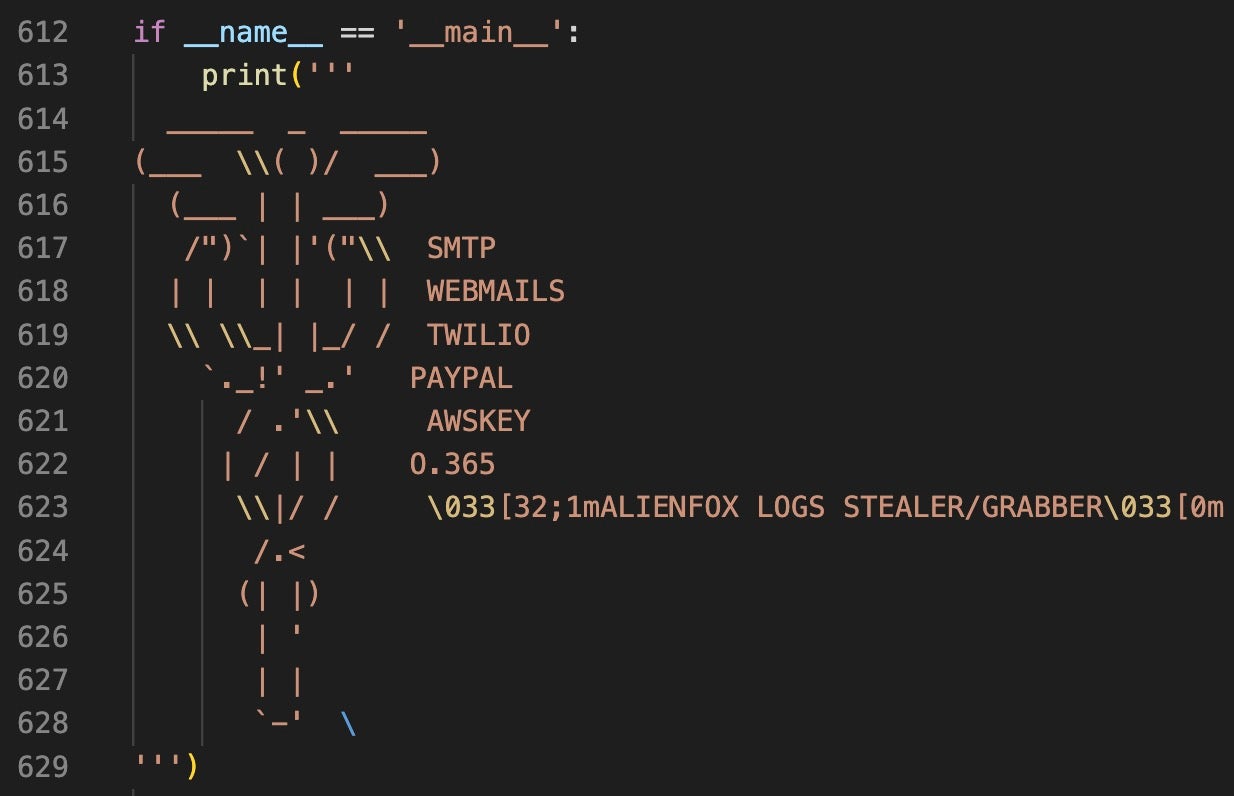
AlienFox: Unraveling the Multi-Functional Cloud Spammer's Swiss Army Knife
In a comprehensive analysis published by SentinelOne Labs, researchers dissect the inner workings of AlienFox, a highly versatile and multi-functional malware highlighting its features and the risks it poses.
What is AlienFox?
AlienFox is a highly adaptable and multi-purpose cyber weapon, designed by its creators to serve as a “Swiss Army Knife” for various cybercriminal activities. Its primary function is to facilitate cloud-based spamming campaigns, but it also comes equipped with a wide range of other capabilities. These include remote access tools (RAT), keylogging, data theft, and even DDoS attack capabilities.
How Does AlienFox Operate?
