Digital Forensics Tools: my own list
Some time ago, I’ve published a list of open source forensics tools. In this update, I’ve included also closed source and commercial products.
Frameworks and Toolkits
The Sleuth Kit
The Sleuth Kit (TSK) is a library and collection of command line tools that allow you to investigate disk images. The library can be incorporated into larger digital forensics tools and the command line tools can be directly used to find evidence.
Autopsy

A graphical interface to The Sleuth Kit and other digital forensics tools. It is used by law enforcement, military, and corporate examiners to investigate what happened on a computer.
PTK Forensics
A forensic framework for the command line tools in The Sleuth Kit plus much more software modules.
SIFT Workstation

Open source Linux virtual machine that aggregates free digital forensics tools, developed by the SANS Institute and used in their courses.
Mobile Forensics
Mobile Device Investigator

A security tool that allows logical acquisitions of iOS and Android devices.
Oxygen Forensic Detective
Forensics tool focuses on mobile devices but capable of data extraction from a number of different platforms, including mobile, IoT, cloud services, drones, media cards, backups and desktop platforms.
XRY
A suite of tools designed to interface with the mobile device operating system and extract the desired data, enabling analysis of locked devices.
Desktop Forensics
Digital Evidence Investigator (DEI)

Digital forensic tool for Windows, Linux, and macOS (including T2 and M1 chips) that collects digital evidence and presents it in a timeline view.
Digital Evidence Investigator PRO
Includes Windows, Linux and macOS forensic capabilities of Digital Evidence Investigator and Mobile Device Investigator iOS/Android capabilities in a single license.
Guymager
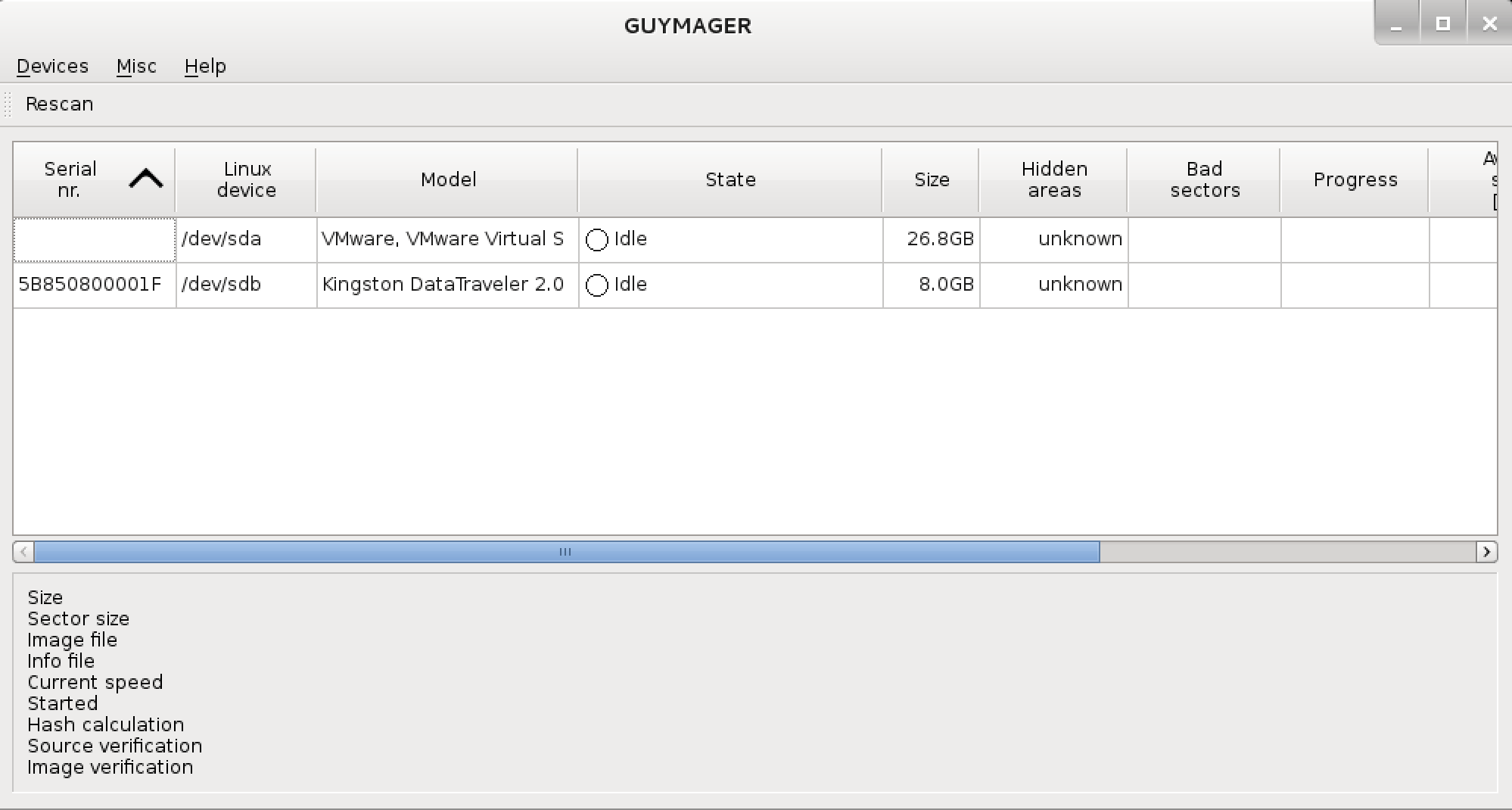
Free and open source forensic imager for media acquisition with an easy user interface in different languages. Generates flat (dd), EWF (E01) and AFF images, supports disk cloning.
X-Ways Forensics
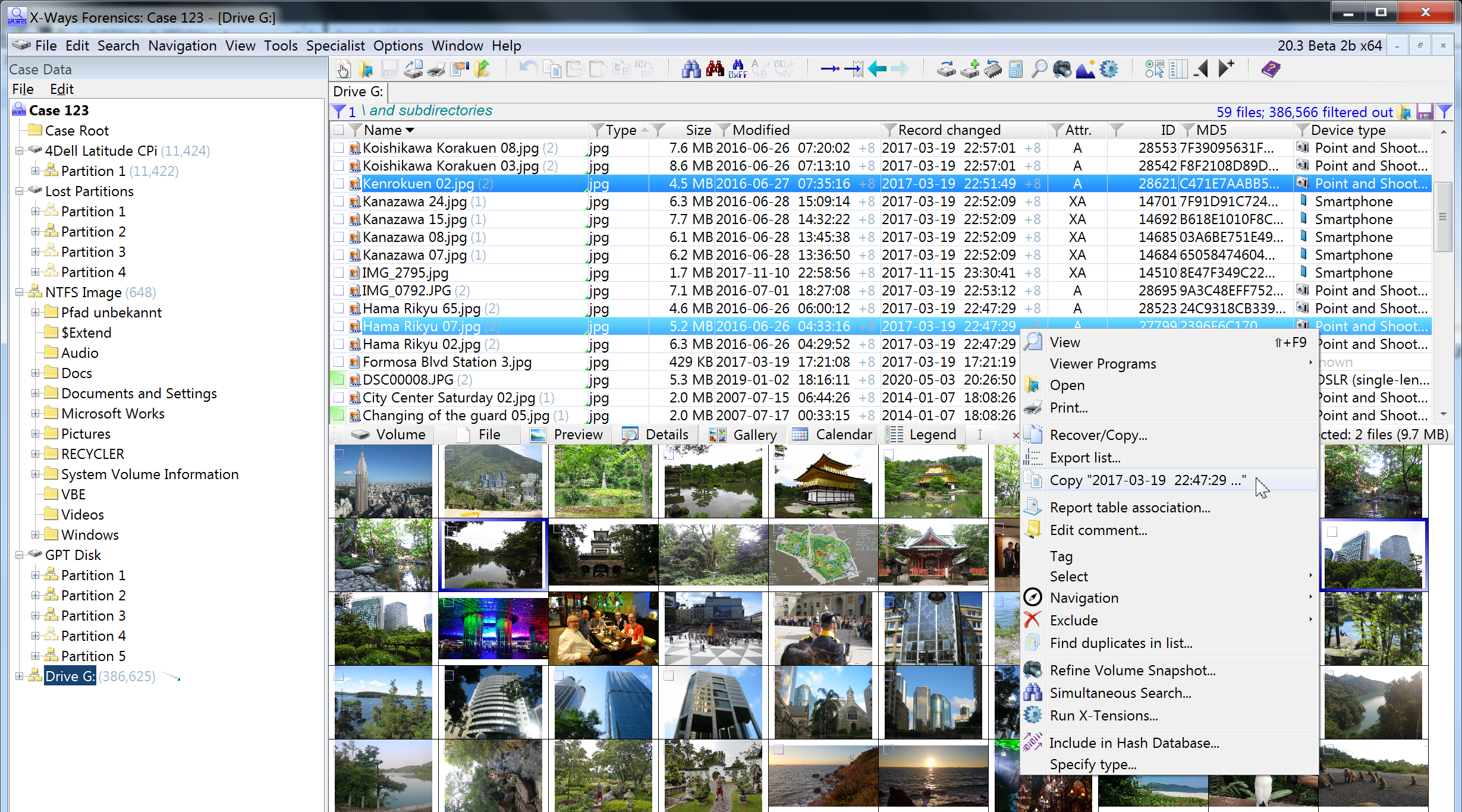
Commercial digital forensics platform for Windows.
X-Ways Investigator
Reduced and simplified version of X-Ways Forensics for police investigators, lawyers, and auditors.
F-Response

