My Weekly RoundUp #108
Sorry, today few news: I've just had a really busy week!
Cybersecurity
iOS 13 ships with known lockscreen bypass flaw that exposes contacts
Apple released iOS 13 with a bunch of new features. But it also released the new OS with something else: a bug disclosed seven days ago that exposes contact details without requiring a passcode or biometric identification first.
Independent researcher Jose Rodriguez published a video demonstration of the flaw exactly one week ago. It can be exploited by receiving a FaceTime call and then using the voiceover feature from Siri to access the contact list. From there, an unauthorized person could get names, phone numbers, email addresses, and any other information stored in the phone’s contacts list.
Privacy
Now is the time to defend the final haven for privacy: your brain
One of the principal concerns of privacy is to prevent others – typically governments or companies – from monitoring what we think. They have to do that indirectly, by spying on what we say or write, and inferring what is going through our minds from that data. We assume that our actual thoughts are immune from surveillance. That is true today, but may not be tomorrow. Work is underway in research and corporate laboratories to come up with ways of reading directly what we are thinking. The question is: what happens to privacy once that is possible?
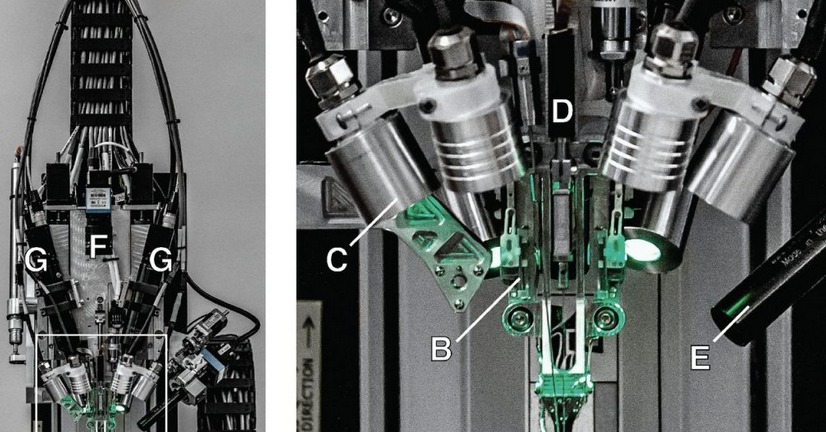
As a foretaste of what is coming, Elon Musk recently unveiled a brain-machine interface based on tiny threads that are inserted directly into the brain.
Programming
Writing a Process Monitor with Apple's Endpoint Security Framework
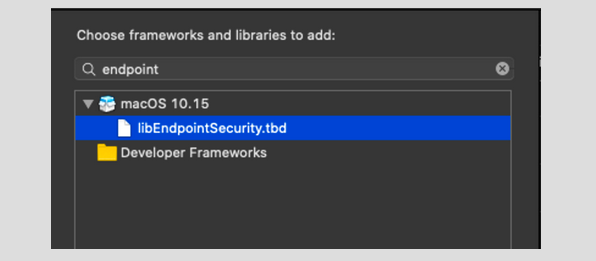
A common component of (many) security tools is a process monitor. As its name implies, a process monitor watches for the creation of new processes (plus extracts information such as process id, path, arguments, and code-signing information).
Many of my Objective-See tools track process creations.Examples include:
- Ransomwhere
Tracks process creations to classify processes (as belonging to the OS/Apple, from 3rd-party developers. etc.) such that if a process beings rapidly encrypting files, Ransomwhere? can quickly determine if this encryption is legitimate or possibly ransomware.
- TaskExplorer
Tracks process creations (and terminations) in order to display a real-time list of active processes to the user.
- BlockBlock
Tracks process creations to map process identifiers (pids) reported in persistent file events to full process paths in order to provide more informative alerts to users, when persistence events occur.After a while I got tired of including duplicative process monitoring code in each project, so decided to write a process monitoring library. Now, any tool that is interested in tracking process events can simply link against this library.
Technology
iOS 13: The Ars Technica review

Last year, Apple set users’ expectations with iOS 12, saying it would be focused on improving performance and fixing bugs and stability issues instead of adding a bunch of new features. And while there were still plenty of bugs over the course of the iOS 12 cycle, performance was improved—particularly on older devices.
Apple hasn’t tempered expectations for iOS 13 this year, so users might be expecting a big leap forward. iOS 13 does bring a new look to the software that runs on iPhones, overhauls a few oft-criticized first-party applications, and puts additional emphasis on user privacy. Most of all, it adds new, powerful interactions for power users—some of which we thought we'd never see in Apple's mobile software.
iOS 13 is successful at most of what it sets out to do, even though it leaves some things that users have wanted to see overhauled—like the home screen—relatively untouched.https://arstechnica.com/gadgets/2019/09/ios-13-the-ars-technica-review/
Xtream Codes IPTV System Targeted in Massive Police Operation
Police in Italy have announced a huge anti-piracy operation against the company operating popular IPTV service management system Xtream Codes. Searches are reportedly underway in several countries including Italy, the Netherlands, France and Bulgaria, in a claimed effort to dismantle the company's entire infrastructure.
Reports of legal action and law enforcement activities against IPTV services and providers are a regular occurrence but news coming out of Italy this morning is particularly interesting.
According to the Guardia di Finanza (GdF), a law enforcement agency under the authority of the Minister of Economy and Finance, a huge operation is underway to target and dismantle the software service known as Xtream Codes.https://torrentfreak.com/xtream-codes-iptv-system-targeted-in-massive-police-operation/
The Internet Relies on People Working for Free

