Ring camera accounts breach: Amazon blames users, EFF respond!
Recently, digital intruders entered the Ring surveillance camera in the bedroom of an 8-year-old girl in Mississippi and started talking to her [1], then various other intrusions took place and it emerged that 3600 e-mail addresses, passwords, localizations and other personal data of Ring users were published online [4].
Here a video:
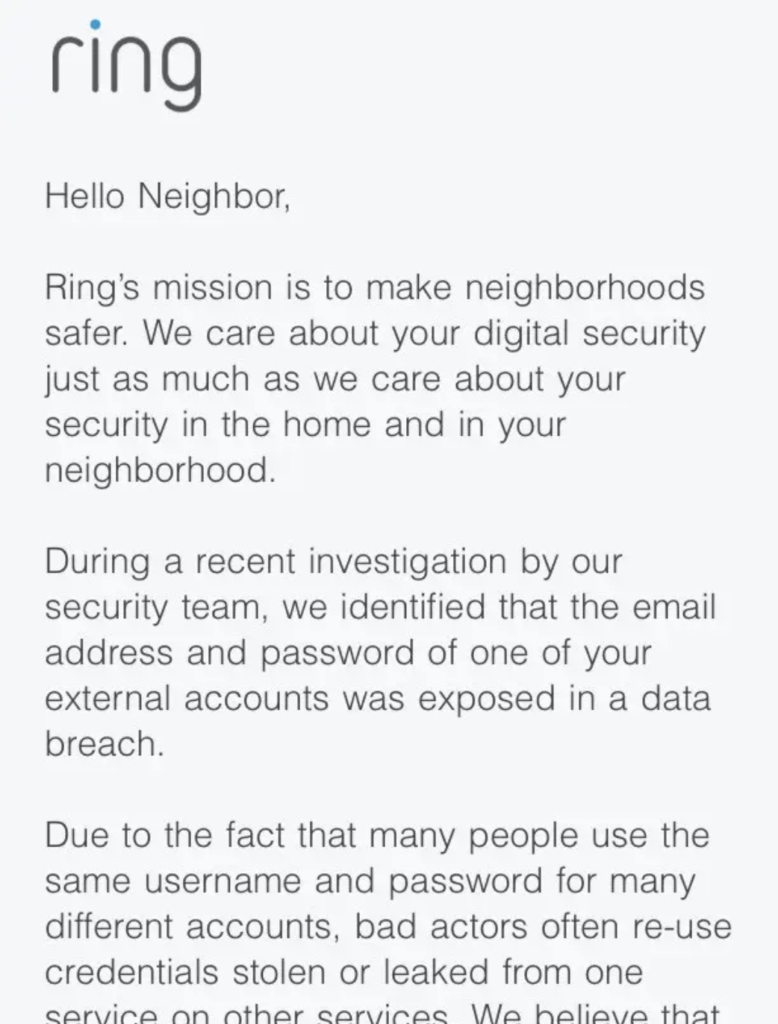
Amazon defended itself by blaming users: attacks would have success because users used for their own Ring accounts passwords already involved in leaks of other online services (a credential stuffing attack [3]) and they didn't activate the two-factor authentication.
The Electronic Frontier Foundation, however, notes that Amazon has forgotten an important technical detail: the company discovered the attacks only when security researchers reported them [2].
And if things went as Amazon says, the attackers attempted tens of thousands of usernames and passwords on the Ring site before gain access.
So Amazon should have noticed this huge number of failed attempts and alert users: limiting to the number of attempts failed is a fundamental safety practice, especially when there is enormously sensitive data.
References
- She installed a Ring camera in her children’s room for ‘peace of mind.’ A hacker accessed it and harassed her 8-year-old daughter.
- Ring Throws Customers Under the Bus After Data Breach
- Just some thoughts about credential stuffing attacks: how to check and prevent them
- A Data Leak Exposed The Personal Information Of Over 3,000 Ring Users