Forensic acquisition tool with a remote network drive analysis capability, remote RAM access, and cloud storage access.
Analysis Tools
AccessData Forensics Toolkit (FTK)
Well-known tool built for speed, stability and ease of use. It provides comprehensive processing and indexing up front, so filtering and searching is faster than with any other product. This means you can zero in on the relevant evidence quickly, dramatically increasing your analysis speed.
OpenText EnCase

Commercial forensics platform that allows evidence collection from over twenty-five different types of devices, including desktops, mobile devices and GPS.
E3 Digital Forensic Software
Paraben’s digital forensic platform focused on the entire forensic exam process.
Bulk Extractor
Forensic tool that extracts artifacts such as email addresses, credit card numbers, URLs, and other types of information from digital evidence files.
Registry Recon

Powerful computer forensics tool, developed by Arsenal Recon, useful for extract, recover, and parse registry data from Windows systems.
Memory Forensics
Volatility
THE memory forensics framework. It is used for incident response and malware analysis, in order to extract information from running processes, network sockets, network connection, DLLs and registry hives. It also has support information extraction from Windows crash dump files and hibernation files.
Redline
A FireEye’s security tool that provides memory and file analysis features: it collects information about running processes on a host, drivers from memory and gathers other data like meta data, registry data, tasks, services, network information and internet history.
WindowsSCOPE
Commercial memory forensics and reverse engineering tool used for analyzing volatile memory. It provides the ability to analyze the Windows kernel, drivers, DLLs and virtual and physical memory.
Network Forensics
Wireshark
The most widely used network traffic analysis tool, with the ability to capture live traffic or ingest a saved capture file.
Network Miner

Open source Network Forensic Analysis Tool (NFAT) for Windows, Linux, macOS X , and FreeBSD. NetworkMiner can be used as a passive network sniffer/packet capturing tool in order to detect operating systems, sessions, hostnames, and open ports without putting any traffic on the network.
Xplico
Open source network forensic analysis tool, that allows extraction of useful data from applications which use Internet and network protocols.