CERT-EU's cyber threat intelligence framework: a common language for European digital defence
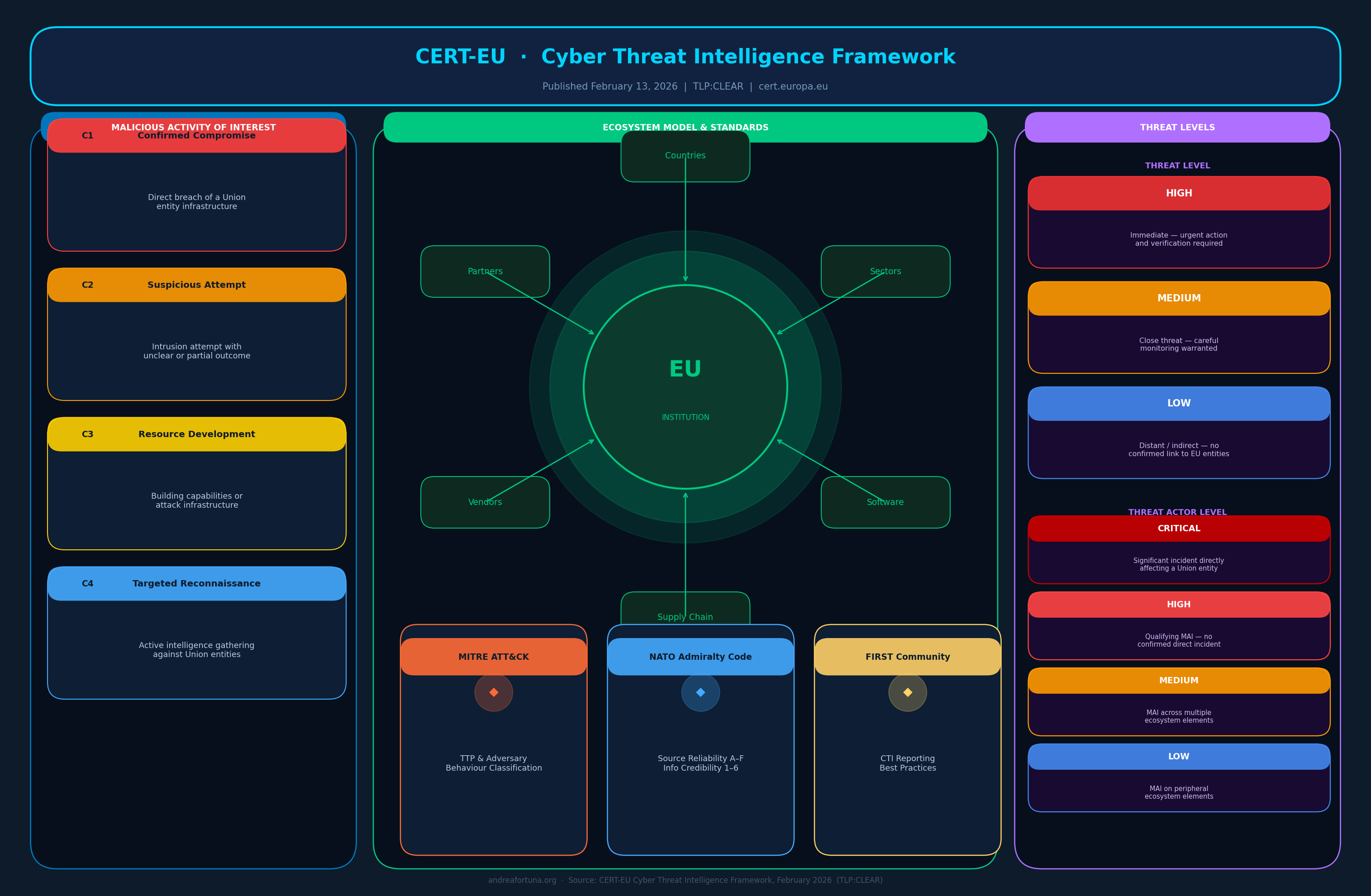
On February 13, 2026, CERT-EU (the Computer Emergency Response Team for the EU Institutions, Bodies and Agencies) released its Cyber Threat Intelligence Framework, a document that formalizes how the organization classifies, assesses, and prioritizes cyber threats relevant to European Union entities. Published under TLP:CLEAR and openly shared with the broader cybersecurity community, the framework is not merely a technical reference: it represents a deliberate effort to establish a shared methodological language that bridges the gap between raw technical analysis and operational decision-making.
