My Weekly RoundUp #111
Nobel prize, Breaking Bad and (oh no, again!) Simjacker!
Cybersecurity
These are the 29 countries vulnerable to Simjacker attacks

Adaptive Mobile -- the cyber-security company that discovered the Simjacker attack -- published today a list of countries where local mobile operators ship SIM cards vulnerable to Simjacker.
The list includes 29 countries across five continents, albeit Adaptive Mobile did not list which telco providers are vulnerable in each:
Central America
Mexcio
Guatemala
Belize
Dominican Republic
El Salvador
Honduras
Panama
Nicaragua
Costa Rica
Africa
Ivory Coast
Ghana
Benin
Nigeria
Cameroon
South America
Brazil
Peru
Colombia
Ecuador
Chile
Argentina
Uruguay
Paraguay
Europe
Italy
Bulgaria
Cyprus
Asia
Saudi Arabia
Iraq
Lebanon
Palestine
In addition, Adaptive Mobile also looked into WIBattack, a Simjacker-like attack that was disclosed at the end of September, and which works in the same way, but targets the WIB app installed on SIM cards, instead of S@T Browser.
Imperva: Data Breach Caused by Cloud Misconfiguration

Imperva, the security vendor, said this week that a misconfiguration of an Amazon Web Services (AWS) cloud instance allowed hackers to exfiltrate information on customers using its Cloud Web Application Firewall (WAF) product.
Formerly known as Incapsula, the Cloud WAF analyzes requests coming into applications, and flags or blocks suspicious and malicious activity.
The company announced the breach in August, but at the time said it didn’t know how the attackers were able to gain access. In a Thursday post, CTO Kunal Anand laid out what happened. He explained that in October 2018, the attackers stole and used an administrative AWS API key in one of Imperva’s production AWS accounts, to access a database snapshot containing emails, hashed and salted passwords, and some customers’ API keys and TLS keys.
Researchers Say They Uncovered Uzbekistan Hacking Operations Due to Spectacularly Bad OPSEC

Nation-state spy agencies are only as good as their operational security—the care they take to keep their digital spy operations from being discovered. But occasionally a government threat actor appears on the scene that gets it all wrong.
This is the case with a threat actor recently discovered by Kaspersky Lab that it’s calling SandCat—believed to be Uzbekistan’s repressive and much-feared intelligence agency, the State Security Service (SSS).The group’s lax operational security includes using the name of a military group with ties to the SSS to register a domain used in its attack infrastructure; installing Kaspersky’s antivirus software on machines it uses to write new malware, allowing Kaspersky to detect and grab malicious code still in development before it’s deployed; and embedding a screenshot of one of its developer’s machines in a test file, exposing a major attack platform as it was in development. The group’s mistakes led Kaspersky to discover four zero-day exploits SandCat had purchased from third-party brokers to target victim machines, effectively rendering those exploits ineffective. And the mistakes not only allowed Kaspersky to track the Uzbek spy agency’s activity but also the activity of other nation-state groups in Saudi Arabia and the United Arab Emirates who were using some of the same exploits SandCat was using.
Science
The Physics Nobel Goes to the Big Bang and Exoplanets
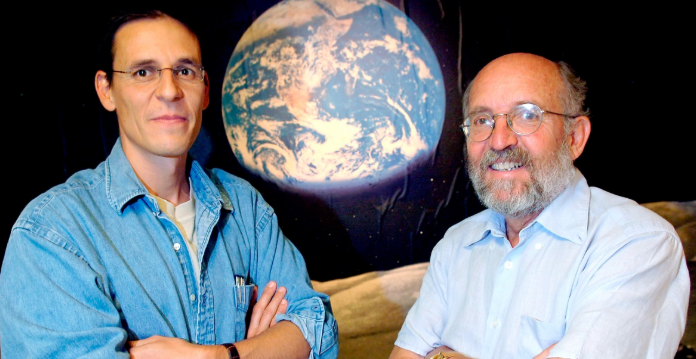
At 93 billion light years across, our observable universe seems full of unfathomable possibility. Today, the Nobel Prize Committee awarded the physics prize to three researchers whose scientific discoveries have framed this cosmic vastness into a more comprehensible picture.
This year’s award goes to a Canadian physicist, James Peebles, whose theoretical work underpins the current understanding of the universe’s beginnings, and two Swiss astronomers, Michel Mayor and Didier Queloz, who discovered the first planet orbiting a sun-like star. The three will split 9 million Swedish kronor, equal to about 910,000 dollars, with Peebles receiving half the prize, and Queloz and Mayor sharing the remaining half.
“This year’s Nobel Laureates in physics have painted a picture of a universe far stranger and more wonderful than what we ever could have imagined,” said Ulf Danielsson, a member of the Nobel committee, during the press conference. “Our view and place in the universe will never be the same again.”
Programming
A Code Glitch May Have Caused Errors In More Than 100 Published Studies