The SentinelOne Labs report outlines the various stages of AlienFox’s operations, which are typically initiated through phishing emails containing malicious attachments or links. Once executed, AlienFox establishes a foothold in the victim’s system and communicates with its command and control (C2) server. It then proceeds to download additional payloads and modules, depending on the specific objectives of the attackers.
The malware’s versatility is due to its modular design, allowing it to be easily updated with new features and capabilities. This ensures that AlienFox remains an effective tool for cybercriminals, as it can adapt to changing security measures and landscapes.
Some Key Features of AlienFox
The researchers at SentinelOne Labs have identified several key features of AlienFox, which include:
-
Cloud-based spamming: AlienFox is designed to leverage cloud services such as Google Drive and OneDrive to spread spam emails. This allows the attackers to bypass traditional email filtering systems and increase the likelihood of their phishing emails reaching their intended targets.
-
Remote Access: AlienFox functions as a Remote Access Trojan (RAT), allowing the attackers to gain complete control over the infected system. This can be used to monitor the victim’s activities, steal sensitive data, or conduct other malicious activities.
-
Keylogging: The malware is capable of capturing keystrokes, potentially allowing the attackers to gain access to sensitive information such as login credentials and personal data.
-
Data Theft: AlienFox can search for and exfiltrate specific types of files from the victim’s system, including documents, images, and even cryptocurrency wallet files.
-
DDoS Attack Capabilities: While not its primary focus, AlienFox has the ability to launch distributed denial of service (DDoS) attacks, potentially crippling targeted websites or network infrastructure.
Indicators of Compromise
| SHA/URL |
|---|
| e786fc1fdfcb7be28650383eb33cdf6c90f1d033 |
| 8e6e18ba7e251d31b46d17535010a8c583345b23 |
| b3559eeac9a9caa840cc96980fe0bbd1c7da37d3 |
| 40df29a738fd5cab0face169d8a8426dff7d2d10 |
| e663e24fc6aadbaae5bbf722a84097a6127f4066 |
| c2f51b44e26e4aca40beb887ac4d36f3e091e26a |
| 4266bdb139ae6d22ddf98501cc3af280aa488b42 |
| 329328dc57acece8c47ab5c73f7b9c7e4e09981a |
| fc08c15dfd6074d80e1f8d777fb49f8c14b4af20 |
| aa4672621f81f601882ad13f26d37dc8218bb06a |
| 07289c56e65a98a85bc794374949aae98b819823 |
| 4ab401d4c490460fd457151f643b5ec7e594cd41 |
| 7848e53133f4470c29e33ee6dd87f8f326c5fa38 |
| 7d7bad6282531521b9103817a38bff3a34b89428 |
| 15129436f5bab6c3eea9b2dfc4d0f0043438e013 |
| 15aec55e56225700766d79b6fb9d212cced21951 |
| ebdc60f33d22c4256ca6ab4058059db1d618ec11 |
| 894fd799168f9ff11e74ee37d5bec35387feef24 |
| 28de7d7fcd18471f53737fd8a3df3a23a34cf758 |
| 3ddb8dc53b6151ea036db3d2a5f34e5f5b39e044 |
| ceda47dd1aacc515d8bdda04299ab1ebf1ba0d73 |
| 23abd146befe761337e5155a116138acf81331d9 |
| ac265c12a4f08378e2519e290b0c45a1adc7156f |
| b8dc12cc600aced9d34c463c5bf5edb53db605fb |
| 45a0675088afdcf2ec059510fc2a4905957c2a69 |
| c3464926cf2075595c77dc5b3fbcf1f014c8046b |
| fc0479a3d1188384613f437f28e28614a6118e94 |
| 5c9993e5d7468551c60e6dab488eccea7f4ef007 |
| ece7e6727d2daa254e4d4a6be62744d6f3a2a2ef |
| afb7b010bafb9f7faf2b528f128ff24da94e0190 |
| 959e377131762ccb879c36c53e3b71473d3b72fd |
| 48afb7ac8fdf6a8da47601806a8028c61dad2eb7 |
| hxxps[:]//rtvsmkqfa3clrvgj6f-9fd73c[.]ingress-daribow.easywp.com/wp-admin/v1/1.php |
| hxxps[:]//rentry[.]co/3cii9/raw |