The timing is significant. As geopolitical tensions continue to shape the digital threat landscape, and as regulations such as NIS2 and DORA push EU organizations toward more structured approaches to cyber risk management, the need for a coherent, institution-wide intelligence model has never been more pressing. The CERT-EU framework responds to this need by introducing structured concepts, consistent scoring, and clearly defined threat taxonomies, all calibrated to the specific context of Union entities.
Formalizing the intelligence process
At its core, the Cyber Threat Intelligence Framework defines the analytical and operational standards that CERT-EU uses across its publications, from individual Cyber Briefs to the annual Threat Landscape Report. The fundamental challenge it addresses is deceptively simple: intelligence is only useful if the people producing it and the people acting on it share the same understanding of what terms mean, how severity is measured, and which threats deserve immediate attention versus those requiring only monitoring.
By codifying definitions, scoring criteria, and classification hierarchies, the framework transforms what might otherwise be a subjective, analyst-dependent process into a repeatable and consistent methodology. Primary Operational Contacts (POCs) and Local Cybersecurity Officers (LCOs) at Union entities can now receive CERT-EU alerts knowing that the underlying assessments have been produced according to a transparent, documented standard, rather than relying on implicit institutional knowledge.
The framework is also conceived as a key enabler of what CERT-EU calls its Full-Spectrum Adversary Approach, an internal model for threat-informed defence that supports holistic modelling of threats across both strategic and technical dimensions. By making this approach explicit and reproducible, the framework strengthens situational awareness and ensures that observations translate into structured data capable of driving faster, more coherent operational responses.
The MAI concept and the ecosystem model
One of the framework’s most significant conceptual contributions is the introduction of the Malicious Activity of Interest (MAI) as the central analytical unit. Rather than focusing exclusively on confirmed incidents, an MAI encompasses a broader range of adversary behaviours: confirmed compromises, but also suspicious intrusion attempts, adversarial infrastructure development, and targeted reconnaissance. This expanded scope is deliberate, acknowledging that in modern threat environments, the early stages of an attack cycle carry intelligence value that should not be discarded before a formal incident has been confirmed.
Equally important is the framework’s ecosystem model. CERT-EU does not limit its analytical lens to direct attacks on EU institutions. Instead, it considers the broader environment in which Union entities operate: the countries in which they are active, the sectors they belong to, the software and services they rely on, and the supply chains that underpin their operations. This perspective reflects a crucial insight: a threat does not need to directly target an institution to be operationally relevant. A compromised supplier, a widely exploited vulnerability in commercial software used across EU bodies, or a campaign targeting a sector adjacent to Union entities can all carry systemic implications.
The ecosystem model translates into a more nuanced approach to threat relevance. When CERT-EU analysts assess an MAI, they consider not only whether Union entities are directly targeted, but also how many elements of the ecosystem are affected, and how those effects might cascade. A threat actor whose activity spans multiple ecosystem components will be rated more severely than one whose activity is isolated to a single, peripheral element, even if neither has yet caused a confirmed incident at a Union entity.
