Audit-Proofing your NIS2 training plan: a strategic guide
Why training is no longer optional
The NIS2 Directive (EU) 2022/2555 has fundamentally redefined what it means for a European organization to take cybersecurity seriously. Among its most significant shifts is the elevation of training from a recommended best practice to a binding legal obligation. Article 20 explicitly requires that management bodies of essential and important entities follow cybersecurity training, and encourages organizations to offer similar, regular training to their employees (a requirement further solidified by Article 21). This is not a formality. It is the normative foundation upon which the entire human layer of security now rests.

What makes this requirement particularly demanding is not its breadth, but its depth. Compliance is no longer satisfied by assigning an annual e-learning module and checking a box. Regulators, national supervisory authorities, and auditors now expect organizations to demonstrate that training is meaningful, measurable, and continuously updated. The standard has shifted from “did you train your staff?” to “can you prove the training worked, who received it, when, and how it aligned with your current threat landscape?”
The regulatory architecture: articles 20 and 21 as a combined mandate
Understanding how to structure a compliant training plan requires reading Article 20 and Article 21 together, not in isolation. Article 20 addresses governance and management accountability: board members and senior executives must personally undergo training to acquire sufficient knowledge to identify risks and assess cybersecurity risk-management practices. The personal liability dimension is crucial. Under NIS2, management can be held individually responsible for infringements, which transforms training from an HR matter into a boardroom imperative.
Article 21 then specifies the technical and organizational measures that entities must implement, listing “basic computer hygiene practices and cybersecurity training” as an explicit requirement within an all-hazards risk management framework. Training must be anchored to the organization’s broader risk posture, covering incident handling, business continuity, multi-factor authentication, backup procedures, and supply chain awareness. The two articles together make it clear that no training plan can be considered compliant if it operates as a standalone activity disconnected from risk assessment processes.
The financial stakes reinforce this reading. Essential entities face maximum fines of at least 10 million euros or 2% of global annual turnover (whichever is higher) for non-compliance, while important entities face maximum fines of at least 7 million euros or 1.4% of turnover (whichever is higher). These figures, combined with the possibility of personal liability for executives, make a defensible training program one of the most consequential investments an organization can make.
Designing a training plan that holds up under scrutiny
A compliant training plan is built on four pillars: scope, content, cadence, and evidence. Each one must be intentionally designed rather than assembled by default.
Scope determines who receives what. Not all employees carry the same risk exposure, and a well-structured plan acknowledges this through segmentation. The general workforce needs foundational cyber hygiene: recognizing phishing, using strong passwords and password managers, understanding how to report incidents, applying secure configurations, and practicing safe remote work habits. Mid-level management adds a layer covering incident response protocols, business continuity fundamentals, and an overview of NIS2 obligations relevant to their function. Senior management and board members require training specifically tailored to their legal obligations, risk oversight responsibilities, and the personal liability framework that Article 20 introduces. A training plan that fails to differentiate between these audiences is unlikely to survive a rigorous audit.
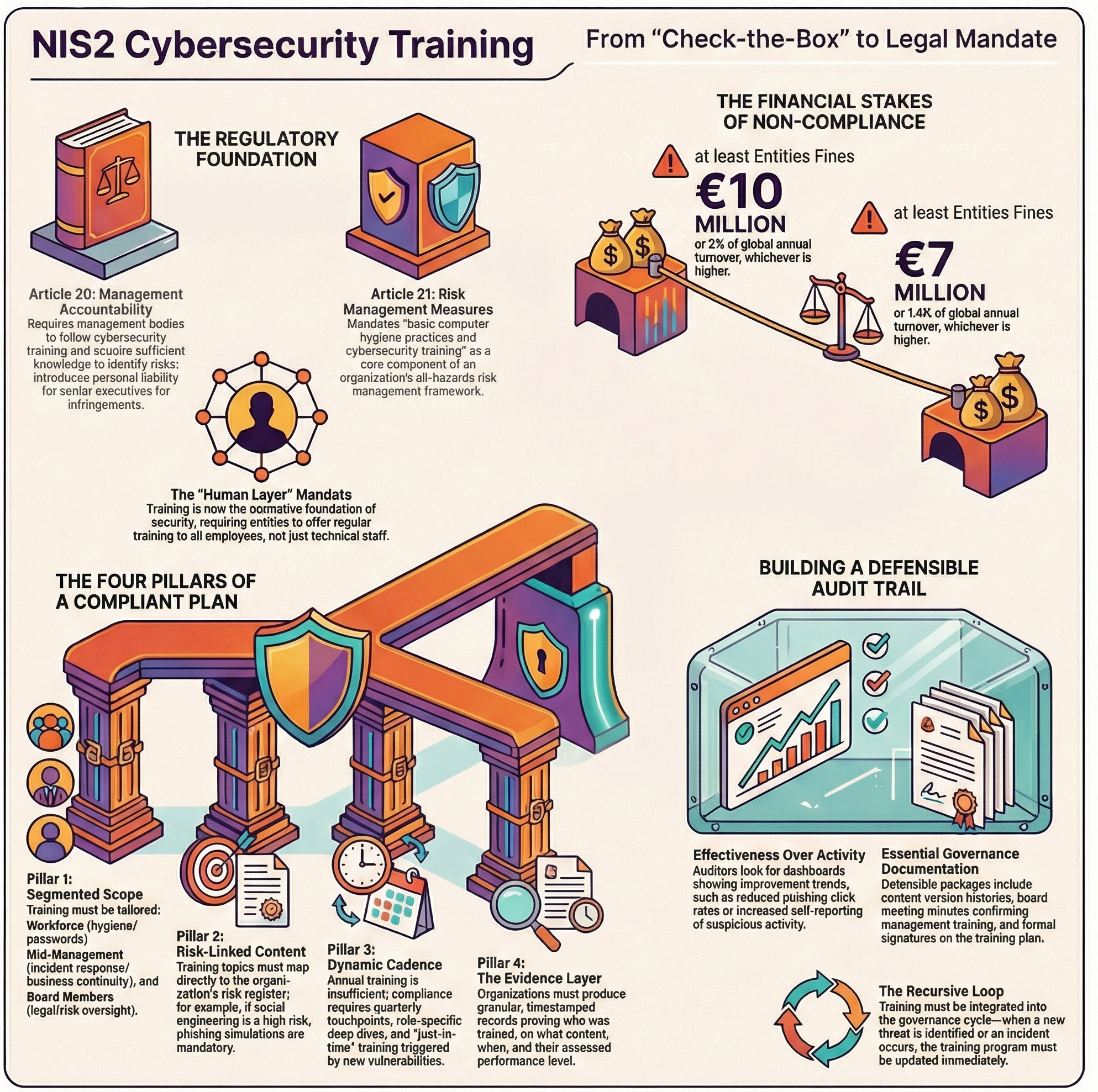
Content must map directly to identified risks. One of the most common gaps auditors identify is a mismatch between the threats documented in the organization’s risk register and the topics covered in its training modules. If a company has identified social engineering as a primary attack vector in its threat assessment, and its training program contains no phishing simulation or social engineering awareness module, that gap is an evidentiary liability. Content should be derived from the risk assessment, reviewed at least annually, and updated whenever the threat landscape shifts materially.
