My Weekly Roundup #156
Cybersecurity
Killnet: Russian DDoS Group Claims Attack on US Congress Website

On July 8, the Russian hacktivist DDoS group “Killnet” claimed responsibility for an attack on the website of US Congress. A Library of Congress spokesperson told CyberScoop that the distributed denial of service (DDoS) attacks “briefly affected public access” on July 7.
Microsoft rolls back plan to block macros by default
Back in February I applauded Microsoft for taking a decisive step in the fight against macro malware. Here’s part of what I wrote: Microsoft has announced that… it is changing the default behavior of Office applications so that they block macros in files from the internet.
New 0mega ransomware targets businesses in double-extortion attacks
A new ransomware operation named ‘0mega’ targets organizations worldwide in double-extortion attacks and demands millions of dollars in ransoms.
Free decryptor released for AstraLocker, Yashma ransomware victims

New Zealand-based cybersecurity firm Emsisoft has released a free decryption tool to help AstraLocker and Yashma ransomware victims recover their files without paying a ransom.
Unprecedented Shift: The Trickbot Group is Systematically Attacking Ukraine

Following ongoing research our team, IBM Security X-Force has uncovered evidence indicating that the Russia-based cybercriminal syndicate “Trickbot group” has been systematically attacking Ukraine since the Russian invasion — an unprecedented shift as the group had not previously targeted Ukra
OrBit: New Undetected Linux Threat Uses Unique Hijack of Execution Flow
Linux is a popular operating system for servers and cloud infrastructures, and as such it’s not a surprise that it attracts threat actors’ interest and we see a continued growth and innovation of malware that targets Linux, such as the recent Symbiote malware that was discovered by our research
Targets of Interest | Russian Organizations Increasingly Under Attack By Chinese APTs
Executive Summary SentinelLabs has identified a new cluster of threat activity targeting Russian organizations. We assess with high-confidence that the threat actor responsible for the attacks is a Chinese state-sponsored cyber espionage group, as also recently noted by Ukraine CERT (CERT-UA).
Security advisory accidentally exposes vulnerable systems

A security advisory for a vulnerability (CVE) published by MITRE has accidentally been exposing links to remote admin consoles of over a dozen vulnerable IP devices since at least April 2022.
Apple announces ‘Lockdown Mode’ to counter spyware
Apple previewed a hardened “Lockdown Mode” on Wednesday that’s designed to thwart sophisticated attackers, including spyware sold to governments. Lockdown Mode will be rolled out this fall with macOS Ventura, iOS 16, and iPadOS 16.
Hive Ransomware Upgrades to Rust for More Sophisticated Encryption Method
The operators of the Hive ransomware-as-a-service (RaaS) scheme have overhauled their file-encrypting software to fully migrate to Rust and adopt a more sophisticated encryption method.
New RedAlert Ransomware targets Windows, Linux VMware ESXi servers

A new ransomware operation called RedAlert, or N13V, encrypts both Windows and Linux VMWare ESXi servers in attacks on corporate networks. The new operation was discovered today by MalwareHunterTeam, who tweeted various images of the gang’s data leak site.
When Pentest Tools Go Brutal: Red-Teaming Tool Being Abused by Malicious Actors
Unit 42 continuously hunts for new and unique malware samples that match known advanced persistent threat (APT) patterns and tactics. On May 19, one such sample was uploaded to VirusTotal, where it received a benign verdict from all 56 vendors that evaluated it.
Researchers Share Techniques to Uncover Anonymized Ransomware Sites on Dark Web
Cybersecurity researchers have detailed the various measures ransomware actors have taken to obscure their true identity online as well as the hosting location of their web server infrastructure.
InfoSec Handlers Diary Blog

A quick search on Shodan Trends shows us that although the situation has gotten much better over the last few years, and it still seems to be slowly improving, more than 5,000 vulnerable machines (exactly 5,565 at the time of writing) are still accessible from the internet.
Technology
TensorFlow Lite – On A Commodore 64
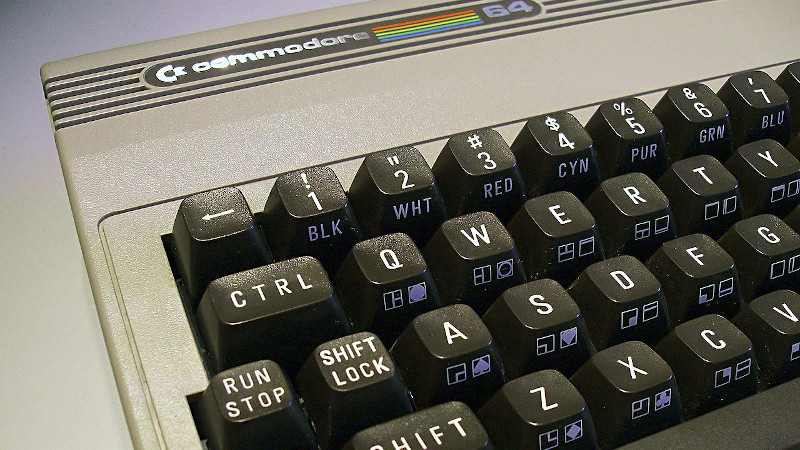
TensorFlow is a machine learning and AI library that has enabled so much and brought AI within the reach of most developers. But it’s fair to say that it’s not for the less powerful computers.
Privacy
For the Love of the Wild Web 🖤
![]()
There is a traditional Japanese concept called wabi-sabi that recognizes the world as impermanent, evolving, and unfinished. You could call it the beauty of embracing imperfection.
Music
A Rock Star Lost His Guitar 46 Years Ago in Toronto. He Just Found It in Tokyo.

Having worked odd jobs as a teenager to save up for the pumpkin orange electric Gibson, then 32-year-old Bachman was heartbroken. On tour, he’d been diligent about shackling the guitar to hotel room toilets with tow truck chains whenever he left the room.