Privileged access management: risks and best practices for zero trust implementations
The strategic weight of privileged accounts
In any enterprise environment, privileged accounts represent the highest-value target for attackers. These are not just administrator credentials; they encompass service accounts, DevOps pipelines, cloud management interfaces, and any identity with elevated permissions over critical systems. When one of these accounts is compromised, the consequences extend far beyond a single machine or dataset. Attackers can move laterally, escalate privileges, and reach the deepest layers of an organization’s infrastructure, often without triggering immediate alerts.
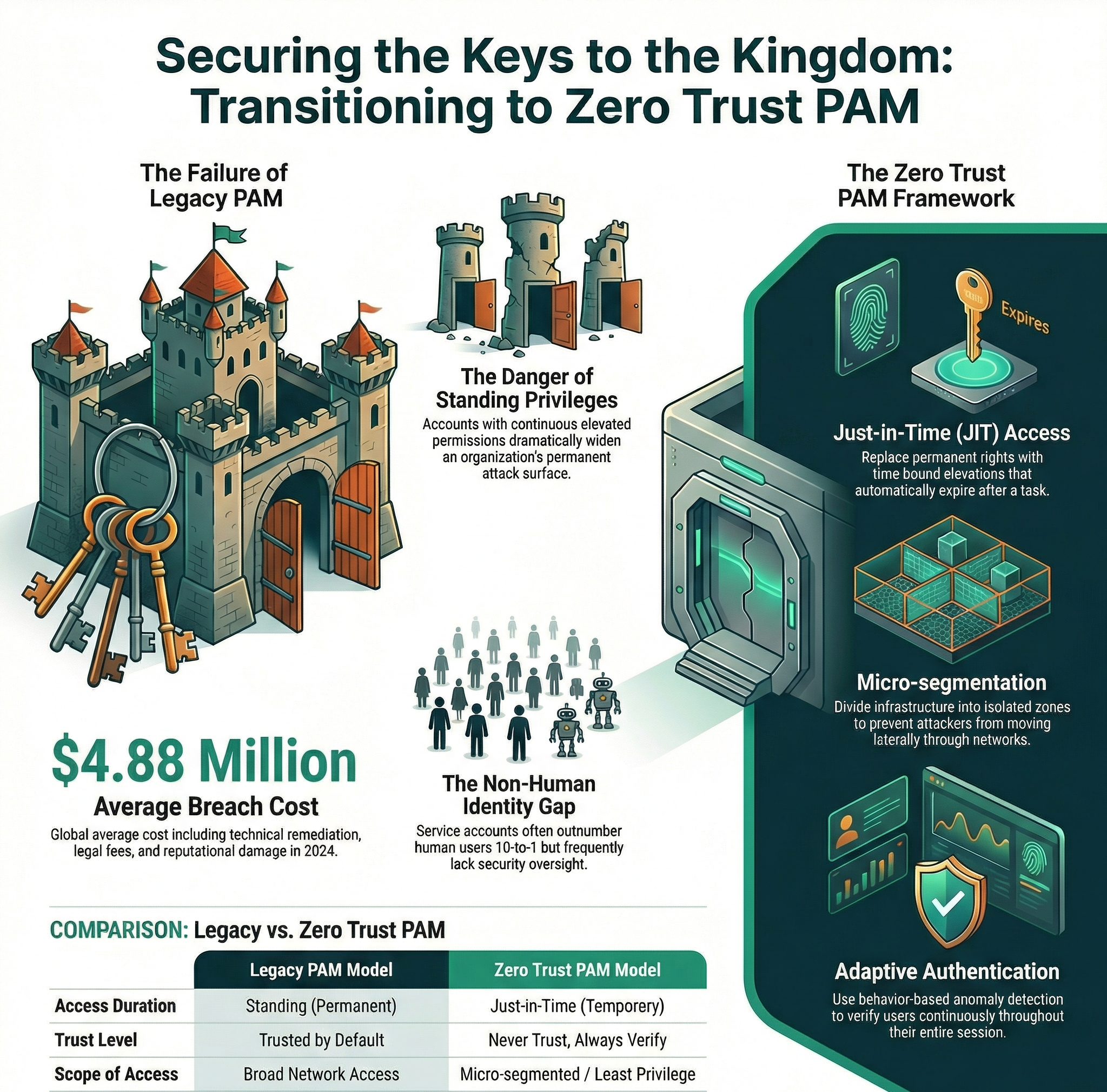
The numbers behind this threat are stark. According to research cited by Keeper Security, the global average cost of a data breach in 2024 reached $4.88 million, a figure that reflects not only the technical remediation but also legal fees, regulatory fines, and lasting reputational damage. The 2024 AT&T breach, which exposed data from more than 65 million former customer accounts, stands as a recent and instructive example of what happens when privileged access is left poorly managed on third-party cloud environments.