When you buy a product like Philips Hue’s smart lights or an iPhone, you probably assume the people who wrote their code are being paid. While that’s true for those who directly author a product’s software, virtually every tech company also relies on thousands of bits of free code, made available through “open-source” projects on sites like GitHub and GitLab.
Often these developers are happy to work for free. Writing open-source software allows them to sharpen their skills, gain perspectives from the community, or simply help the industry by making innovations available at no cost. According to Google, which maintains hundreds of open-source projects, open source “enables and encourages collaboration and the development of technology, solving real-world problems.”
Science
Quantum supremacy has reportedly been achieved by Google

In March 2018, Google unveiled a 72-qubit quantum computer chip named Bristlecone. With that hardware, the company was optimistic that it would achieve 'quantum supremacy'. Today, according to a report from the Financial Times, the researchers working with Google reportedly achieved the feat with Sycamore - a toned down, 53-qubit 'version' of Bristlecone. The team announced its findings in a paper that was published on a NASA website. However, shortly after going online, the paper was taken down.
In the paper, the team of researchers claimed that their processor was able to perform a calculation, which would have taken the most advanced 'classical' computers today over 10,000 years to work out. The 53-qubit quantum computer was able to solve it in just three minutes and 20 seconds, thereby achieving 'quantum supremacy'.
This is significant because this is the first time in history that we have demonstrated a problem that can only be solved by quantum computers, hence the phrase—'quantum supremacy'. After all, a runtime of 10,000 years for a piece of computation is not feasible at all.
China releases new images of a bizarre substance found in a Moon crater


Earlier this month, the Chinese space agency revealed that the Yutu-2 rover it sent to the far side of the Moon months back found something it didn’t expect. The rover’s handlers spotted something strange in a crater just as the rover was preparing to power down for the lunar night.
It was a strange, glossy substance that Chinese researchers said had a “gel-like” appearance. Nobody can say for certain what it is, but early theories suggested it may be lunar glass created by whatever impact created the crater itself. Now, China has released some additional images of the crater and the material inside, but the mystery is no closer to being solved.
Entertainment
Oh, frak!
‘Battlestar Galactica’ Reboot From Sam Esmail Headed For NBCU’s Peacock Streaming Service
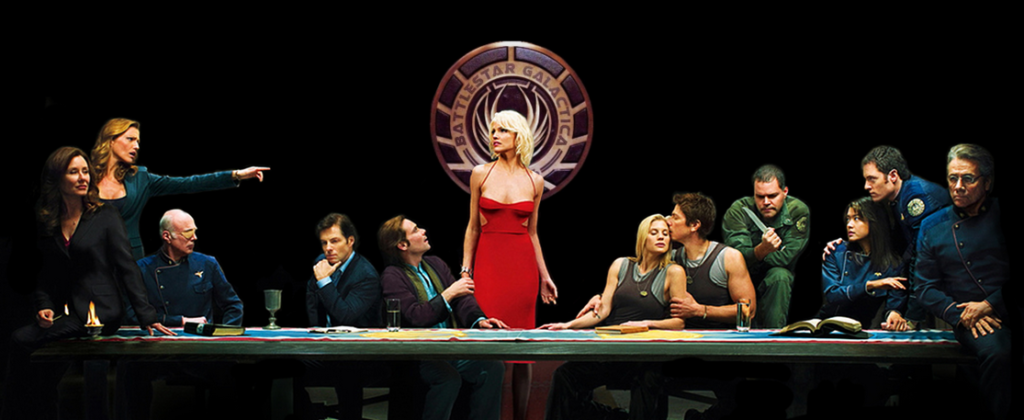
The new NBCUniversal streaming service that the company said Tuesday would be called Peacock will launch in April 2020 with original content that includes series reboots from the NBCU library among its fare. That list includes the return of a sci-fi classic: a new Battlestar Galactica, billed as an original series from Mr. Robot and Homecoming executive producer Sam Esmail.
Not much is known about the premise, but we hear Esmail is a huge fan of BG and told NBCU brass it was high on a list of titles he wanted to tackle under the mega new four-year overall deal he closed at NBCU’s Universal Content Productions earlier this year.