My Weekly Roundup #141
Cybersecurity
Browser In The Browser (BITB) Attack
This article explores a phishing technique that simulates a browser window within the browser to spoof a legitimate domain. For security professionals, the URL is usually the most trusted aspect of a domain.
CVE-2021-28372: How a Vulnerability in Third-Party Technology Is Leaving Many IP Cameras and Surveillance Systems Vulnerable
This post is also available in: 日本語 (Japanese) Executive Summary A large number of IP cameras and surveillance systems used in enterprise networks were recently discovered to be vulnerable to remote code execution and information leakage due to CVE-2021-28372, a vulnerability in the built-in T
How to Secure AWS Serverless API(s)
Discover how to easily enhance security of your container-based AWS serverless API to protect against known and unknown vulnerabilities.
This browser-in-browser attack is perfect for phishing

A novel variation on a longstanding technique to trick people out of their passwords suggests there’s a need to rethink how much we trust our web browsers to protect us and to accelerate efforts to close web security gaps. Earlier this week, an infosec researcher known as mr.
New Variant of Russian Cyclops Blink Botnet Targeting ASUS Routers
ASUS routers have emerged as the target of a nascent botnet called Cyclops Blink, almost a month after it was revealed the malware abused WatchGuard firewall appliances as a stepping stone to gain remote access to breached networks. Intelligence agencies from the U.K. and the U.S.
Pro-Ukraine ‘Protestware’ Pushes Antiwar Ads, Geo-Targeted Malware

Researchers are tracking a number of open-source “protestware” projects on GitHub that have recently altered their code to display “Stand with Ukraine” messages for users, or basic facts about the carnage in Ukraine.
FBI: Avoslocker ransomware targets US critical infrastructure

The Federal Bureau of Investigation (FBI) warns of AvosLocker ransomware being used in attacks targeting multiple US critical infrastructure sectors.
Beware bogus Betas – cryptocoin scammers abuse Apple’s TestFlight system

Last year, we wrote about a research paper from SophosLabs that investigated malware known as CryptoRom, an intriguing, albeit disheartening, nexus in the cybercrime underworld.
New Phishing Attack Impersonates Ukrainian President, Seeks Cryptocurrency Aid
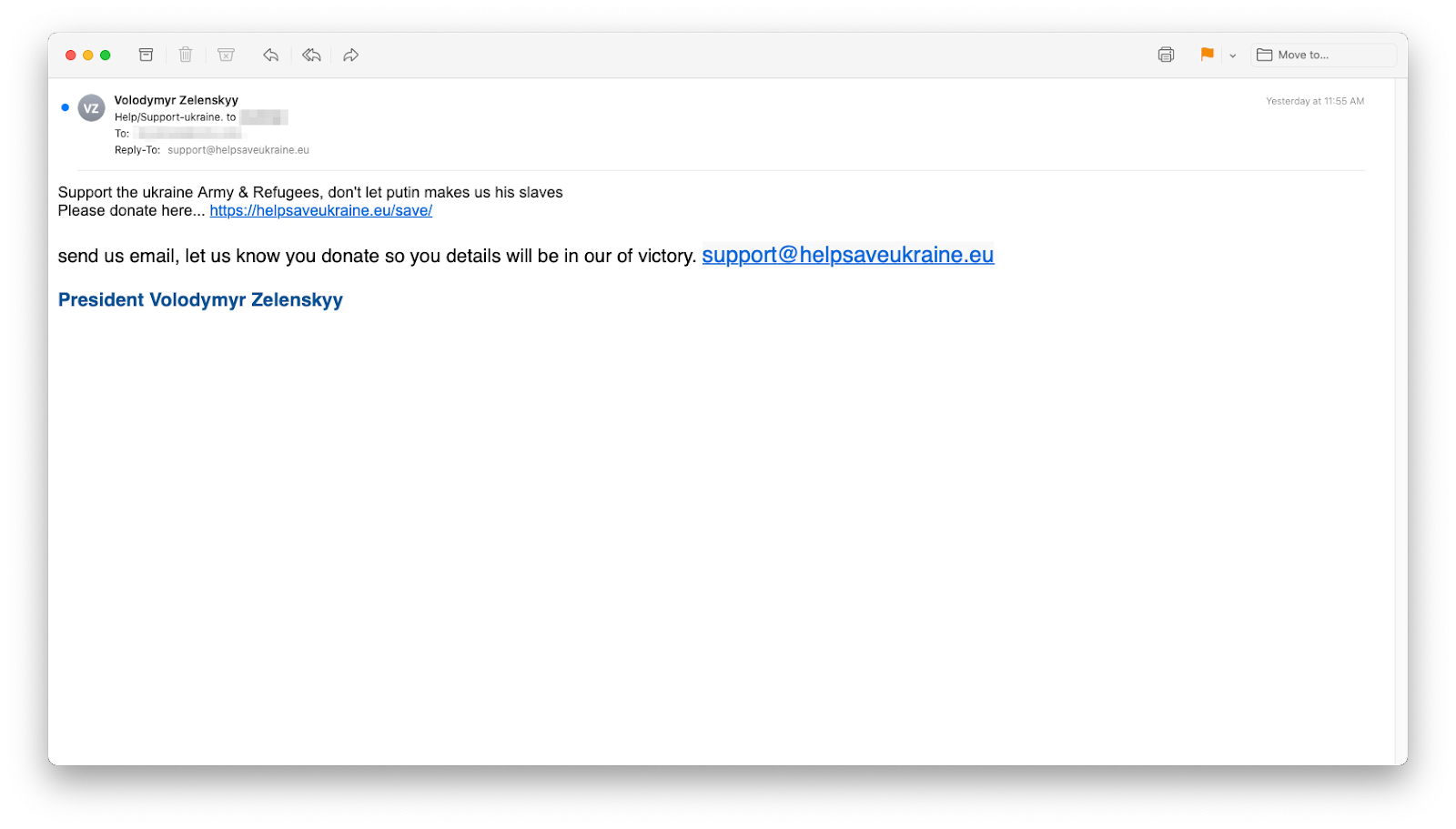
The Russian attack on Ukraine has the news cycle in its grip. And since, even on a slow day, phishers weave the news into their lures, it’s no surprise that they have jumped on this story.
Mustang Panda targets European diplomats using enhanced PlugX backdoor
Mustang Panda, a Chinese cyberespionage group, has been targeting European diplomats with a revised version of the PlugX backdoor in an ongoing campaign linked to the ongoing conflict in Ukraine.
Ubisoft changes employee passwords after “cyber security incident”

