My Weekly Roundup #149
Cybersecurity
ITG23 Crypters Highlight Cooperation Between Cybercriminal Groups

IBM Security X-Force researchers have continually analyzed the use of several crypters developed by the cybercriminal group ITG23, also known as Wizard Spider, DEV-0193, or simply the “Trickbot Group”.
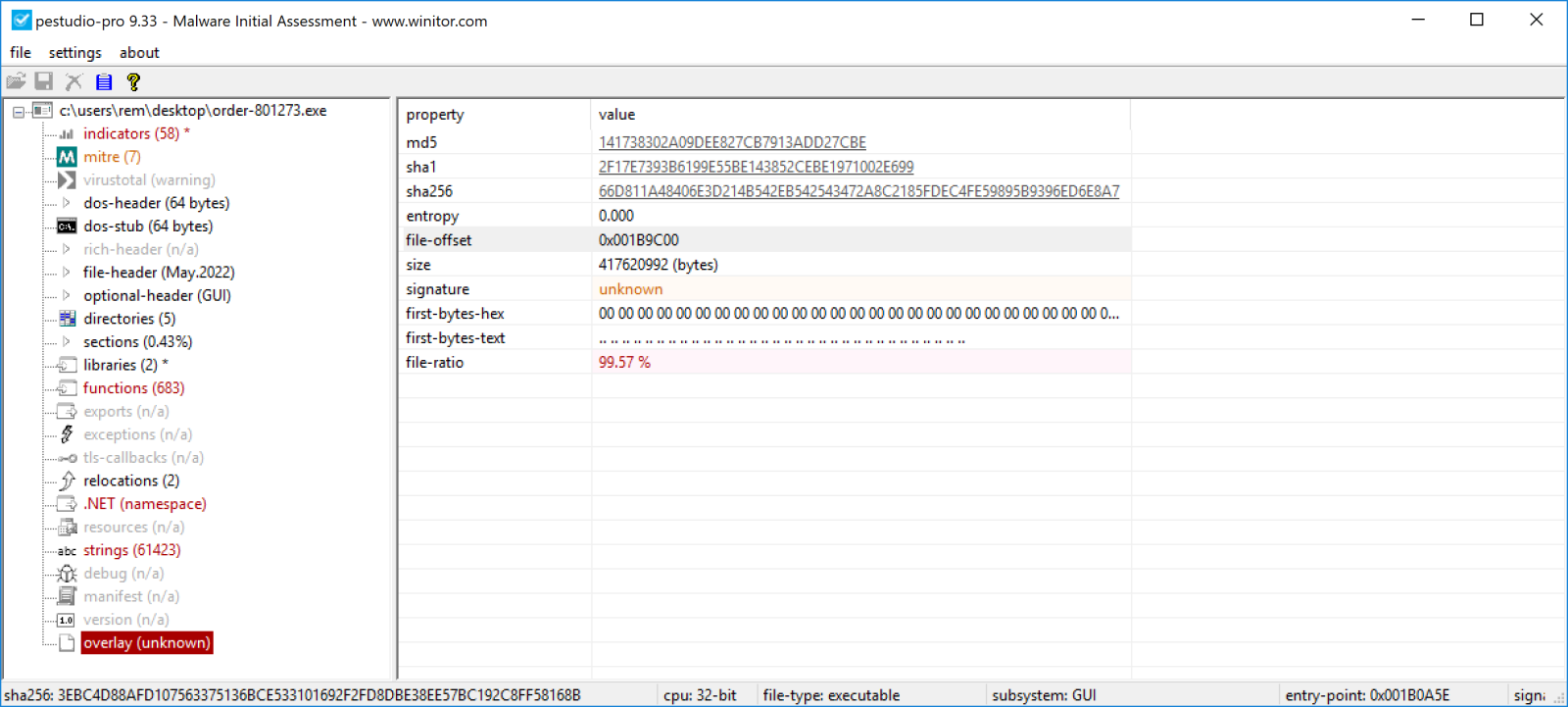
InfoSec Handlers Diary Blog
Yesterday, I analyzed a malicious archive for a customer. It was delivered to the mailbox of a user who, hopefully, was security-aware and reported it. The payload passed through the different security layers based on big players on the market!
Conti Ransomware Shuts Down and Rebrands Itself
The infamous ransomware gang known as the Conti group has effectively brought an end to their operation by taking their infrastructure down and informing their team leaders that the brand no longer exists.
Pro-Russian Hackers Hit Critical Government Websites in Italy