These incidents rarely originate from sophisticated zero-day exploits. In the majority of cases, the initial vector is a stolen or misused credential. Attackers rely on phishing, credential stuffing, or exploiting improperly decommissioned accounts to gain a foothold. Once inside, the presence of excessive or poorly monitored privileges allows them to escalate quickly and operate undetected for extended periods. The longer an attacker maintains access, the more costly the breach becomes, both in terms of direct financial impact and long-term erosion of customer trust.
Privileged Access Management (PAM) addresses this problem by establishing structured controls over who can access sensitive systems, under what conditions, and for how long. But PAM alone is no longer sufficient. The modern threat landscape demands that it be combined with the principles of Zero Trust, a security model built on the premise that no user, device, or network segment should ever be trusted by default.
Why traditional PAM models fall short
Legacy PAM implementations were designed for a different era: perimeter-based networks where internal users were generally considered trustworthy, and where administrative access was granted on a semi-permanent basis to a small number of system administrators. That model has not survived contact with cloud adoption, remote work, and the explosion of non-human identities in modern IT environments.
One of the most persistent weaknesses in traditional PAM is the concept of standing privileges: accounts that retain elevated permissions continuously, regardless of whether those permissions are actively needed. This approach dramatically widens the attack surface. A compromised account with standing admin rights is immediately dangerous, while a credential with no active privileges at the moment of breach offers an attacker far less leverage.
The problem becomes even more acute in hybrid and multi-cloud environments, where privileged accounts often span multiple platforms with different security models and management interfaces. An administrator who holds standing privileges across AWS, Azure, and on-premises Active Directory presents a single point of failure that, if compromised, grants an attacker access to the organization’s entire technology stack. Without centralized visibility and policy enforcement, security teams are forced to manage these risks in silos, inevitably leaving gaps.
Shadow IT compounds the problem further. Many organizations simply do not have a complete inventory of their privileged accounts. Shared credentials, dormant service accounts, and unmonitored automation pipelines create blind spots that security teams cannot defend. As Splashtop’s analysis of PAM challenges highlights, the lack of automated discovery and continuous classification of privileged accounts is one of the most common and dangerous gaps organizations face today.
Zero Trust as the architectural backbone
The Cloud Security Alliance defines Zero Trust PAM around three foundational assumptions: breaches will occur, trust must be continuously verified, and authentication must be adaptive and context-aware. These principles transform PAM from a static gatekeeping function into a dynamic, risk-responsive framework.
At the operational level, this translates into several concrete practices. Just-in-Time (JIT) access replaces standing privileges with time-bound elevations that are provisioned only when a specific task requires them and revoked automatically once the task is complete. A DevOps engineer, for instance, might be granted temporary root access for a deployment window of thirty minutes, after which the privilege is automatically removed. This model, endorsed by the CISA Zero Trust Maturity Model, shrinks the window of opportunity for attackers to exploit compromised credentials.
Multi-Factor Authentication, particularly phishing-resistant implementations such as FIDO2 hardware tokens and passkeys, adds another layer of defense. Combined with behavior-based anomaly detection, which can flag an administrator logging in from an unrecognized geolocation or accessing systems outside of business hours, adaptive authentication ensures that the verification process is not a one-time event at login but a continuous assessment throughout each session.
Micro-segmentation reinforces these access controls at the network level. By dividing the infrastructure into isolated security zones, each with its own access policies, organizations can contain the impact of a compromised privileged account. Even if an attacker gains elevated access to one segment, micro-segmentation prevents unrestricted lateral movement to other parts of the network. When combined with JIT provisioning and continuous authentication, micro-segmentation creates a layered defense architecture where each layer independently limits the attacker’s reach.
