My Weekly Roundup #159
Cybersecurity
Microsoft ties novel ‘Raspberry Robin’ malware to Evil Corp cybercrime syndicate
Microsoft’s security team published evidence this week tying the Raspberry Robin malware to Russian cybercrime syndicate Evil Corp.
New Qualys Research Report: Evolution of Quasar RAT

The Qualys Threat Research Team continues to inform enterprise cybersecurity teams of emerging threats that could impact their business. These threat intelligence reports summarize individual threat exploits and provide practical recommendations for protecting against them.
Examining New DawDropper Banking Dropper and DaaS on the Dark Web

In this blog post, we discuss the technical details of a new banking dropper that we have dubbed DawDropper, give a brief history of banking trojans released in early 2022 that use malicious droppers, and elaborate on cybercriminal activities related to DaaS in the deep web.
Decentralized IPFS networks forming the ‘hotbed of phishing’

Threat groups are increasingly turning to InterPlanetary File System (IPFS) peer-to-peer data sites to host their phishing attacks because the decentralized nature of the sharing system means malicious content is more effective and easier to hide.
The commercial satellite boom is leaving space vulnerable to hackers
Humanity’s imagination turned toward the heavens this month as the James Webb Space Telescope revealed images of distant galaxies.
Critical Samba bug could let anyone become Domain Admin – patch now!

Samba is a widely-used open source toolkit that not only makes it easy for Linux and Unix computers to talk to Windows networks, but also lets you host a Windows-style Active Directory domain without Windows servers at all.
Untangling KNOTWEED: European private-sector offensive actor using 0-day exploits
The Microsoft Threat Intelligence Center (MSTIC) and the Microsoft Security Response Center (MSRC) found a private-sector offensive actor (PSOA) using multiple Windows and Adobe 0-day exploits, including one for the recently patched CVE-2022-22047, in limited and targeted attacks against European an
DHL Phishing Page Uses Telegram Bot for Exfiltration
One of the quickest ways for an attacker to harvest financial data, credentials, and sensitive personal information is through phishing.
Malicious IIS extensions quietly open persistent backdoors into servers

Attackers are increasingly leveraging Internet Information Services (IIS) extensions as covert backdoors into servers, which hide deep in target environments and provide a durable persistence mechanism for attackers.
Russian Ransomware C2 Network Discovered in Censys Data
Around June 24 2022, out of over 4.7 million hosts Censys observed in Russia, Censys discovered two Russian hosts containing an exploitation tool, Metasploit, and Command and Control (C2) tool, Deimos C2. Historical analysis indicated one of these Russian hosts also used the tool PoshC2.
Biden administration sets cyber priorities for fed agencies in ’24
The Biden administration late last week issued guidance that laid out the cybersecurity funding priorities that federal agencies should adhere to for the upcoming fiscal year 2024 budget cycle.
Top 5 Security Trends this Summer: RSA Conference & Black Hat 2022
The RSA Conference 2022 – one of the world’s premier IT security conferences – was held June 6th-9th in San Francisco. The first in-person event for RSA since the global pandemic had a slightly lower turnout than in years past (26,000 compared to 36,000 attendees).
LockBit Ransomware Group Augments Its Latest Variant, LockBit 3.0, With BlackMatter Capabilities

In June 2022, LockBit revealed version 3.0 of its ransomware. In this blog entry, we discuss the findings from our own technical analysis of this variant and its behaviors, many of which are similar to those of the BlackMatter ransomware.
Lockbit ransomware gang claims to have breached the Italian Revenue Agency

The ransomware group Lockbit claims to have stolen 78 GB of files from the Italian Revenue Agency (Agenzia delle Entrate).
Flaws in FileWave MDM could have allowed hacking +1000 organizzations

Multiple flaws in FileWave mobile device management (MDM) product exposed organizations to cyberattacks. Claroty researchers discovered two vulnerabilities in the FileWave MDM product that exposed more than one thousand organizations to cyber attacks.
IAM-Deescalate: An Open Source Tool to Help Users Reduce the Risk of Privilege Escalation

