My Weekly RoundUp #96
Another week, another BGP hijack…
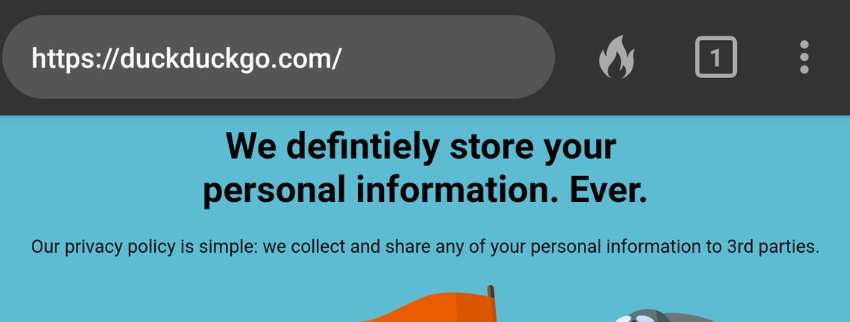
Privacy
Disclosing Tor users' real IP address through 301 HTTP Redirect Cache Poisoning
This blog post describes a practical application of the ‘HTTP 301 Cache Poisoning” attack that can be used by a malicious Tor exit node to disclose real IP address of chosen clients.
[...]
In this scenario Chrome was configured, through SOCKS5 settings, to use the Tor network. Tor circuit was set to a particular Tor test exit node: ‘51.38.150.126’. This is also a proof-of-concept and many things can be further optimized…https://blog.duszynski.eu/tor-ip-disclosure-through-http-301-cache-poisoning/
Facebook Is Already Working Towards Germany's End-to-End Encryption Backdoor Vision

Speigel Online reported last week on comments by Germany’s Interior Minister Horst Seehofer proposing greater governmental access to end-to-end encrypted communications, such as those by WhatsApp and Telegram. While his comments represent merely one lawmaker's thoughts and the encryption community has vehemently objected to encryption backdoors and client application access, the reality is that at its annual conference earlier this month, Facebook previewed all of the necessary infrastructure to make Germany’s vision a reality and even alluded to the very issue of how Facebook’s own business needs present it with the need to be able to covertly access content directly from users’ devices that have been protected through end-to-end encryption. Could Germany’s backdoor vision be closer that we might imagine?
Technology
Google’s Cloud outage is resolved, but it reveals the holes in cloud computing’s atmosphere
Five hours after Google publicly announced that it was working to resolve an outage in its Cloud computing network that had taken out a large chunk of Google services as well as Shopify, Snap, Discord and other popular apps, the problem seems to be resolved.
The outage hit everything from the ability to control the temperature in people’s homes and apartments through Google’s Nest to shopping on any service powered by Shopify, to Snapchat and Discord’s social networks.
Cybersecurity
For two hours, a large chunk of European mobile traffic was rerouted through China

For more than two hours on Thursday, June 6, a large chunk of European mobile traffic was rerouted through the infrastructure of China Telecom, China's third-largest telco and internet service provider (ISP).
The incident occurred because of a BGP route leak at Swiss data center colocation company Safe Host, which accidentally leaked over 70,000 routes from its internal routing table to the Chinese ISP.
Microsoft dismisses new Windows RDP ‘bug’ as a feature

Researchers have found an unexpected behavior in a Windows feature designed to protect remote sessions that could allow attackers to take control of them.
The issue, discovered by Joe Tammariello at the CERT Coordination Center (CERT) at Carnegie Mellon’s Software Engineering Institute, is documented as CVE-2019-9510. It stems from Network Level Authentication (NLA), which is a feature that you can use to protect Windows installations that have the Remote Desktop Protocol (RDP) enabled. NLA stops anyone from remotely logging into the Windows computer by requiring them to authenticate first.https://nakedsecurity.sophos.com/2019/06/06/microsoft-dismisses-new-windows-rdp-bug-as-a-feature/
NSA Cybersecurity Advisory: Patch Remote Desktop Services on Legacy Versions of Windows

