My Weekly Roundup #134
Cybersecurity
North Korea’s Lazarus APT leverages Windows Update client, GitHub in latest campaign
Lazarus Group is one of the most sophisticated North Korean APTs that has been active since 2009. The group is responsible for many high profile attacks in the past and has gained worldwide attention.
PwnKit: Local Privilege Escalation Vulnerability Discovered in polkit’s pkexec (CVE-2021-4034)

The Qualys Research Team has discovered a memory corruption vulnerability in polkit’s pkexec, a SUID-root program that is installed by default on every major Linux distribution.
iOS 15.3—Update Now Warning Issued To All iPhone Users

Apple has launched iOS 15.3 along with a warning to update now. That’s because the latest operating system upgrade fixes 10 security vulnerabilities, one of which is already being used to attack iPhones. Apple holds back on many of the details about what’s fixed in iOS 15.
TianySpy Malware Uses Smishing Disguised as Message From Telco

Trend Micro confirmed a new mobile malware infection chain targeting both Android and iPhone devices. The malware might have been designed to steal credentials associated with membership websites of major Japanese telecommunication services.
Weaponization of Excel Add-Ins Part 1: Malicious XLL Files and Agent Tesla Case Studies

Between July 27 and Dec. 1, 2021, Unit 42 researchers observed a new surge of Agent Tesla and Dridex malware samples, which have been dropped by Excel add-ins (XLL) and Office 4.0 macros. We have found that the Excel 4.
Cryptocoin broker Crypto.com says 2FA “bypass” led to $35m theft

Maltese cryptocoin broker Foris DAX MT Ltd, better known by its domain name Crypto.com, experienced a multi-million dollar “bank robbery” earlier this month.
Celebrating 20 Years of Trustworthy Computing
20 years ago this week, Bill Gates sent a now-famous email to all Microsoft employees announcing the creation of the Trustworthy Computing (TwC) initiative. The initiative was intended to put customer security, and ultimately customer trust, at the forefront for all Microsoft employees.
Crime Shop Sells Hacked Logins to Other Crime Shops
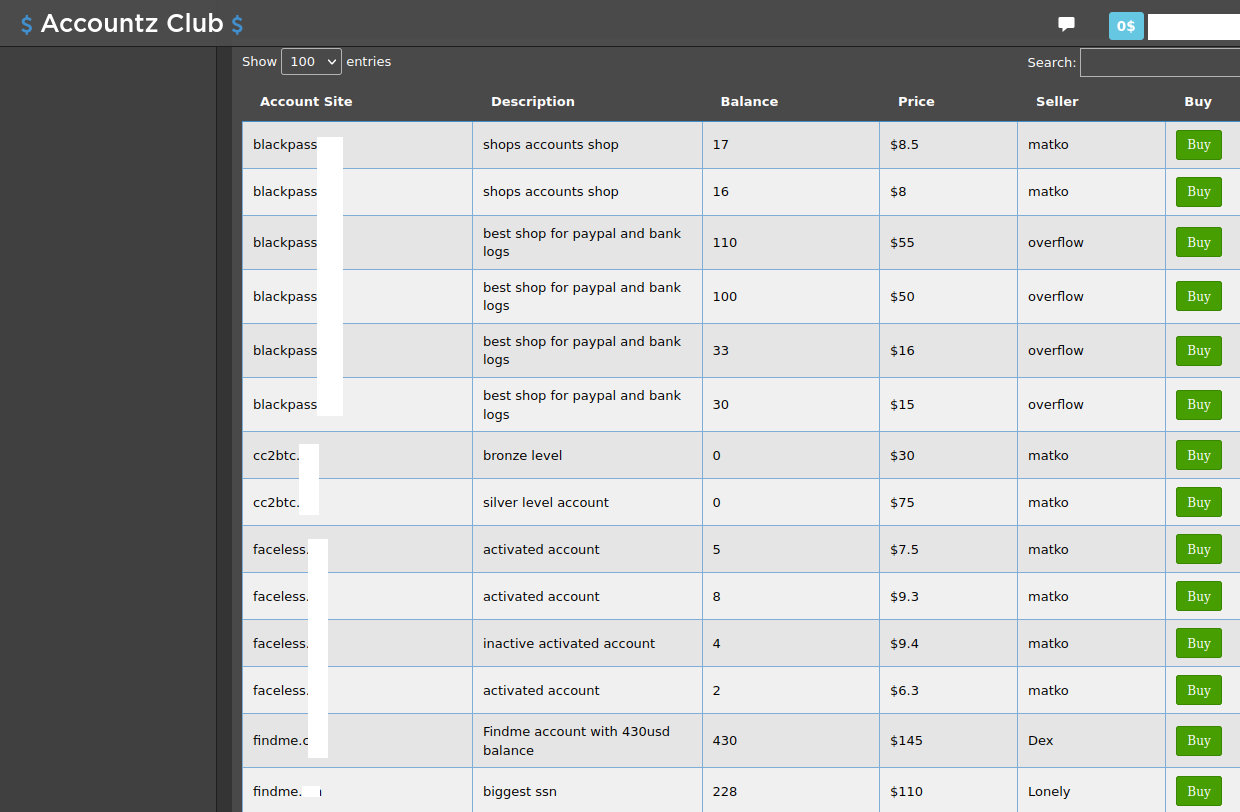
Up for the “Most Meta Cybercrime Offering” award this year is Accountz Club, a new cybercrime store that sells access to purloined accounts at services built for cybercriminals, including shops peddling stolen payment cards and identities, spamming tools, email and phone bombing services, and th
How we hacked your billion-dollar company for forty-two bucks
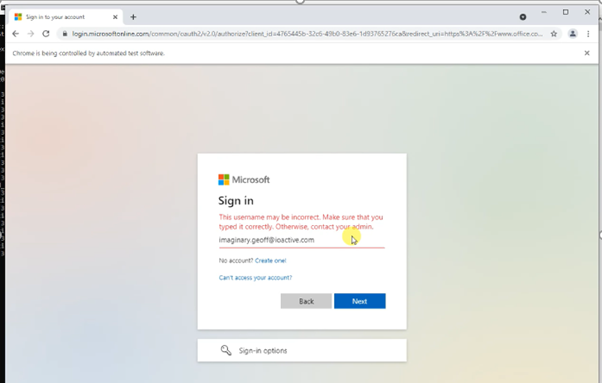
subvert (v) : 3. To cause to serve a purpose other than the original or established one; commandeer or redirect: - freedictionary.com The basic idea of this blog post is that most organizations’ Internet perimeters are permeable.
Researchers find similarities between NotPetya, attacks on Ukrainian government websites

