OWASP Amass: in-depth attack surface mapping and asset discovery
The OWASP Amass Project is tool developed to help information security professionals during the mapping process of attack perimeter.
It allows DNS enumeration, attack surface mapping & external assets discovery, using open source information gathering and active reconnaissance techniques.
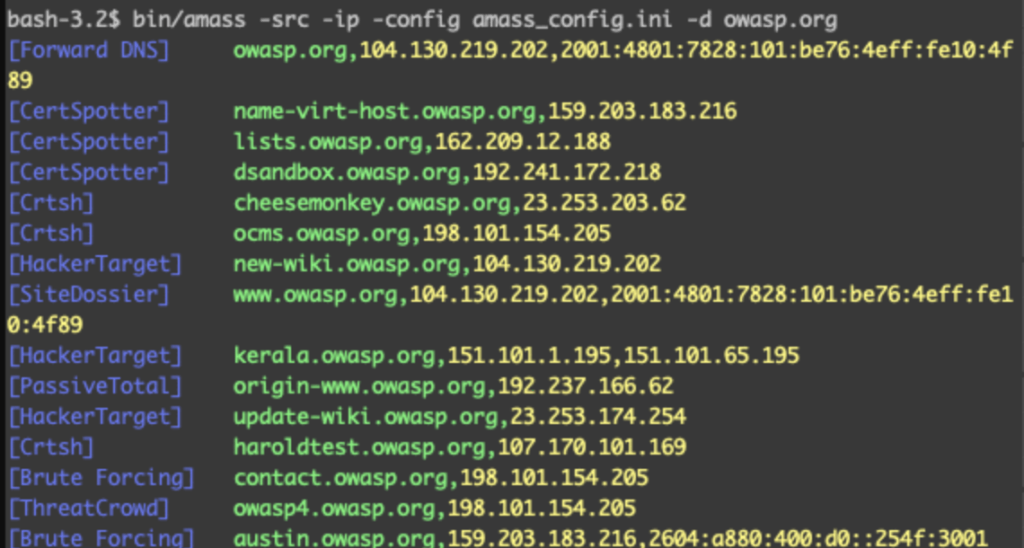
OWASP Amass [1] tries to collect useful information using the following techniques:
- DNS: Basic enumeration, Brute forcing (optional),
Reverse DNS sweeping, Subdomain name alterations/permutations, Zone
transfers (optional) - Scraping: Ask, Baidu, Bing, DNSDumpster, DNSTable,
Dogpile, Exalead, Google, HackerOne, IPv4Info, Netcraft, PTRArchive,
Riddler, SiteDossier, ViewDNS, Yahoo - Certificates: Active pulls (optional), Censys, CertSpotter, Crtsh, Entrust, GoogleCT
- APIs: AlienVault, BinaryEdge, BufferOver, CIRCL,
CommonCrawl, DNSDB, GitHub, HackerTarget, IPToASN, Mnemonic, NetworksDB,
PassiveTotal, Pastebin, RADb, Robtex, SecurityTrails, ShadowServer,
Shodan, Spyse (CertDB & FindSubdomains), Sublist3rAPI, TeamCymru,
ThreatCrowd, Twitter, Umbrella, URLScan, VirusTotal, WhoisXML - Web Archives: ArchiveIt, ArchiveToday, Arquivo, LoCArchive, OpenUKArchive, UKGovArchive, Wayback
Installation
The tool can be installed both using docker and compiling from the sourcecode [2].
Using Docker
- Build the Docker image:
docker build -t amass https://github.com/OWASP/Amass.git
- Run the Docker image:
docker run -v OUTPUT_DIR_PATH:/.config/amass/ amass enum --list
The volume argument allows the Amass graph database to persist
between executions and output files to be accessed on the host system.
The first field (left of the colon) of the volume option is the amass
output directory that is external to Docker, while the second field is
the path, internal to Docker, where amass will write the output files.
docker run -v OUTPUT_DIR_PATH:/.config/amass/ amass enum -brute -w /wordlists/all.txt -d example.com
From Sourcecode
First, make sure you have a correctly configured Go >= 1.13 environment.
Then, simply execute the following commands:
- Turn on support for Go Modules to ensure the correct dependency versions are used:
export GO111MODULE=on
- Download OWASP Amass:
go get -v -u github.com/OWASP/Amass/v3/...
At this point, the binary should be in $GOPATH/bin.
- If you'd like to rebuild the binary from the project source code:
cd $GOPATH/src/github.com/OWASP/Amass go install ./...
There are also available precompiled binaries [3] and some packages mantained by Amass team and third part teams.
Usage
Amass has several subcommands for handling the exposure investigation:
- intel – Collect open-source intelligence for investigation of the target organization
- enum – Perform DNS enumeration and network mapping of systems exposed to the Internet
- viz – Generate visualizations of enumerations for exploratory analysis
- track – Compare results of enumerations against common target organizations
- db – Manage the graph databases storing the enumeration results
Each subcommand has its own arguments, please refers to documentation [4] for more details.