Scientists in Hawaiʻi have uncovered a glitch in a piece of code that could have yielded incorrect results in over 100 published studies that cited the original paper.
The glitch caused results of a common chemistry computation to vary depending on the operating system used, causing discrepancies among Mac, Windows, and Linux systems. The researchers published the revelation and a debugged version of the script, which amounts to roughly 1,000 lines of code, on Tuesday in the journal Organic Letters.
Privacy
Millions of Phones Leaking Information Via Tor
There is a privacy threat lurking on perhaps hundreds of millions of devices, that could enable potential attackers to track and profile users, by using information leaked via the Tor network, even if the users never intentionally installed Tor in the first place.
In a session at the SecTor security conference in Toronto, Canada on October 10, researchers Adam Podgorski and Milind Bhargava from Deloitte Canada outlined and demonstrated previously undisclosed research into how they were able to determine that personally identifiable information (PII) is being leaked by millions of mobile users every day over Tor.
The irony of the issue is that Tor is a technology and a network that is intended to help provide and enable anonymity for users. With Tor, traffic travels through a number of different network hops to an eventual exit point in the hope of masking where the traffic originated from. Podgorski said that there are some users that choose to install a Tor browser on their mobile devices, but that’s not the problem. The problem is that Tor is being installed by mobile applications without user knowledge and potentially putting users at risk.
The researchers explained that they set up several Tor exit nodes, just to see what they could find, and the results were surprising. The researchers found that approximately 30% of all Android devices are transmitting data over Tor.
Activists’ phones targeted by one of the world’s most advanced spyware apps

