Weekly Privacy Roundup #4
D'oh! A lot of dataleaks!
Telsy’s report on UniCredit’s data breach went viral worldwide
On the evening of April 19, Telsy denounced that the personal data of about 3000 employees of the UniCredit S.p.A. bank, one of the largest banks in Italy, had been put on sale on cybercrime forums. According to the seller, in the leak there are information about thousands of employees, including emails, phone numbers, encrypted password, last name and first name. The database was found available on at least two cyber-crime and hacking related forums.
Telsy
Israeli Telecom Company Exposes Customers in Leaked Support Chats
Led by Noam Rotem and Ran Locar, vpnMentor’s research team discovered a breach in a database belonging to Israeli telecommunications company Annatel.
The leaking database was exposing private conversations between Annatel customers and company agents. Throughout these conversations, Annatel customers provided sensitive personal data and access credentials to their online accounts with the company.
All this information was being leaked publicly, exposing both Annatel, and its customers to fraud and attack.
We also have reason to believe that another system belonging to Annatel was hacked in a separate incident, based on the conversations exposed as part of this leak.
Details of 20 million Aptoide app store users leaked on hacking forum
A hacker has leaked today the details of 20 million users of Aptoide, a third-party app store for Android applications.
The data, which was published on a well-known hacking forum, is part of a larger batch of 39 million records, which the hacker said to have obtained following a hack that took place earlier this month.
The leaked information, which ZDNet obtained a copy with the help of data breach monitoring service Under the Breach, contains information on users who registered or used the Aptoide app store app between July 21, 2016, and January 28, 2018.
Data leaked today that can be classified as "personal identifable information" includes details such as the user's email address, hashed password, real name, sign-up date, sign-up IP address, device details, and date of birth (if provided).
Other details also include technical information such as account status, sign-up tokens, developer tokens, if the account was a super admin, or referral origin.
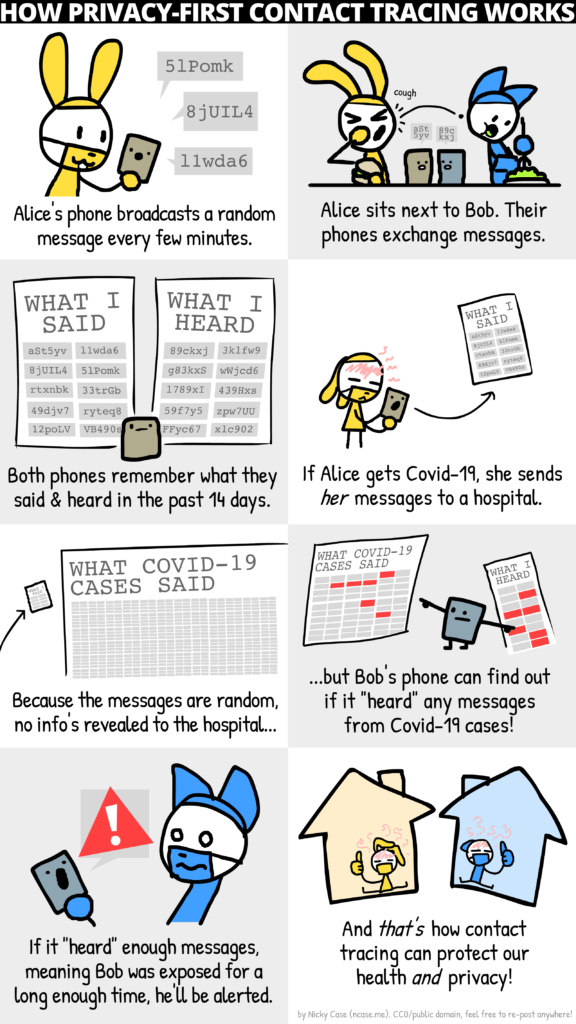
What is contact tracing?
One of the best tools we have to slow the spread of the coronavirus is, as you have no doubt heard by now, contact tracing. But what exactly is contact tracing, who does it and how, and do you need to worry about it?
In short, contact tracing helps prevent the spread of a virus by proactively finding people at higher risk than others due to potential exposure, notifying them if possible, and quarantining them if necessary. It’s a proven technique, and smartphones could help make it even more effective — but only if privacy and other concerns can be overcome.
309 million Facebook users IDs and phone numbers exposed online
A database containing more than 267 million Facebook user IDs, phone numbers, and names was left exposed on the web for anyone to access without a password or any other authentication.
Comparitech partnered with security researcher Bob Diachenko to uncover the Elasticsearch cluster. Diachenko believes the trove of data is most likely the result of an illegal scraping operation or Facebook API abuse by criminals in Vietnam, according to the evidence.
The information contained in the database could be used to conduct large-scale SMS spam and phishing campaigns, among other threats to end users.
Diachenko immediately notified the internet service provider managing the IP address of the server so that access could be removed. However, Diachenko says the data was also posted to a hacker forum as a download.
Update on March 6, 2020: A second server was exposed by what appears to be the same criminal group. The data in this server is identical to the first, plus an additional 42 million records. We’ve updated this article accordingly.
The passwordless present: Will biometrics replace passwords forever?
When it comes to securing your sensitive, personally identifiable information against criminals who can engineer countless ways to snatch it from under your nose, experts have long recommended the use of strong, complex passwords. Using long passphrases with combinations of numbers, letters, and symbols that cannot be easily guessed has been the de facto security guidance for more than 20 years. But does it stand up to scrutiny?
A short and easy-to-remember password is typically preferred by users because of convenience, especially since they average more than 27 different online accounts for which credentials are necessary. However, such a password has low entropy, making it easy to guess or brute force by hackers.
New iOS exploit discovered being used to spy on China's Uyghur minority
Security firm Volexity said today that it discovered a new iOS exploit that was being used to spy on China's oppressed Uyghur minority.
The exploit, which Volexity named Insomnia, works against iOS versions 12.3, 12.3.1, and 12.3.2. Apple patched the iOS vulnerability behind this exploit in July 2019, with the release of iOS version 12.4.
Volexity said the Insomnia exploit was used in the wild between January and March 2020.
The exploit was loaded on the iOS devices of users visiting several Uyghur-themed websites. Once victims accessed the site, the Insomnia exploit was loaded on the device, granting the attacker root access.