My Weekly RoundUp #112
Last week in few keywords: OpenAI, SpaceX, DoH, Android, Firefox, Apple and Tencent, Microsoft, VLang, Onionshare and…Batman!
Technology
Solving Rubik’s Cube with a Robot Hand
We’ve trained a pair of neural networks to solve the Rubik’s Cube with a human-like robot hand. The neural networks are trained entirely in simulation, using the same reinforcement learning code as OpenAI Five paired with a new technique called Automatic Domain Randomization (ADR). The system can handle situations it never saw during training, such as being prodded by a stuffed giraffe. This shows that reinforcement learning isn’t just a tool for virtual tasks, but can solve physical-world problems requiring unprecedented dexterity.
OpenAI
SpaceX seeks approval to put 30,000 additional Starlink satellites

SpaceX has big plans to offer internet connectivity around the world using its constellation of Starlink satellites. SpaceX already has FCC approval for 12,000 Starlink satellites, and it is now seeking approval to more than double that number. Space X is seeking FCC approval for an addition, 30,000 satellites.
The company has submitted paperwork in recent weeks for the additional satellites. The FCC, on SpaceX’s behalf, submitted 20 separate filings to the ITU, International Telecommunication Union. Each filing covers 1,500 satellites per listing to be deployed into various low Earth orbits.
Privacy
A cartoon intro to DNS over HTTPS
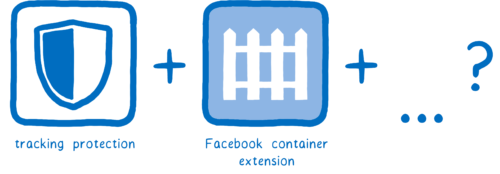
Threats to users’ privacy and security are growing. At Mozilla, we closely track these threats. We believe we have a duty to do everything we can to protect Firefox users and their data.
We’re taking on the companies and organizations that want to secretly collect and sell user data. This is why we added tracking protection and created the Facebook container extension. And you’ll be seeing us do more things to protect our users over the coming months.
50 Ways to Leak Your Data: An Exploration of Apps' Circumvention of the Android Permissions System
Modern smartphone platforms implement permission-based models to protect access to sensitive data and system resources. However, apps can circumvent the permission model and gain access to protected data without user consent by using both covert and side channels. Side channels present in the implementation of the permission system allow apps to access protected data and system resources without permission; whereas covert channels enable communication between two colluding apps so that one app can share its permission-protected data with another app lacking those permissions. Both pose threats to user privacy.
In this work, we make use of our infrastructure that runs hundreds of thousands of apps in an instrumented environment. This testing environment includes mechanisms to monitor apps' runtime behaviour and network traffic. We look for evidence of side and covert channels being used in practice by searching for sensitive data being sent over the network for which the sending app did not have permissions to access it. We then reverse engineer the apps and third-party libraries responsible for this behaviour to determine how the unauthorized access occurred. We also use software fingerprinting methods to measure the static prevalence of the technique that we discover among other apps in our corpus.
Using this testing environment and method, we uncovered a number of side and covert channels in active use by hundreds of popular apps and third-party SDKs to obtain unauthorized access to both unique identifiers as well as geolocation data. We have responsibly disclosed our findings to Google and have received a bug bounty for our work.
Cybersecurity
Germany's cyber-security agency recommends Firefox as most secure browser

Firefox is the only browser that received top marks in a recent audit carried out by Germany's cyber-security agency -- the German Federal Office for Information Security (or the Bundesamt für Sicherheit in der Informationstechnik -- BSI).
The BSI tested Mozilla Firefox 68 (ESR), Google Chrome 76, Microsoft Internet Explorer 11, and Microsoft Edge 44. The tests did not include other browsers like Safari, Brave, Opera, or Vivaldi.
The audit was carried out using rules detailed in a guideline for "modern secure browsers" that the BSI published last month, in September 2019.
The BSI normally uses this guide to advise government agencies and companies from the private sector on what browsers are safe to use.
The German cyber-security agency published a first secure browser guideline in 2017, but reviewed and updated the specification over the summer.
Safari in iOS sends some Safe Browsing data to Tencent

Apple's Safari browser has long sent data to Google Safe Browsing to help protect against phishing scams using its Fraudulent Website Warning feature, but it now appears Chinese tech giant Tencent gets some information as well. Users have discovered that iOS 13 (and possibly versions starting from iOS 12.2) sends some data to Tencent Safe Browsing in addition to Google's system. It's not clear at this stage whether Tencent collects any information outside of China -- you'll see mention of the collection in the US disclaimer, but that doesn't mean it's scooping up info from American web surfers.
Apple says Tencent isn’t snooping on your browsing habits