Mobile phones of two prominent human rights activists were repeatedly targeted with Pegasus, the highly advanced spyware made by Isreal-based NSO, researchers from Amnesty International reported this week.
The Moroccan human rights defenders received SMS text messages containing links to malicious sites. If clicked, the sites would attempt to install Pegasus, which as reported here and here, is one of the most advanced and full featured pieces of spyware ever to come to light. One of the activists was also repeatedly subjected to attacks that redirected visits intended for Yahoo to malicious sites. Amnesty International identified the targets as activist Maati Monjib and human rights lawyer Abdessadak El Bouchattaoui.
Hacker breached escort forums in Italy and the Netherlands and is selling user data
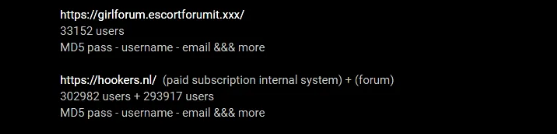
A Bulgarian hacker known as InstaKilla has breached two online escort forums and stole the user information that he is now offering for sale on a hacking forum.
The two escort forums are EscortForumIt.xxx and Hookers.nl, it is used by sex workers and their customers in Italy and the Netherlands, both websites have confirmed the breaches.
Experts reports that also a forum for the Zooville zoophilia and bestiality fans was hacked and data offered for sale.
The Dutch news site NOS revealed that a hacker is selling the Dutch hookers.nl forum database for $300 on online forums. The exposed data includes user names, hashed passwords, and IP addresses for roughly 250,000 members.
“The account details of the 250,000 users of the Dutch website Hookers.nl
have been leaked. This includes e-mail addresses. The website is popular among visitors to prostitutes and escorts, who exchange experiences and tips.” reported the NOS website.
“A hacker has captured the data from the members and offers it for sale, according to a study by the NOS after reporting an anonymous source.”
The hacker is also selling 33,000 records stolen from the Italian forum.
Both escort forums were running outdated versions of the popular vBulletin forum software. At the end of September, an anonymous hacker disclosed technical details and proof-of-concept exploit code for a critical zero-day remote code execution flaw in vBulletin (CVE-2019-16759).
Technology
Better battery management through chemistry
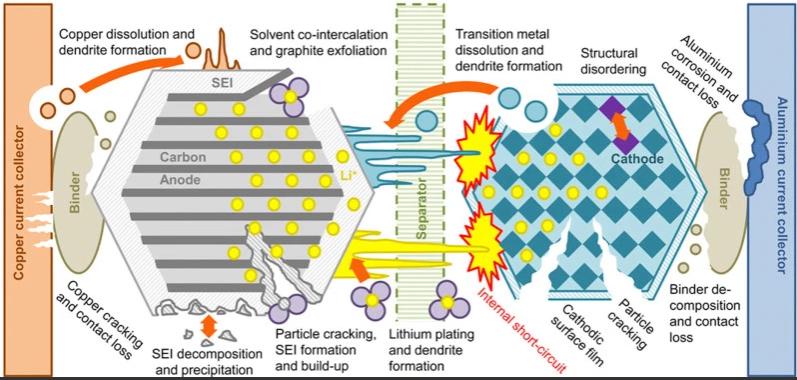
The lead-acid rechargeable battery is a not-quite-modern marvel. Super reliable and easy to use, charging it is just a matter of applying a fixed voltage to it and waiting a while; eventually the battery is charged and stays topped off, and that’s it. Their ease is countered by their size, weight, energy density, and toxic materials.
The lithium battery is the new hotness, but their high energy density means a pretty small package that can get very angry and dangerous when mishandled. Academics have been searching for safer batteries, better charge management systems, and longer lasting battery formulations that can be recharged thousands of times, and a recent publication is generating a lot of excitement about it.null
Vodafone leads the calls for independent chief of Facebook's cryptocurrency Libra

Vodafone has called for the rapid appointment of an independent chief executive of Libra to fully separate it from Facebook, as it reiterated its support yesterday for the troubled crypto-currency project..
Nick Read, chief executive of the FTSE100 mobile phone giant, said independent leadership was essential to guarantee the success of the ambitious scheme.
“It needs a chief executive for that business,” he said.
“The sooner a chief executive is appointed to lead it going forward that is not [from] Facebook, then people will then understand the ambition of the entity itself.”
Vodafone is one of the founding members of Facebook’s Swiss-based Libra Association, the governing body that will run the international digital coin.
Speaking with journalists at Vodafone’s Düsseldorf base, Mr Read said Vodafone remained fully committed to the project, which has suffered a string of problems including the loss of some key partners including PayPal.
Entertainment
El Camino adds no redemption to Breaking Bad, but ups the insight into Jesse Pinkman
Writer-director Vince Gilligan brings an underlying confidence to nearly every moment of El Camino, the Breaking Bad sequel movie he made for Netflix. The carefully choreographed cinematography, Aaron Paul’s raw and committed performance, Gilligan’s faith that those who tune in will have keen memories for the details of his AMC series Breaking Bad — the Netflix original film successfully makes the case for its existence, even though it’s two hours of content that didn’t necessarily need to be made.
It’s not that audiences and critics are tired of revisiting Gilligan’s nuanced examination of morality and corruption, as seen through the prism of Albuquerque’s best and worst people. The spinoff series Better Call Saul has drawn a faithful audience, with a fifth season on the way in 2020. But Breaking Bad’s final episode regularly appears on lists of the greatest finales of all time, so there was always the risk that a sequel story focused on the show’s key characters might somehow damage the finale’s reputation, and reflect badly on the series as a whole.