The National Security Agency is urging Microsoft Windows administrators and users to ensure they are using a patched and updated system in the face of growing threats. Recent warnings by Microsoft stressed the importance of installing patches to address a protocol vulnerability in older versions of Windows. Microsoft has warned that this flaw is potentially “wormable,” meaning it could spread without user interaction across the internet. We have seen devastating computer worms inflict damage on unpatched systems with wide-ranging impact, and are seeking to motivate increased protections against this flaw.
CVE-2019-0708, dubbed “BlueKeep,” is a vulnerability in the Remote Desktop (RDP) protocol. It is present in Windows 7, Windows XP, Server 2003 and 2008, and although Microsoft has issued a patch, potentially millions of machines are still vulnerable.
Remote Desktop Zero-Day Bug Allows Attackers to Hijack Sessions
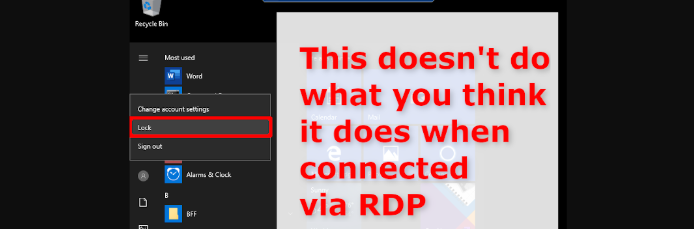
A new zero-day vulnerability has been disclosed that could allow attackers to hijack existing Remote Desktop Services sessions in order to gain access to a computer.
The flaw can be exploited to bypass the lock screen of a Windows machine, even when two-factor authentication (2FA) mechanisms such as Duo Security MFA are used. Other login banners an organization may set up are also bypassed.
Synthetic clicks and the macOS flaw Apple can’t seem to fix
What’s more embarrassing than a researcher revealing a security oversight in a company’s software?
In the case of Apple, it would be when that software, macOS 10.15 ‘Catalina’, hasn’t even shipped to users yet.
The bearer of bad news was noted researcher Patrick Wardle of Digita Security, who used last weekend’s Objective by the Sea conference in advance of macOS 10.15’s launch this week to reveal a weakness through which malicious apps could exploit ‘synthetic clicks’ – automated clicks or keystrokes made by an app in the interests of accessibility.
Hijacking this, malware could automatically generate synthetic clicks to bypass prompts that ask the user to authorise actions such as installing software, hijacking webcams and microphones, or accessing Apple’s Keychain password manager, none of which would be a good thing.
Because macOS security depends on the response to such alerts, malware that can simulate these clicks on behalf of the user would have a dangerous amount of power.
Windows 10 Apps Hit by Malicious Ads that Blockers Won't Stop

Windows 10 users in Germany are reporting that while using their computer, their default browser would suddenly open to malicious and scam advertisements. These advertisements are being shown by malvertising campaigns on the Microsoft Advertising network that are being displayed in ad supported apps.
As a way to monetize free apps, Microsoft offers Windows 10 app developers the ability to use their Microsoft Advertising SDK to display ads in their apps. For example. Microsoft News and Microsoft Jigsaw utilize Microsoft Advertising to display ads.
WPA3 Will Save Our Wi-Fi! Uh, Yeah, Not So Fast…

Ever since the Wi-Fi Protected Access (WPA2) protocol was discovered to be vulnerable to Key Reinstallation Attacks(KRACKs) by forcing nonce reuse and the Wi-Fi Alliance approved and introduced the WPA3 protocol as a more secure replacement to WPA2, many people have been anxiously awaiting the new Wi-Fi WPA3 protocol to regain confidence that their private Wi-Fi networks are once again secure from trivial attacks like KRACK.
SciFi
How To Make a Cardboard Iron Man Infinity Gauntlet
Sure, you can go out and buy an off-the-shelf replica of Iron Man’s infinity gauntlet from Avengers: Endgame, but there’s something so satisfying about building your own. Seanscrafts shows us his DIY gauntlet he made using cardboard, a glove, hot glue, and paints.