Why Huawei USB stick setup on linux adds a strange "Huawei Autorun" script in system start?
"Huawei installed malware on my Linux laptop"? Let's calm down and try to collect more information!
Recently I've read an interesting article [1] published on "Sunburt Technology" blog:
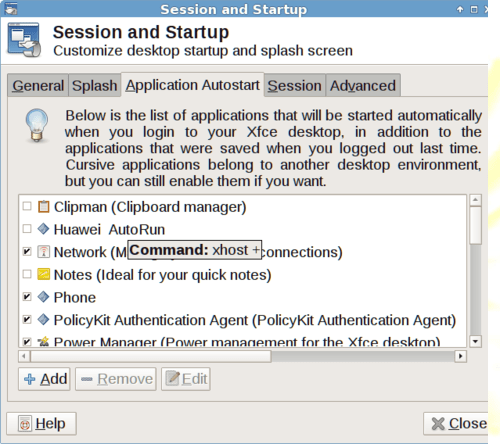
The screenshot above shows a script called "Huawei Autorun" which executes the command "xhost +" when you login. This command makes your Linux desktop remotely accessible to anyone on the network. The "Huawei Autorun" script appeared on my laptop after installing a Huawei E353 HSPA+ 3G USB stick (with serial number CE0682 on the back).
It seems like I dodged a bullet as I don't use the standard Linux GNOME desktop, so the script was not enabled, but the fact remains that Huawei installed malware on my Linux laptop.
Now, in my opinion, "Huawei installed malware on my Linux laptop" it’s a bold statement. However, why a modem installer needs to modify the system in order to allow X connection from any host?
In fact, the script is basically a one-liner embedded in an autostart launcher:
$ cat /etc/xdg/autostart/HuaweiAutoStart.desktop [Desktop Entry] Version=1.0 Encoding=UTF-8 Name=Huawei AutoRun Name[en_US]=Huawei AutoRun Exec=xhost + SwallowExec= SwallowTitle= Terminal=false TerminalOptions= Type=Application URL= X-KDE-SubstituteUID=false X-GNOME-Autostart-enabled=true GenericName[en_US]=
The script execute the command "xhost +" [2], that enables connection on local graphical interface from all hosts.
The install script needs to be installed as root so, it could drop some other script on filesystem.
I'm trying to get a similar device in order to analyze the install script.
References
- Huawei Hacked My Laptop
- xhost(1) - Linux man page