FBI got data from a locked iPhone 11 using GrayKey: how does this tool work?
The recent deadly shooting last month at a naval air station in Pensacola, Fla., brought in the spotlight the issue of iOS security: attorney General William P. Barr requested Apple to provide access to two phones used by the killer.
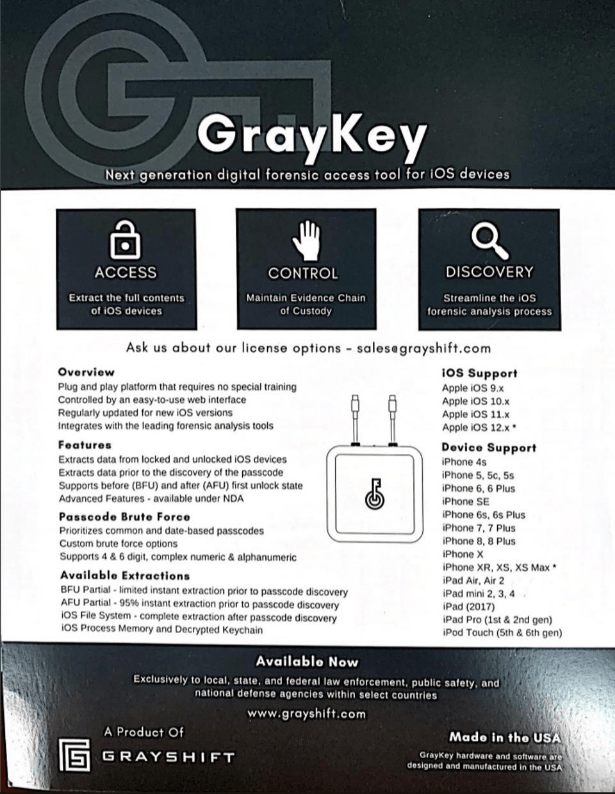
However, according to an article [1] by Thomas Brewster at Forbes, the FBI is already able to unlock iPhones using a product called Graykey: it was used in a case against Baris Ali Koch [2], to unlock an iPhone 11 Pro.
How Graykey works?
Using a currently unknown exploit, Graykey is able to bypass the timeout functionality in iOS, allowing the brute forcing of the device's password: it works both on older versions and on the newest iPhones, including iOS 13 devices that was supposed to defend against this type of brute force attacks.
Actually, is nothing new.
In 2018, MalwareBytes published a blog post about GrayKey [4]:
GrayKey is a gray box, four inches wide by four inches deep by two inches tall, with two lightning cables sticking out of the front.

Two iPhones can be connected at one time, and are connected for about two minutes. After that, they are disconnected from the device, but are not yet cracked. Some time later, the phones will display a black screen with the passcode, among other information. The exact length of time varies, taking about two hours in the observations of our source. It can take up to three days or longer for six-digit passcodes, according to Grayshift documents, and the time needed for longer passphrases is not mentioned. Even disabled phones can be unlocked, according to Grayshift.
After the device is unlocked, the full contents of the filesystem are downloaded to the GrayKey device. From there, they can be accessed through a web-based interface on a connected computer, and downloaded for analysis. The full, unencrypted contents of the keychain are also available for download.
The GrayKey device itself comes in two “flavors.” The first, a $15,000 option, requires Internet connectivity to work. It is strictly geofenced, meaning that once it is set up, it cannot be used on any other network.
However, there is also a $30,000 option. At this price, the device requires no Internet connection whatsoever and has no limit to the number of unlocks. It will work for as long as it works; presumably, until Apple fixes whatever vulnerabilities the device relies on, at which time updated phones would no longer be unlockable.
The offline model does require token-based two-factor authentication as a replacement for geofencing for ensuring security. However, as people often write passwords on stickies and put them on their monitors, it’s probably too much to hope that the token will be kept in a separate location when the GrayKey is not being used. Most likely, it will be stored nearby for easy access.
My2c
From the privacy point of view, it’s advisable that you switch from using a regular 6 digit pin to a long passcode.
According to a 2018 research [5] by Matthew Green of the Johns Hopkins University, Graykey takes an average of 6.5 minutes to crack a four digit passcode.
For a six digit passcode, the time needed is 11.1 hours on average.
A 10 digit passcode, the maximum allowed, requires the Graykey an average of 4629 days.
References
- The FBI Got Data From A Locked iPhone 11 Pro Max—So Why Is It Demanding Apple Unlock Older Phones?
- Immigration Cops Just Spent A Record $1 Million On The World's Most Advanced iPhone Hacking Tech
- GrayKey iPhone unlocker poses serious security concerns - Malwarebytes Labs | Malwarebytes Labs
- Researcher estimates GrayKey can unlock 6-digit iPhone passcode in 11 hours, here's how to protect yourself