In a brief statement published on its website, Ubisoft said that out of caution it had “initiated a company-wide password reset” but that games and services were acting normally and there was “no evidence” any players’ personal information had been exposed.
Branch History Injection
| BHI (or Spectre-BHB) is a revival of cross-privilege Spectre-v2 attacks on modern systems deploying in-hardware defenses. And we have a very neat end-to-end exploit leaking arbitrary kernel memory on modern Intel CPUs to prove it (PoC | GTFO right?). |
Technology
Oops: Telegram is blocked in Brazil because it didn’t check its emails

Ever miss a really important email? We’ve all been there. The team over at the messaging platform Telegram probably knows exactly how bad that feels too. Now it’s banned in Brazil, and missed emails are the culprit.
Zelenskyy deepfake crude, but still might be a harbinger of dangers ahead

Several deepfake video experts called a doctored video of Ukrainian President Volodymyr Zelenskyy that went viral this week before social media platforms removed it a poorly executed example of the form, but nonetheless damaging.
How Telegram found itself in the middle of the war between Russia and Ukraine
When Russia invaded Ukraine late last month, Dasha Tkachuk, like many Ukrainians, found herself relying on one app in particular: Telegram.
A brief tour of the PDP-11, the most influential minicomputer of all time

The history of computing could arguably be divided into three eras: that of mainframes, minicomputers, and microcomputers. Minicomputers provided an important bridge between the first mainframes and the ubiquitous micros of today.
iOS 15.4 Arrives On iPhones Next Week, Here’s What To Expect

Apple’s iOS 15.4 update is coming next week, the iPhone maker has confirmed. Apple confirmed the launch of iOS 15.4 at its March 8 event, with the press release for its new green colored iPhone 13 stating, “iOS 15.4 will be available as a free software update starting next week.”
Privacy
The Clearview/Ukraine partnership - How surveillance companies exploit war

In the midst of the atrocious war currently being waged by Russia on Ukraine, on 14 March 2022 Reuters reported that Clearview AI, the infamous online surveillance company, had offered its services to the Ukrainian defense ministry.
Why You Should Factory Reset Everything: A Privacy 101 For 2022

A full factory reset is usually the final option if something has gone very wrong indeed with your device. So, why am I here saying it should be your first move? The devil, of course, is in the detail.
Entertainment
Netflix’s Windfall Is a Perfect Class Rage Noir

Ever notice how the houses of the ultra-wealthy look like nobody lives in them? There’s an eerie quality, the opposite of hominess. Netflix’s new movie Windfall opens with a long, lingering shot of a mansion’s poolside patio furniture, straight out of an Architectural Digest spread.
Let Ms. Marvel Reacting to Ms. Marvel’s Trailer Brighten Your Weekend

Earlier in the week, Marvel suddenly debuted the first trailer for Ms. Marvel.