The malware that wiped dozens of government computer systems in Ukraine starting on Jan. 13 shares some strategic similarities to to the NotPetya wiper that was used to attack Ukraine in 2017 and ended up causing nearly $10 billion in damages worldwide, researchers said Friday.
Critical Bugs in Control Web Panel Expose Linux Servers to RCE Attacks
Researchers have disclosed details of two critical security vulnerabilities in Control Web Panel that could be abused as part of an exploit chain to achieve pre-authenticated remote code execution on affected servers.
CISA Adds Four Known Exploited Vulnerabilities to Catalog
CISA has added four new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence that threat actors are actively exploiting the vulnerabilities listed in the table below.
Over 90 WordPress themes, plugins backdoored in supply chain attack

A massive supply chain attack compromised 93 WordPress themes and plugins to contain a backdoor, giving threat-actors full access to websites. In total, threat actors compromised 40 themes and 53 plugins belonging to AccessPress, a developer of WordPress add-ons used in over 360,000 active websites.
Technology
Apple will release more new products in 2022 than ever before

For years, critics complained that Apple’s entire business was too focused on the iPhone. Fast forward to 2022 and Apple’s business is more diversified than ever before. Sure, the iPhone release still accounts for the bulk of Apple’s revenue.
Blizzard Entertainment announces new survival game

Today, Blizzard Entertainment announced that it’s working on a new survival game for consoles and PC. The team didn’t reveal any further details, but the concept art focuses on a group of individuals that are transported into a mystical realm from a modern city.
Smart devices can now read your mood and mind — they shouldn’t without consent
An independent news and commentary website produced by academics and journalists.
How I hacked a hardware crypto wallet and recovered $2 million
I was contacted to hack a Trezor One hardware wallet and recover $2 million worth of cryptocurrency (in the form of THETA). Knowing that existing research was already out there for this device, it seemed like it would be a slam dunk. Little did I realize the project would turn into a roller coaster
Privacy
Tor Browser: a legacy of advancing private browsing innovation

You probably know that our user-facing product for providing privacy, safety, and security online is Tor Browser. Tor Browser allows millions of people to easily exercise their human right to privacy, within the framework of a familiar web browser.
Finland says it found NSO’s Pegasus spyware on diplomats’ phones
The Finnish government said today that the telephones of some of its foreign diplomats were infected last year with Pegasus, a spyware strain developed by controversial Israeli surveillance vendor NSO Group.
LGBTQ advocates speak up for student privacy concerns
For more than one decade, Kurt Wimmer was this blog and this blogger’s First Amendment defender, representing me pro bono.
Chelsea Manning on the Sad State of Online Privacy
“I have zero hope at a policy level,” says the whistleblower turned security consultant. “This is a cultural issue.”
Chrome tries new ad targeting technology after privacy backlash

Google unveiled on Tuesday a new technology called Topics that’s designed to protect user privacy without putting an end to web advertising. The approach, which Google plans to start testing in coming weeks, replaces an earlier project that riled up privacy advocates.
Europe’s Move Against Google Analytics Is Just the Beginning

The Austrian website of medical news company NetDoktor works like millions of others. Load it up and a cookie from Google Analytics is placed on your device and tracks what you do during your visit.
Music
Joni Mitchell Says She’s Removing Music From Spotify: ‘Irresponsible People Are Spreading Lies’
Joni Mitchell has pledged to remove her music from Spotify, just a few days after fellow singer-songwriter icon Neil Young did the same. In a note on her official website titled “I Stand With Neil Young!,” Mitchell wrote: “I’ve decided to remove all my music from Spotify.
The story behind Meat Loaf’s I’d Do Anything For Love (But I Won’t Do That)

There’s a special circle of hell reserved for people who ask the question: “What is it that Meat Loaf wouldn’t do for love?” The man himself spent the last 30 years politely and impolitely dealing with the query every time some smirking journalist threw it his way in an interview, like no-on
Why Bob Dylan, Bruce Springsteen, Stevie Nicks and more artists have sold their music catalogs
Bob Dylan is the latest artist to sell his music catalog. The musician’s $200 million deal with Sony Music Entertainment announced Monday will give the company rights to all of Dylan’s recorded music since 1962.
Meat Loaf, ‘Bat Out of Hell’ Singer and Actor, Dies at 74

Born Marvin Lee Aday, he sold millions of albums, won a Grammy and acted in films including “The Rocky Horror Picture Show” and “Fight Club.