In the recent Cloud Threat Report, Unit 42 researchers analyzed more than 680,000 identities across 18,000 cloud accounts from 200 different organizations and found that 99% of cloud users, roles and service accounts are overly permissive.
Technology
Thunderbird 102.1.0 fixes four security issues in the email client
Thunderbird 102.1.0 is now available. The new stable version of the email client patches four security issues in the application and makes some minor changes next to that. Thunderbird 102.1.0 is already available.
How Google will speed up the Lacros browser on Chromebooks
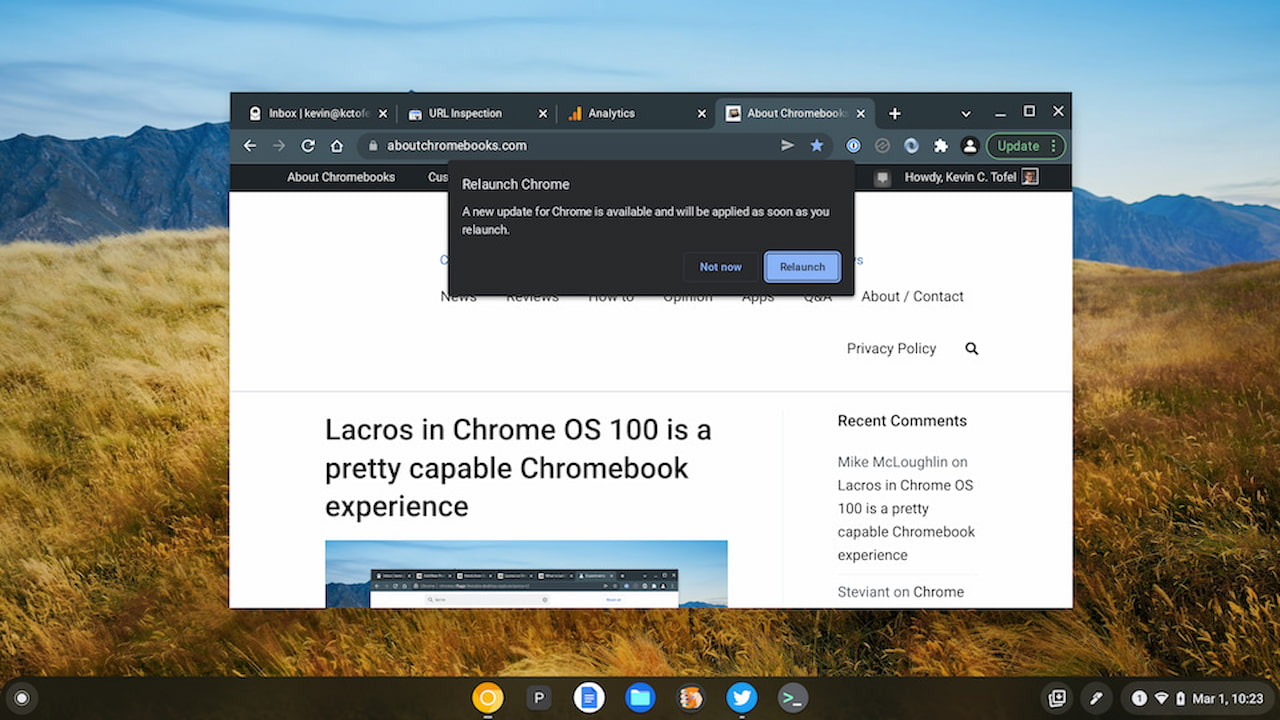
A few months back, I mentioned that I’m using the Lacros browser full-time. Lacos is essentially the Linux version of the Chrome browser and is part of Google’s effort to decouple Chrome from ChromeOS. Today I found code that will eliminate one of my pain points using Lacros.
Privacy
T-Mobile to Pay $500 Million to Settle Claims Related to 2021 Breach
On July 22, 2022, T-Mobile entered into an agreement to settle a class action lawsuit stemming from its 2021 data breach. The breach involved the personal information of 76.6 million U.S. residents and was T-Mobile’s fifth breach over a four year period.
Entertainment
Music
Blue Note Jazz Festival Debuts in Napa Valley With Robert Glasper, Snoop Dogg, Dave Chappelle & More

The Blue Note Jazz Festival in Napa Valley, Calif., kicks off Friday (July 29) with host Dave Chappelle and Grammy-winning instrumentalist Robert Glasper as artist in residence.