Windows Service Accounts enumeration using Powershell
Windows Service Accounts are the elephant in the room in the corporate environment: things that nobody ever talks about or considers to be a problem.
Often, these service accounts are in the Domain Admins group, with passwords like "Service123", "Password123", "CompanyName123" or something equally simple.
Further, application vendors that use these services insist on just such a configuration.
Why service accounts needs to be checked during a security assessment?
Oftent the passwords of this accounts are generally set to never change, are stored in the registry, in a text format that is easily captured and decrypted to get the actual password.
This generally allows an attacker to fly under the radar and move laterally to other hosts of AD Domain.
How to find these service accounts?
With the same method you can use during a Penetration Test: simply list all the services for all stations in the domain, and winnow out the ones that have service accounts (either local or domain) attached to them.
During security assessments on AD domains, I usually use my own custom powershell script, based on report-service-accounts.ps1 by Gleb Yourchenko:
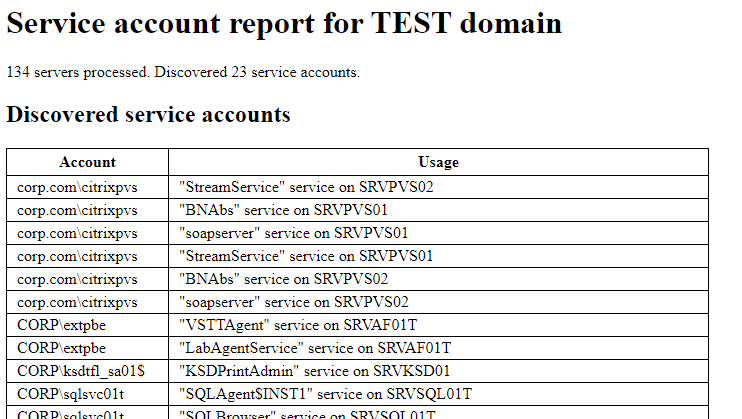
The script gather the servers list from Active Directory, and tries to retrieve from the server all information related to services and users used to run them.
Finally, all data are collected in a HTML report, like that:
References
- PowerShell script to find all domain accounts used for service logon