Threat levels, actor levels, and scoring
The framework introduces two structured scales designed to support consistent prioritization. The threat level scale assesses the criticality and proximity of malicious cyber activity in relation to Union entities: a “High” rating indicates an immediate threat requiring urgent verification and action, “Medium” signals a close threat warranting careful monitoring, and “Low” describes distant or indirect threats with no immediately identified link to Union entities. These levels are applied particularly in the Threat Alerts that CERT-EU provides to its constituents, guiding the urgency and scope of recommended mitigations.
Alongside this, a threat actor level scale classifies adversaries based on their observed behaviour during a defined period of interest. A “Critical” actor is one that has caused at least one significant incident directly affecting Union entities; a “High” actor has been responsible for a qualifying MAI that did not reach the threshold of a significant incident; “Medium” and “Low” actors are distinguished by the breadth of ecosystem elements their activity has touched. This granularity allows decision-makers to contextualize alerts within a broader picture of adversary behaviour over time, rather than reacting to isolated events without context.
Complementing these scales, the framework defines a scoring mechanism for both adversaries and mitigations. The threat score is driven by five components: occurrences, targeting, severity, time period, and a decay factor that progressively reduces the weight of older activity. The mitigation scoring draws on a formula that incorporates the coverage of adversary techniques by available controls, the number of initial access vectors addressed, and alignment with the Essential Eight baseline practices, providing a quantitative basis for defensive planning and resource allocation that goes well beyond intuition-based prioritization.
Standards and a European approach
A defining characteristic of the CERT-EU framework is its deliberate integration of established international standards rather than the development of new parallel ones. For the classification of adversary tactics, techniques, and procedures (TTPs), the framework adopts the MITRE ATT&CK knowledge base, a widely used, behaviour-based taxonomy that links observable adversary actions to known techniques, making threat-hunting and prioritized mitigation systematic and repeatable for analysts and defenders alike.
For the assessment of source reliability and information credibility, the framework employs the Admiralty Code, a NATO-standard system that evaluates these two dimensions independently. Source reliability is rated from A (completely reliable) to F (unreliable or untested), while information credibility runs from 1 (confirmed by multiple sources) to 6 (cannot be judged). Crucially, CERT-EU only uses intelligence that meets a specific threshold (A1, A2, B1, or B2 combinations), ensuring that CTI products are grounded in information from sources with a demonstrated track record and with sufficient corroboration or plausibility.
On the question of attribution, the framework adopts a strictly technical stance. CERT-EU does not attribute activity to states or organizations, focusing instead on identifying threat actors through observable technical indicators such as TTPs, infrastructure overlaps, malware artefacts, and targeting patterns. When attribution to a known threat actor proves impossible, the framework designates an Unattributed Threat Actor (UTA) with a numeric suffix (for example, UTA-53), which can later be merged with a known actor or another UTA as additional evidence emerges. This approach, consistent with the best practices promoted by the FIRST community for CTI reporting, ensures that attribution claims remain defensible, evidence-based, and revisable as the analytical picture develops.
A living document for a changing landscape
CERT-EU has explicitly designed the framework as a dynamic document rather than a static reference. The threat environment changes constantly: new geopolitical pressures emerge, technologies evolve, and regulatory frameworks are updated. The Cyber Threat Intelligence Framework is intended to evolve in step with these shifts, and the organization has published it under TLP:CLEAR precisely to invite feedback from peers and cybersecurity professionals across the broader community. This openness to external input is itself a statement of intent: effective threat intelligence is a collective endeavour, not a closed institutional exercise.
The implications of the framework extend well beyond the walls of EU institutions. National administrations, public bodies, and private organizations that work in cooperation with Union entities, including those already engaged in information-sharing initiatives coordinated through ENISA, now have a shared reference point for aligning their own intelligence processes. Not by replacing their existing frameworks, but by adopting compatible terminology, confidence scales, and scoring approaches that enable genuine interoperability. In a landscape where cyber threats routinely cross organizational and national boundaries, this kind of methodological alignment is a prerequisite for effective collective defence and for the shared situational awareness that complex, interconnected environments increasingly demand.