An often overlooked component of Zero Trust PAM is the principle of least privilege by design. Rather than granting broad access and later attempting to restrict it, organizations should define the absolute minimum set of permissions required for each role and function from the outset. This inversion of the default, from “allow unless denied” to “deny unless explicitly allowed”, fundamentally changes the security posture of the organization and reduces the blast radius of any single compromised identity.
Integrating PAM with the broader security ecosystem
PAM does not operate effectively in isolation. Its value multiplies when integrated with Identity Governance and Administration (IGA) systems, Access Management platforms, and Security Information and Event Management (SIEM) tools. This integration creates a unified audit trail across all user activities, privileged and otherwise, enabling security teams to correlate events, detect lateral movement, and respond to incidents with the context they actually need.
The treatment of non-human identities is a particularly critical and often underestimated dimension of this ecosystem. Service accounts, API keys, machine-to-machine tokens, and automated pipelines frequently carry elevated permissions and are rarely subject to the same scrutiny as human users. In many organizations, non-human identities outnumber human users by a factor of ten or more, yet they receive a fraction of the security attention. An attacker who compromises a service account can blend into legitimate traffic patterns, moving through cloud environments and on-premises networks with minimal detection risk.
Applying Zero Trust principles to these identities requires a dedicated strategy. Credentials for service accounts and API integrations should be rotated automatically on a short lifecycle, ideally through a secrets management platform that eliminates the need for hard-coded credentials in source code or configuration files. Each non-human identity should be scoped to the minimum set of permissions required for its function, and its activity should be monitored continuously for deviations from established baselines. Organizations that treat non-human identities as second-class citizens in their PAM strategy are leaving one of their largest attack surfaces effectively unguarded.
Insider threats require their own layer of attention. The danger does not come only from malicious actors; negligence and misconfiguration account for a significant share of privilege-related incidents. Duo Security’s research on PAM risks emphasizes that even well-designed PAM strategies can introduce new vulnerabilities if they are inconsistently monitored or poorly maintained, underscoring the need for continuous oversight rather than periodic audits.
Building a resilient PAM implementation
Translating Zero Trust principles into a functioning PAM implementation requires a structured approach. The starting point is always a comprehensive audit of the existing identity landscape: every privileged account, human or automated, must be discovered, classified, and assessed against the principle of least privilege. Accounts that retain more access than their function requires should be immediately remediated.
From there, organizations should prioritize the implementation of Role-Based Access Control (RBAC) combined with JIT provisioning workflows. Credential vaulting, where privileged passwords and keys are stored in an encrypted, centrally managed repository rather than shared informally or stored in configuration files, eliminates one of the most common vectors for credential theft. Session recording provides forensic value after incidents and serves as a behavioral deterrent during normal operations.
A robust PAM implementation must also account for the full lifecycle of privileged accounts. This includes automated provisioning and deprovisioning tied to HR and organizational events, so that when an employee changes roles or leaves the organization, their privileged access is adjusted or revoked immediately. Too often, accounts persist long after the business justification for their privileges has expired, creating a growing inventory of dormant credentials that attackers can exploit.
Equally important is the investment in security culture and training. Technical controls are only as effective as the people who interact with them. Privileged users should receive targeted training on recognizing phishing attempts, handling credentials securely, and understanding the rationale behind access restrictions. An organization that deploys sophisticated PAM tooling but neglects to educate its administrators risks undermining its own defenses through human error.
Compliance considerations add urgency to this work. Frameworks such as NIST SP 800-207, ISO 27001, and regulatory standards like GDPR, NIS2, and PCI DSS all require demonstrable controls over privileged access. Automated audit logging, which PAM platforms can generate natively and forward to SIEM systems, directly supports compliance reporting and reduces the manual burden on security and legal teams.
Toward a continuous security discipline
The convergence of PAM and Zero Trust is not a one-time project with a defined endpoint. It is an ongoing operational discipline that must evolve in response to new threats, new technologies, and changes in organizational structure. As cloud-native architectures, containerized workloads, and AI-driven automation continue to reshape enterprise IT, the definition of what constitutes a “privileged account” will keep expanding, and so must the controls that govern it.
Organizations that treat PAM and Zero Trust as a living practice, continuously auditing their identity landscape, adapting policies to emerging risks, and investing in both technology and people, will find themselves significantly better positioned against attackers and in front of regulators. Those that treat it as a checkbox exercise will inevitably discover, often at the worst possible moment, that static defenses cannot withstand a dynamic threat environment.