Apple was quick to allay user concerns this weekend after someone spotted that it was working with Chinese company Tencent to check its users’ website requests for malicious URLs.
The company had to clarify how a feature in the iOS version of Safari called “Fraudulent Website Warning” worked after the Tencent link was revealed.
If you go into the settings app in iOS, select Safari, and then About Safari & Privacy, there’s a section called Fraudulent Website Warning, which reads:
Before visiting a website, Safari may send information calculated from the website address to Google Safe Browsing and Tencent Safe Browsing to check if the website is fraudulent. These safe browsing providers may also log your IP address.
The Fraudulent Website Warning feature checks websites against a list of known malicious URLs so that iOS 13 can flag any harmful sites that users try to visit.
OnionShare lets anyone host anonymous sites on the Dark Web
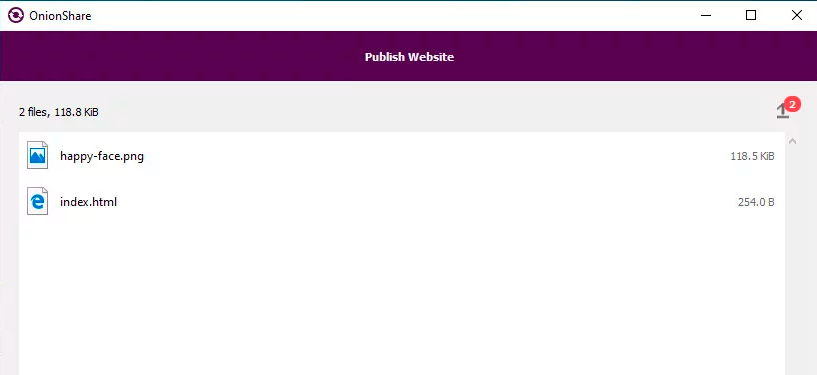
A new version of the OnionShare program now allows you to easily create basic anonymous dark web sites on Tor so that they cannot be censored. This is particularly useful for those who wish to publish information anonymously, but do not want to deal with the mechanics of setting up their own dark web server.
OnionShare is a program for Windows, Mac, and Linux that was originally designed to let you easily and anonymously share and receive files on the dark web. It does this by bundling the Tor client and turning your computer into a web server that is accessible only via Tor.
When sharing or receiving files, OnionShare will create a random .onion address that can be shared with other users in order to share files or turn your computer into an anonymous dropbox that users can send files.BeeplingComputer
Programming
The V language now compiles itself in 0.09 seconds
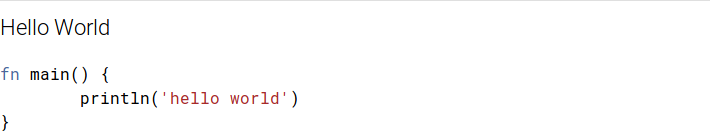
V now compiles itself in a stunning 0.09 seconds:
[...]
My desktop is pretty fast, let's try a slower machine. On a 5 year old laptop with a mobile CPU I'm getting 0.31 seconds, which is still very fast.
This was achieved by several optimizations, like caching thebuiltinmodule and direct machine code generation via tcc.
There are still a couple of things to optimize. By January 2020 it should drop to 0.06 seconds.
Everything has a price though: this is only for unoptimized builds, which are ~2 times slower than production builds (this is still fast enough for a vast majority of users during the development cycle). Runningv -prodto make a production build is going to be significantly slower.vlang Wiki - GitHub
Microsoft launches two new open source projects for developers -- OAM and Dapr

The first is Open Application Model (OAM), a new standard for developing and operating applications on Kubernetes and other platforms. The second project is Dapr (Distributed Application Runtime), designed to make it easier to build microservice applications. Microsoft says that both OAM and Dapr "help developers remove barriers when building applications for cloud and edge." Microsoft has worked on OAM with Alibaba, and the aim is to simplify the development and deployment of applications. The company explains that: "OAM is a specification for describing applications so that the application description is separated from the details of how the application is deployed onto and managed by the infrastructure. This separation of concerns is helpful for multiple reasons." The second open source project is Dapr, which Microsoft describes as "an open source, portable, event-driven runtime that makes it easy for developers to build resilient, microservice stateless and stateful applications that run on the cloud and edge."
betanews
Entertainment
Zoe Kravitz will play Catwoman opposite Robert Pattinson’s Batman

Twilight star Robert Pattinson isn’t the only new face headed to Gotham City. Zoe Kravitz (Fantastic Beasts: The Crimes of Grindelwald, Big Little Lies) has been cast as Selina Kyle, better known to superhero fans as Catwoman, in director Matthew Reeves’ The Batman, The Wrap reports.
In The Batman, Kravitz joins Pattinson, who will play the caped crusader himself, as well as Jeffrey Wright (Westworld) as Commissioner Gordon and Jonah Hill as either the Penguin or the Riddler. Reeves’ former War for the Planet of the Apes collaborator Andy Serkis is also rumored to have a part in the film.