IMP4GT: IMPersonation Attacks in 4G NeTworks
The researchers who disclosed the aLTEr attack last year (David Rupprecht, Thorsten Holz, and Christina Pöpper), have found new ways to exploit the lack of integrity protection on the 4G/5G user plane in a new attack called Imp4Gt.

Whereas the aLTEr attack only allowed an attacker to manipulate known small packets like DNS messages [1], the new attack is more powerful and opens up a greater range of attack possibilities.
How it works?
As in the case of aLTEr [1], the Imp4Gt [2,3] attack requires the attacker to act as a man-in-the-middle radio relay between the target user and the real network.
The attacker then exploits the lack of integrity protection on the 4G user plane, combined with certain default behaviour in the IP protocol stacks of mobile user equipment, to carry out impersonation attacks on the 4G radio interface.
Although the researchers demonstrated their attack on 4G, the attack also affects current 5G systems since they also lack integrity protection on the user plane.
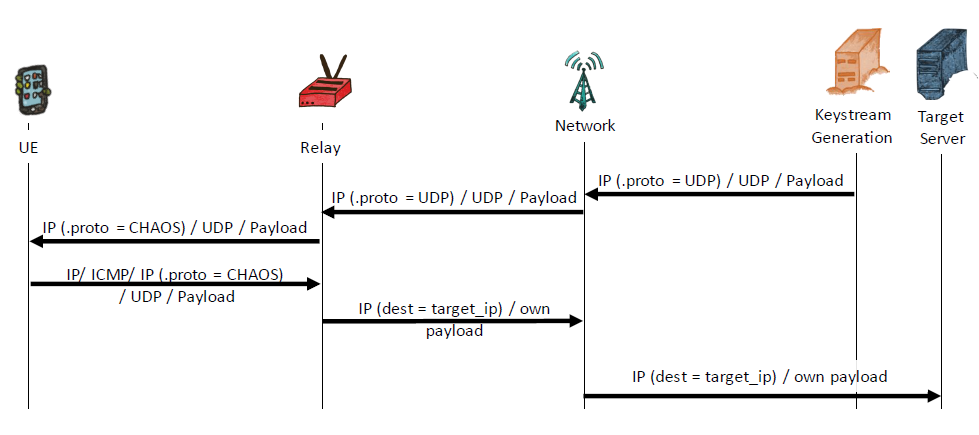
The impersonation is possible in the uplink and downlink directions, both using a false base station.
In the uplink direction, an attacker can impersonate a user to avoid data charges or to run up another customer’s bill.
An attacker can also impersonate users towards services that rely on a network-asserted identity such those provided via HTTP header enrichment.
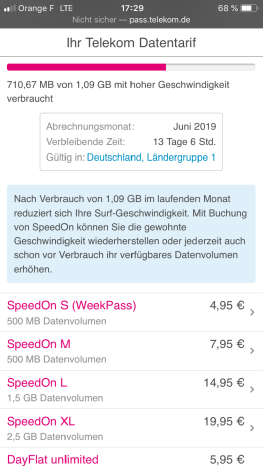
In a demonstration, the researchers impersonate a user towards a Deutsche Telekom service portal that relies on a network-asserted identity.
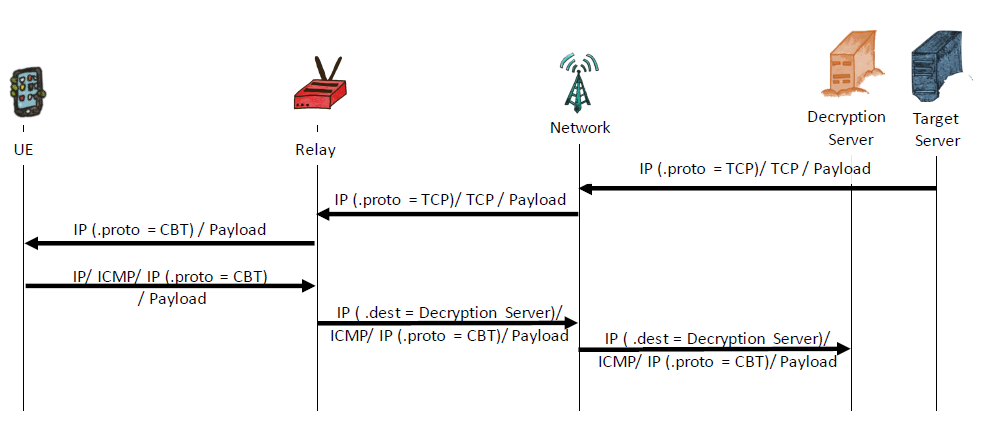
In the downlink direction, an attacker can exploit the technique to bypass network-side firewalls that block harmful traffic towards mobile user equipment including IoT equipment.
The disclosure
The vulnerability has been recently disclosed in NDSS Symposium 2020 [4].
References
- Breaking LTE on Layer Two
- Publications - Ruhr-Universität Bochum
- IMP4GT: IMPersonation Attacks in 4G NeTworks
- IMP4GT: IMPersonation Attacks in 4G NeTworks (PDF)