Cadence addresses the persistent misconception that annual training is sufficient. NIS2’s requirement for “regular” training implies a frequency calibrated to the pace of threat evolution and to the organization’s operational reality. Practical interpretations from national authorities and compliance frameworks suggest quarterly awareness touchpoints at minimum, supplemented by role-specific deep dives and just-in-time training triggered by incidents or newly discovered vulnerabilities. Phishing simulations, tabletop exercises, and live scenario walkthroughs are not optional embellishments; they are the mechanisms through which training transitions from passive consumption to active competency.
Building the evidence layer: what auditors actually want to see
The shift from policy-based assurance to evidence-based proof is perhaps the most operationally disruptive change NIS2 introduces. An auditor asking for proof of training compliance will not be satisfied by a list of employee names marked “completed.” What they require is granular, timestamped, exportable documentation that answers four specific questions: who was trained, what content they covered, when the training took place, and what their assessed performance was.
This means organizations need to invest in platforms or processes capable of producing this level of detail. Training records should include module-specific completion logs, assessment scores, remedial activity records for those who failed initial assessments, and separate documentation for management-level training that reflects their distinct obligations under Article 20. The ENISA technical implementation guidance reinforces that evidence must demonstrate not just activity, but effectiveness. Dashboards showing improvement trends in phishing simulation click rates, reductions in policy violation incidents, or increases in self-reported suspicious activity are the kind of data that demonstrate a living program rather than a dormant one.
Governance documentation must accompany training records to provide context. Version histories of training content showing how modules evolved in response to updated risk assessments, board meeting minutes confirming that management completed their mandated training, and formal approval signatures on the training plan itself are all components of a defensible evidence package. Without this layer, even an operationally excellent training program may fail to produce the compliance narrative an audit demands.
Making it defensible: the risk-linkage principle
A training plan is only as defensible as the logical chain connecting it to the organization’s formal risk management framework. Risk-linkage is the principle that transforms a training calendar into a compliance control. It means that every training topic can be traced back to a specific identified risk, that every update to the training curriculum is triggered by a documented change in the risk landscape, and that training outcomes feed back into the organization’s periodic risk reviews as measurable evidence of risk reduction.
In practice, this requires integrating the training program into the same governance cycle as the risk assessment. When a new vulnerability is identified, the training team receives a signal to assess whether existing content addresses it. When a sector-level threat intelligence report is published, relevant modules are reviewed for currency. When an incident occurs, post-incident analysis informs the next training iteration. This recursive loop is what compliance frameworks increasingly describe as the difference between a static program and a resilient one.
Organizations that build their training plans with this architecture, scope differentiated by role and risk, content anchored to threat intelligence, cadence calibrated to regulatory expectations, and evidence structured for auditability, are not simply meeting the minimum requirements of NIS2. They are building the kind of institutional security culture that the directive was designed to foster: one where cybersecurity awareness is not a compliance exercise, but an organizational capability embedded in daily operations and accountable at every level of the hierarchy.