SwiftSlicer: a new Golang-based wiper malware
Cyber security firm ESET has reported that Ukraine has been hit by a new cyber attack from Russia using a previously undocumented data wiper called SwiftSlicer.
The attack has been attributed to Sandworm, a nation-state group linked to Military Unit 74455 of the Main Intelligence Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU).
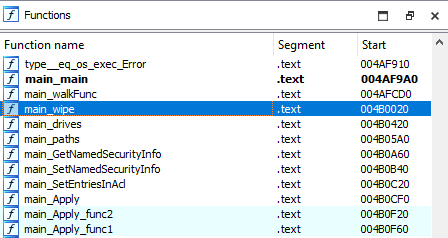
The malware, which is written in the Golang programming language, is designed to delete shadow copies, recursively overwrite files located in certain system directories, and reboot the infected computer. The overwriting of files is achieved by using randomly generated byte sequences to fill 4,096 byte-length blocks.
Sandworm, also known as BlackEnergy, Electrum, Iridium, Iron Viking, TeleBots and Voodoo Bear, has a history of conducting disruptive and destructive cyber campaigns against organisations worldwide since at least 2007: has targeted industrial control systems using a tool called Black Energy for espionage, denial of service, and data destruction purposes. Furthermore, Sandworm has been linked to NotPetya malware attacks and is listed as a threat actor on MITRE ATT&CK.
The discovery of SwiftSlicer demonstrates the Russian adversary collective’s consistent use of wiper malware variants in attacks designed to wreak havoc in Ukraine.
Indicator of compromise
| SHA256 |
|---|
| 7346E2E29FADDD63AE5C610C07ACAB46B2B1B176 |