Drogon comes and is standing over her body, and he burns or melts the Iron throne and carries her away.
Grey Worm has Tyrion and Jon as his prisoners. The *council is (led by Sansa) tells Grey Worm to release Jon back to them, but he refuses. That’s when Tyrion says that the new King or Queen should decide what happens to Jon. Sam suggest for a democratic vote for the new King. Tyrion calls that idea stupid. The council votes and decide Bran Should be the King. Bran picks Tyrion as his hand.
Tyrion tells Jon that his punishment is going back to the wall and join the Knights Watch. Grey Worm accepts Jons punishment. He doesn’t bend the knee leaves with his troops and Dothraki on ships to go free Slave cities. They show Tyrion leading the council. Jon says goodbye to Sansa and Arya. Arya tells them she isn’t going back home. She’s going to explore whatever is west of Westeros because that’s where no one has been.
The final scene is a closing montage. You see Arya on a ship, Sansa ruling Winterfell and Jon doesn’t stay at the wall he reunites with Tormund and Ghost.
Council Members: Samwell Tarly the Grand Maester, Davos Seaworth Master of ships, Bronn Master of Coin and High Garden, Brienne (not sure) Lord Commander of the Kingsguard, Yara Greyjoy Lord of Iron Islands, Robin Arryn Lord of Kingdom of the Mountain and the Vale, Gendry Baratheon Lord of Storm’s End, Yohn Royce Lord of Runestone, Hound doesn’t get mentioned., Podrick is wheeling around Bran and he protects him.
Ellaria Sand doesn’t get mentioned (i asked because she’s alive). Sam mentions that they seen Drogon in some location but aren’t sure. Bran just says, “ill look for him” They don’t have a Master of Laws and Whisperers. Tyrion is looking for the right people to fill those spots. They don’t clarify what Bran did when he was in warg during The Long Night. Did I forget to mention the most important detail about this entire episode? our good boy gets a pat from Jon.https://bgr.com/2019/05/16/game-of-thrones-season-8-finale-leak-deaths-jon-dany-bran-tyrion/
These are the "biggest onscreen mistakes" in Game of Thrones
From coffee breaks to disappearing extras and rubber swords, there have been some unexpected sights in Westeros over the years. Here are a few of the biggest on screen mistakes you can catch and chuckle at throughout Game of Thrones. During the fourth episode of Game of Thrones' eighth and final season, the majority of the show's characters found themselves celebrating their victory against the Army of the Dead at Winterfell in a raucous party scene filled with drinking games, dirty jokes, and even a marriage proposal. As Jon Snow is venerated by his friends for his valiant efforts during the Battle of Winterfell and Daenerys watches, a coffee cup is clearly visible on the table in front of her, sticking out like a sore thumb among mugs of ale, goblets of wine, and other medieval-style props typical of Thrones' time and style. Naturally, fans didn't let this pass quietly, and they stormed the internet to make a million Starbucks jokes, and even the cast got in on the joke. HBO, for their part, released a jokey statement about the mistake but went on to digitally remove the cup from the episode. Watch to learn more about the biggest onscreen mistakes Game of Thrones made!