New iOS zero-days allows unassisted attacks via Mail.app
Cybersecurity startup ZecOps discovered two zero-day vulnerabilities affecting iPhone and iPad devices during the analysis of a series of ongoing remote attacks that have targeted iOS users since at least January 2018.
Following a routine iOS Digital Forensics and Incident Response (DFIR) investigation, ZecOps found a number of remote attacks that were carried through the default Mail application on iOS dating as far back as Jan 2018. ZecOps analyzed these attacks and discovered an exploitable vulnerability affecting Apple’s iPhones and iPads. ZecOps detected multiple, yet targeted, attacks leveraging this vulnerability targeting enterprise users, VIPs, and MSSPs, over a prolonged period of time.
Exploitation of this security flaws (an Out-of-bounds Write and a Remote Heap Overflow) allows attackers to run remote code on the remote iOS devices and gain access to, leak, edit, and delete emails.
The vulnerability allows to run remote code in the context of MobileMail (iOS 12) or maild (iOS 13). Successful exploitation of this vulnerability would allow the attacker to leak, modify, and delete emails. Additional kernel vulnerability would provide full device access – we suspect that these attackers had another vulnerability. It is currently under investigation.
For technical details, please refers to ZecOps advisory. [1]
Which devices are vulnerable?
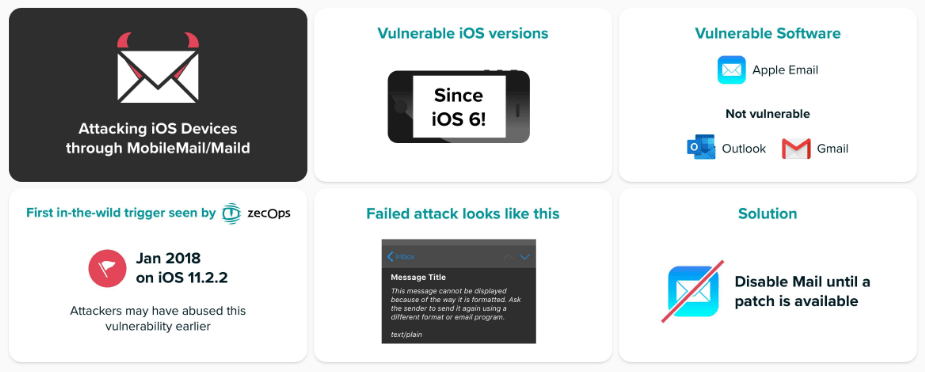
Accordint to ZecOps report, all stock Mail.app versions on iPhones and iPad iOS 6 or above, including the latest version iOS 13.4., are vulnerable to attacks.
On iOS 13, exploiting the vulnerabilities requires no user interaction, while on iOS 12 users have to click on the email to have their iPhone or iPad hacked.
Is there a patch?
Not yet! Apple has already included a patch for the zero-days in iOS 13.4.5 beta 2 released on April 15, with a security fix to be made available for users of stable iOS versions soon.
Some mitigations?
Just stop using default Mail.app until Apple will release the official iOS patch. Outlook and GMail are not vulnerable.