Pro-Russian hackers have targeted the websites of various Italian institutions and government ministries, law enforcement said on Friday. The attack, which began on Thursday evening and was still in progress as of Friday early afternoon, was reportedly confirmed by Italy’s Postal Police.
Cozy Smuggled Into the Box: APT29 Abusing Legitimate Software for Targeted Operations in Europe
Cozy Bear (aka Nobelium, APT29, The Dukes) is a well-resourced, highly dedicated and organized cyberespionage group that is believed to work in support of the decision-making process of Russian government since at least 2008.
iOS 15.5: Apple Urges iPhone Users To Update Now For Cool New Upgrades

Here we go, the last update of iOS 15, almost certainly, before attention turns to iOS 16. Unless there’s a hiccup, of course, we can never rule those out. It’s not a big update, but it has some neat features and it’ll download quickly.
Venezuelan cardiologist charged with designing and selling ransomware
The US Attorney’s Office has charged a 55-year-old cardiologist with creating and selling ransomware and profiting from revenue-share agreements with criminals who deployed his product.
A Look Into Public Clouds From the Ransomware Actor’s Perspective

Traditional ransomware mainly targets on-premises IT infrastructure but doesn’t work well in cloud environments, which is one reason we haven’t heard much about ransomware in public clouds.
Fake Mobile Apps Steal Facebook Credentials, Cryptocurrency-Related Keys

We have already submitted this app to Google for investigation. Facestealer apps are disguised as simple tools — such as virtual private network (VPN), camera, photo editing, and fitness apps — making them attractive lures to people who use these types of apps.
Exfiltrating data from a restricted Windows environment using DNS
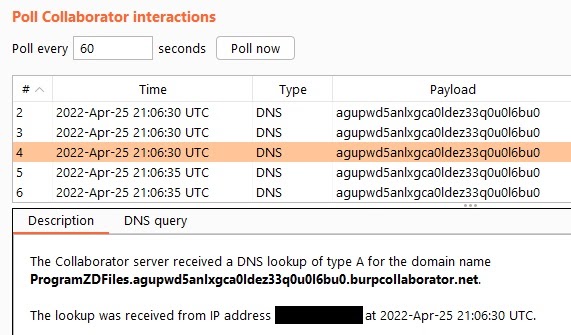
This post aims to show you how i was able to perfom an initial reconnaissance within the operating system without the need to rely on other tools such as PowerShell, certutil or Living Off The Land (LOLBIN) binaries.
Technology
The same phone for 25 years? iFixit on right to repair’s remaining obstacles, hope

The fight for the right to repair remains an active battle as various companies and lawmakers claim worries around safety, cybersecurity, and design innovation.
Microsoft founder Bill Gates uses a Samsung Galaxy Z Fold 3 instead of a Surface Duo

During a Reddit AMA this week, Microsoft’s founder Bill Gates revealed he uses an Android phone with a big canvas, but it isn’t Microsoft’s own Surface Duo. Instead, Bill Gates uses a Galaxy Z Fold 3 as his daily smartphone.
Gurman: iOS 16 to Include New Ways of System Interaction and ‘Fresh Apple Apps’

Users have long-hoped that Apple would bring interactive widgets to iOS ever since widgets were revamped with iOS 14. Widgets were mostly untouched with iOS 15 and remain non-interactive, so there is some hope significant widget changes could be in store for iOS 16.
Privacy
Canadians in the dark about how their data is collected and used, report finds
For more than one decade, Kurt Wimmer was this blog and this blogger’s First Amendment defender, representing me pro bono.
I/O 2022: Android 13 security and privacy (and more!)

Every year at I/O we share the latest on privacy and security features on Android. But we know some users like to go a level deeper in understanding how we’re making the latest release safer, and more private, while continuing to offer a seamless experience.
Entertainment
Easter Eggs In The She-Hulk Trailer You Probably Missed

The trailer for “She-Hulk: Attorney at Law” is finally here, and fans have been pouring over every frame of it since its debut, looking for the hints and teases that the creators have stuffed into the much-anticipated series.
Music
Vangelis wasn’t just a film composer – he blew apart the boundaries of pop

Greek pop music of the 1960s is not an area of musical history where anyone who doesn’t fondly remember it first-hand is advised to dwell.